More Malspam pushing Emotet malware
Introduction
I published a diary on malicious spam (malspam) pushing Emotet back in June 2017 (link). Since then, I continue to catch the occasional sample, and this malspam appears to occur on a near-daily basis.
Emotet is generally known as a banking Trojan, and TrendLabs published a good write-up earlier this month on some recent samples.
Emotet is not exactly big news, nor is it a new threat. Instead, it's another ongoing presence in our current cyber threat landscape. Emotet malspam bears some discussion, because it's a continuing concern. Therefore, today's diary examines recent malspam pushing Emotet on Wednesday 2017-11-29.
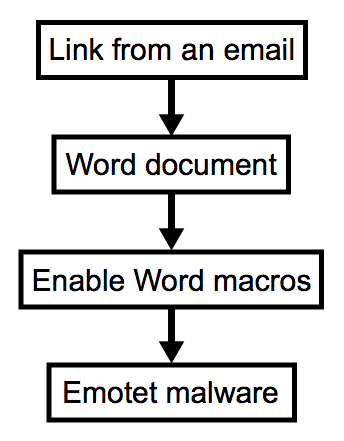
Shown above: Chain of events this malspam.
Emails
Malspam pushing Emotet occurred throughout the day on Wednesday 2017-11-29. As usual, these were invoice-themed emails. They came from different mail servers, each had different sending addresses, and the URLs occasionally changed. I collected 30 emails and saw 19 different URLs to download a fake invoice for the malware.
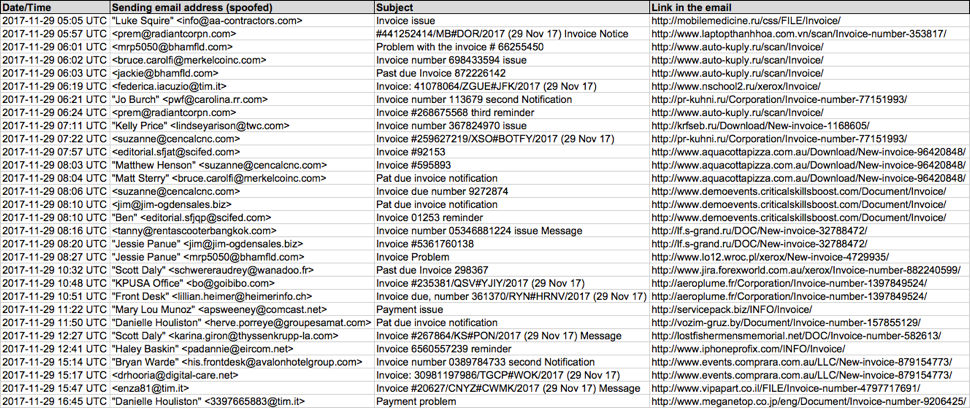
Shown above: Screenshot of a spreadsheet used to track this malspam.

Shown above: Screenshot from one of the emails.
Clicking on the links in these emails returned a Word document disguised as an invoice. These documents had malicious macros designed to infect a victim's host with Emotet malware.
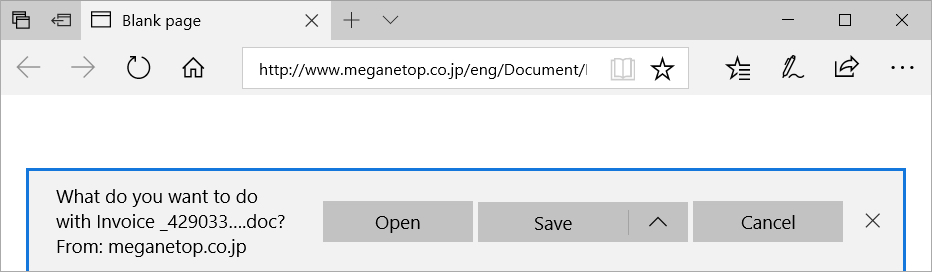
Shown above: Clicking on a link from one of the emails.
