SSH Password Brute Forcing may be on the Rise
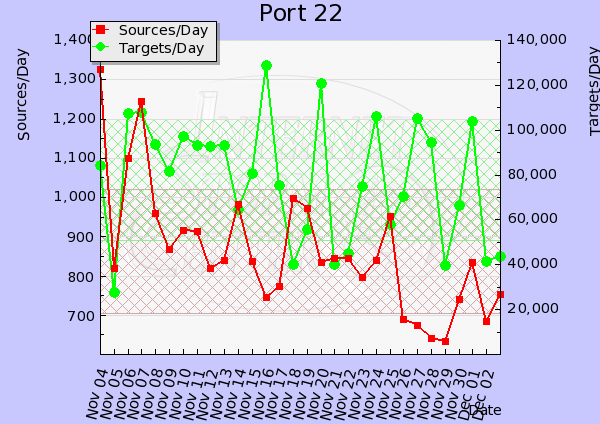
We have received a report of ongoing SSH account brute forcing against root. This activity has been ongoing for about a week now from various IPs. I have also noticed similar activity against one of my server ongoing since mid November from different IPs. A review of the DShield data, shows a spike can easily be observed starting 15 Nov and has been up/down ever since.
I got this report on the 2011-11-27 from one IP that ran over 2000 attempt to "break-in"
Source Port List Count
xx.yyy.209.73 -> 22 2025
Some Defensive Tips (Thanks Swa)
- Never allow root to log in, no matter what: always login in as a regular user and then use su/sudo as needed.
- Change port number: why go stand in the line of fire ?
- Disallow password authentication (use keys)
In addition to the above, you should also consider using TCP Wrappers with the SSH service to limit access to only those addresses that need access.
Another application that can also help protect your SSH service is fail2ban [1], it will ban IPs that makes too many password failures. It updates firewall rules to reject the IP address.
Have you been seeing similar activity?
[1] http://www.fail2ban.org/wiki/index.php/Main_Page
[2] ftp://ftp.porcupine.org/pub/security/index.html
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu



Comments
http://eromang.zataz.com/2010/05/15/suc015-potential-ssh-scan/
Regards
eromang
Dec 4th 2011
1 decade ago
Jeff
Dec 4th 2011
1 decade ago
llameadrpc
Dec 5th 2011
1 decade ago
http://honeypot.jayscott.co.uk/statistics/monthly/
The current months graph can be found on the main page:
http://honeypot.jayscott.co.uk/
Jay
Dec 5th 2011
1 decade ago
Just to add, I think the reason they download the WinXP SP3 patch is for testing bandwidth speeds, unless of course they then try to run it ;-)
Jay
Dec 5th 2011
1 decade ago
Al of Your Data Center
Dec 5th 2011
1 decade ago
Moriah
Dec 5th 2011
1 decade ago
Al of Your Data Center
Dec 5th 2011
1 decade ago
http://www.cipherdyne.org/fwknop/
joshlinx
Dec 5th 2011
1 decade ago