Use The Privilege
Windows is an operating system with security features. For example, one can specify which users can access a file.
There is a system for Discretionary Access Control (DAC), and one for Mandatory Access Control (MAC). DAC is implemented with Discretionary Access Control Lists (DACL) and MAC is implemented with privileges.
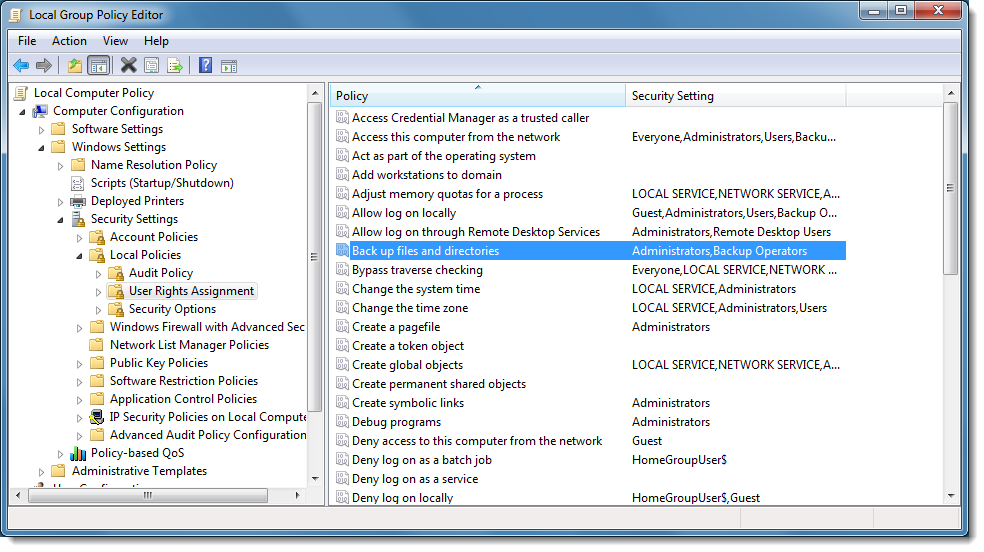
When access to an object like a file is controlled with a DACL, and this DACL does not grant you access, then you can try to get access via a privilege. The privilege you need to read this file (any file), is the backup privilege (SE_BACKUP_NAME). This backup privilege is given to members of the Administrator and Backup Operators group:
But as an administrator on Windows with UAC, you don't have this privilege in your restricted token. You need to elevate the process to have the privilege:
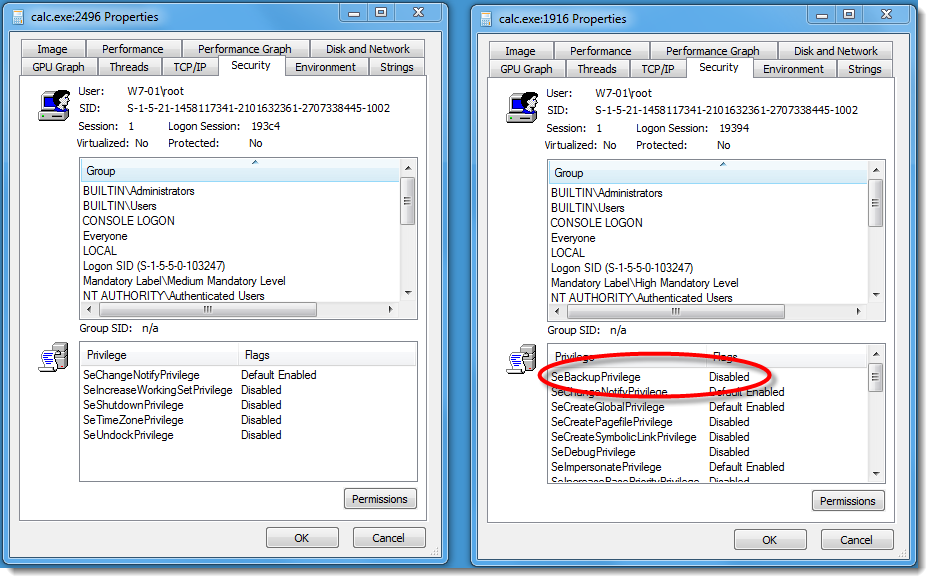
As you can see, you have the privilege, but it is disabled. It needs to be enabled programmatically (with API function AdjustTokenPrivileges):
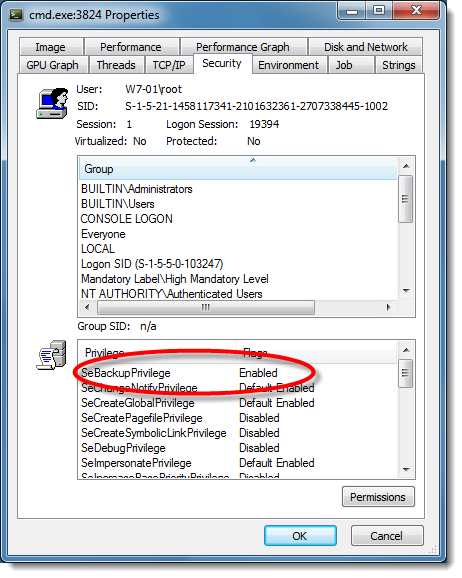
But that is not enough to give you read access to a file. On Windows, a typical way to read the content of a file is to use the API function CreateFile to create a handle for the file, and then use API function ReadFile to read the content of the file via that handle. To use your enabled backup privilege, you need to pass a flag to CreateFile that indicates that you want to use your backup privilege: FILE_FLAG_BACKUP_SEMANTICS.
Since this is not easy to script, it would be nice if you could to this with the command line processor cmd.exe. That's why I took ReactOS' implementation of cmd.exe and added a couple of commands and features to enable and use the backup privilege.

With my modifications, you can use the "privilege" command to enable the backup privilege, and then "copy" or "type" a file. I also added an "info" command. Remark: "cd" does not use the privilege.
Here is a video showing these commands:
Didier Stevens
SANS ISC Handler
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com
IT Security consultant at Contraste Europe.



Comments
Or: those who don't understand Windows have to reinvent it, poorly.
Everybody can use unmodified CMD.EXE or EXPLORER.EXE to access "\System Volume Information" and the files stored there after enabling SeBackupPrivilege for the respective instance of the command processor or Windows Explorer.
To do this, write a simple Win32 program which determines its parent process, opens the parent process for PROCESS_QUERY_INFORMATION, then opens the parent process' token for TOKEN_ADJUST_PRIVILEGES and finally calls TokenAdjustPrivilege.
Now run this program from any instance of the command processor or Windows Explorer
Works since the last millennium...
Anonymous
Apr 15th 2016
9 years ago