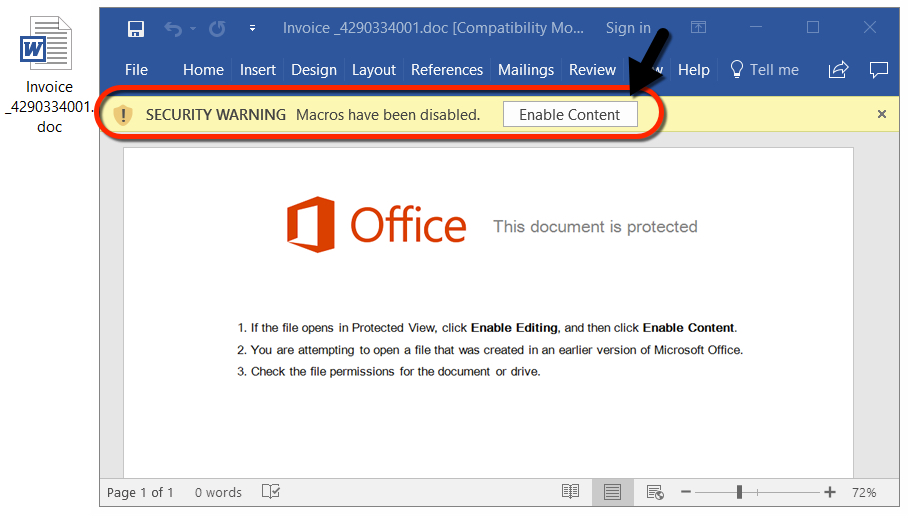
Shown above: Example of a Word document with the malicious macro.
Network traffic
I generated two infections from this malspam. The first was at 19:34 UTC, and the second was at 22:22 UTC. In both infections, I saw an HTTP GET request for the initial Word document, followed by another HTTP GET request after enabling the Word macros to retrieve the Emotet binary.
During the second infection, the original URL to retrieve the Emotet binary had been taken off-line, so additional HTTP GET requests were seen.
After the Windows host was infected, I saw HTTP POST requests on a non-standard port. This was post-infection callback traffic from the infected Windows host. During the first infection, this post-infection callback traffic used TCP port 7080. During the second infection almost three hours later, I saw HTTP POST requests over TCP port 443.
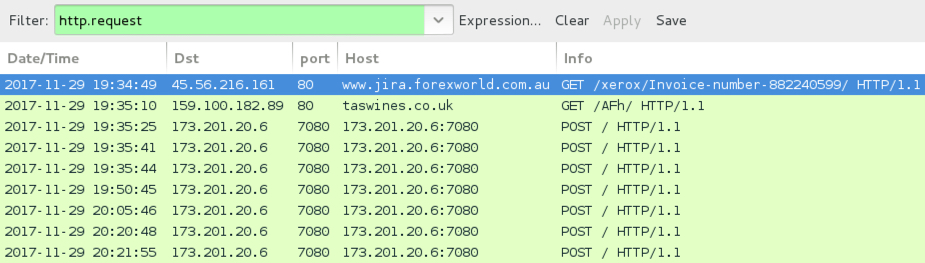
Shown above: The first infection at 19:34 UTC filtered in Wireshark.
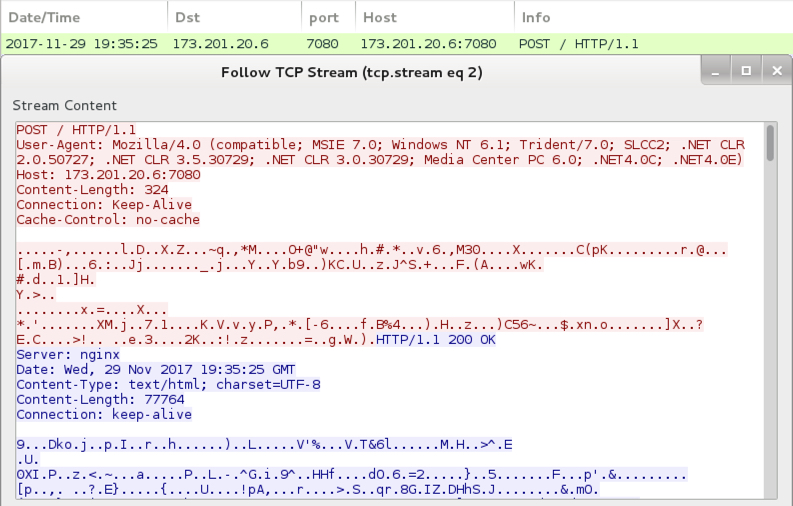
Shown above: Post-infection callback traffic from the infected Windows host.
