Traffic Analysis Quiz: Ugly-Wolf.net
Introduction
It's that time of the month again... Time for another traffic analysis quiz! This one is from a Windows 10 client logged into an Active Directory (AD) environment. Details follow:
- LAN segment: 10.10.16.0/24 (10.10.16.1 through 10.10.16.255)
- Domain Controller: Ugly-Wolf-DC at 10.10.16.6
- Gateway: 10.10.16.1
- Broadcast address: 10.10.16.255
The pcap and alerts are available on my Github repository at:
- https://github.com/brad-duncan/pcaps-for-ISC-diaries/blob/main/2020-10-15-ISC-traffic-analysis-quiz.pcap.zip (3,711,761 bytes)
- https://github.com/brad-duncan/pcaps-for-ISC-diaries/blob/main/2020-10-15-ISC-traffic-analysis-quiz-alerts.zip (4,273,268 bytes)
The zip archives are password-protected with the term: infected
The alerts archive contains an image of alerts and a text file with the same information.
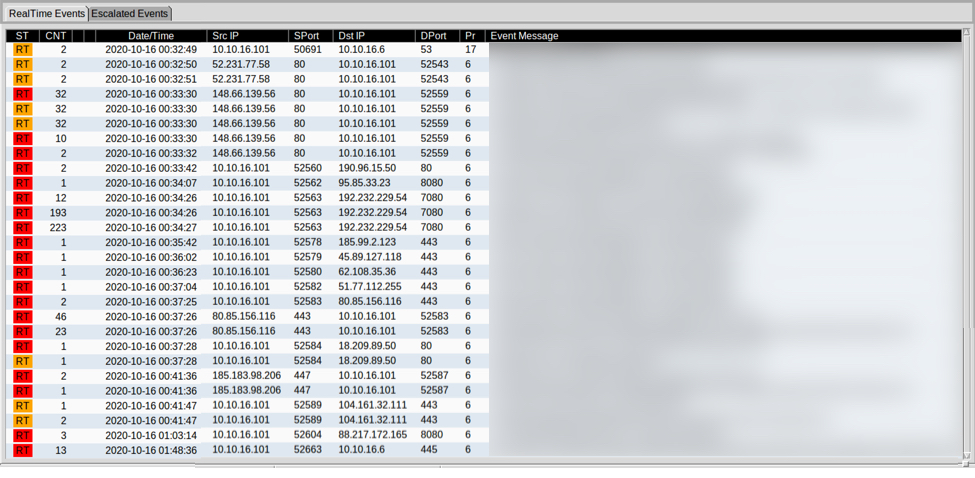
Shown above: Alerts image for this quiz, with the alerts blurred (you'll have to download the alerts file to see them).
The alerts file was created using Security Onion running Suricata using the EmergingThreats Pro ruleset, and the alerts were viewed using Sguil.
The alerts should give away the type of infection(s) happening on the Windows computer at ugly-wolf.net. Since this is an AD environment, you should also be able to find the user account name that was logged into the Windows host before it became infected. In a real-world situation, this could help you track down an infected user and perform incident response actions.
You can also use this quiz to practice drafting an incident report.
If the answers are not obvious, feel free to leave a comment in the comments section, and I'll answer when I get the time.
---
Brad Duncan
brad [at] malware-traffic-analysis.net



Comments
Anonymous
Oct 23rd 2020
4 years ago
These won't show up as whatever the "filename" line shows from the HTTP response headers.
Hope this helps.
Anonymous
Nov 10th 2020
4 years ago