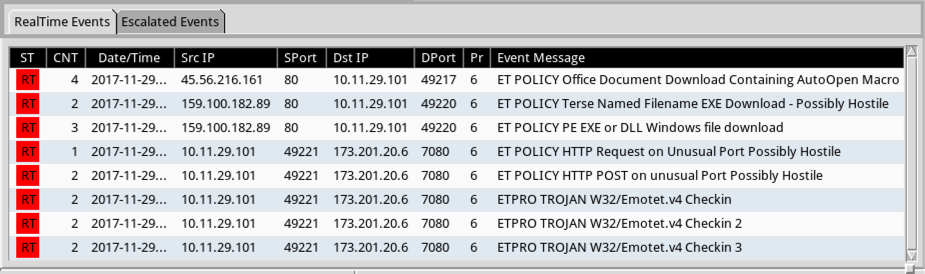
Shown above: Alerts on the infection traffic on Security Onion using Suricata with the Emerging Threats Pro (ET PRO) ruleset.
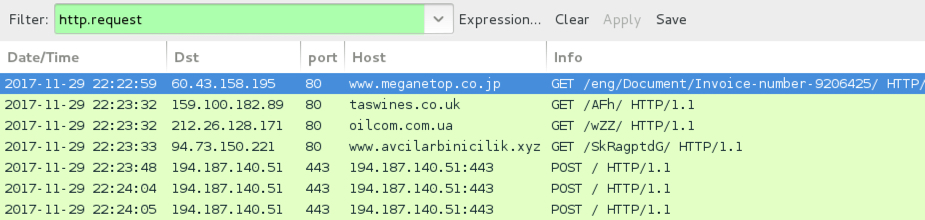
Shown above: The second infection at 22:22 UTC filtered in Wireshark.
Forensics on an infected Windows host
On a Windows 10 host, I had to disable Windows Defender. If not, the downloaded Word document was quickly detected as a severe threat. After I disabled Windows Defender, macros from the Word document retrieved an Emotet binary. However, my Windows 10 host didn't generate any post-infection traffic. I had to infect a Windows 7 host to get a full infection chain.
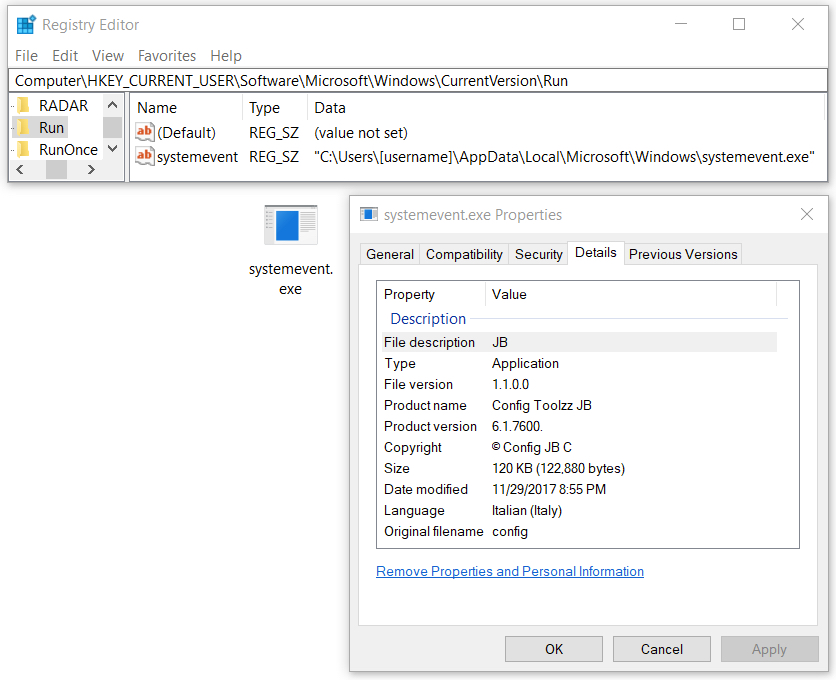
Shown above: Emotet malware made persistent on an infected Windows 10 host.

Shown above: Windows Defender detects this malware.
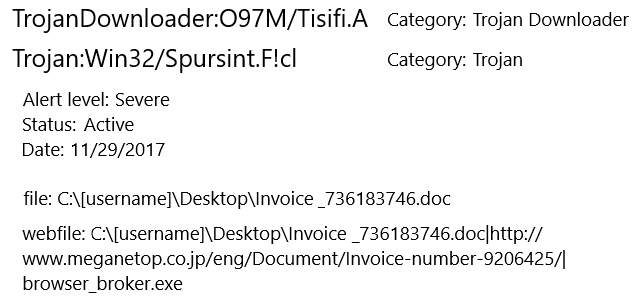
Shown above: Windows Defender catches the Word document.
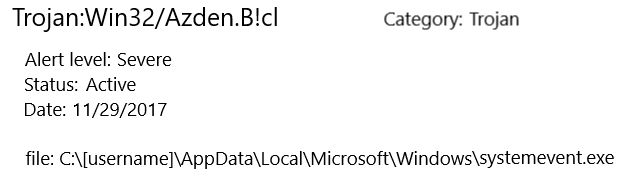
Shown above: Windows Defender catches the Emotet binary.
Windows Defender identified the Word document as TrojanDownloader:O97M/Tisifi.A and Trojan:Win32/Spursint.F!cl. Windows Defender identified the Emotet binary as Trojan:Win32/Azden.B!cl.
Indicators
The following are indicators of this campaign. Many of the domains represent legitimate websites that have been compromised, and they have been used to host malware for this campaign.
Links from the emails to download the Word document:
- aeroplume.fr - GET /Corporation/Invoice-number-1397849524/
- krfseb.ru - GET /Download/New-invoice-1168605/
- lf.s-grand.ru - GET /DOC/New-invoice-32788472/
- lostfishermensmemorial.net - GET /DOC/Invoice-number-582613/
- mobilemedicine.ru - GET /css/FILE/Invoice/
- pr-kuhni.ru - GET /Corporation/Invoice-number-77151993/
- servicepack.biz - GET /INFO/Invoice/
- vozim-gruz.by - GET /Document/Invoice-number-157855129/
- www.aquacottapizza.com.au - GET /Download/New-invoice-96420848/
- www.auto-kuply.ru - GET /scan/Invoice/
- www.demoevents.criticalskillsboost.com - GET /Document/Invoice/
- www.events.comprara.com.au - GET /LLC/New-invoice-879154773/
- www.iphoneprofix.com - GET /INFO/Invoice/
- www.jira.forexworld.com.au - GET /xerox/Invoice-number-882240599/
- www.laptopthanhhoa.com.vn - GET /scan/Invoice-number-353817/
- www.lo12.wroc.pl - GET /xerox/New-invoice-4729935/
- www.meganetop.co.jp - GET /eng/Document/Invoice-number-9206425/
- www.nschool2.ru - GET /xerox/Invoice/
- www.vipapart.co.il - GET /FILE/Invoice-number-4797717691/
Traffic generated by the Word macros to download the Emotet binary:
- 159.100.182.89 port 80 - taswines.co.uk - GET /AFh/
- 212.26.128.171 port 80 - oilcom.com.ua - GET /wZZ/
- 84.73.150.221 port 80 - www.avcilarbinicilik.xyz - GET /SkRagptdG/
Post-infection traffic generated by the Emotet malware:
- 173.201.20.6 port 7080 - 173.201.20.6:7080 - POST /
- 194.187.140.51 port 443 - 194.187.140.51:443 - POST /
SHA256 hash: 7bdf7722115be910e2b301b3f6b3037bc4b987c588838cd2459aeeeec9f50be7
- File size: 175,104 bytes
- File name: Invoice _[random string of numbers].doc
- File description: Word document with malicious macros to install Emotet
SHA256 hash: 315e536e86e7e280a2e5eb11fb53727c44d9fd7d76310cd77a1cbedcac9aff4e
- File size: 122,880 bytes
- File location: C:\Users\[username]\AppData\Local\Microsoft\Windows\shedulecart.exe (on a Win 7 host)
- File location: C:\Users\[username]\AppData\Local\Microsoft\Windows\systemevent.exe (on a Win 10 host)
- File description: Emotet binary (1st run)
SHA256 hash: 9fd6ccc50440cac2b76c4c99fcc6144555bd7e62eda22d66a3e9806a5358a686
- File size: 117,248 bytes
- File location: C:\Users\[username]\AppData\Local\Microsoft\Windows\shedulecart.exe (on a Win 7 host)
- File location: C:\Users\[username]\AppData\Local\Microsoft\Windows\systemevent.exe (on a Win 10 host)
- File description: Emotet binary (2nd run)
Final words
Malspam pushing Emotet is easily caught by any decent spam filter, and the associated malware is easily caught by any decent anti-virus. Windows 10 hosts seem well-protected against this threat. I had to set up a vulnerable Windows 7 host to get a full infection chain.
This malspam campaign cannot be very effective, yet it occurs practically every day. That's a testament to how cheap and easy it is to establish these campaigns. The Internet contains an endless supply of poorly-configured servers ripe for compromise by criminals looking to spam victims with malware. There's obvious a return on this type of investment, because we continue to see such malspam.
As always, on versions of Windows prior to Windows 10, system administrators and the technically inclined can implement best practices like Software Restriction Policies (SRP) or AppLocker to prevent these types of infections.
Emails, pcaps, and malware samples for today's diary can be found here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net



Comments