Help us figure this out: Scans for Apache "Nifi"
Please let me know if you have any idea what they are trying to do here :)
I noticed today that our honeypots detected a few scans for Apache "Nifi." Nifi is a Java-based system that allows for the routing of data. It will enable you to select data from a source (let's say from a CSV file) and output it to a database. Numerous sources and destinations are supported. Dataflows are created via a web-based GUI. One critical use case of Apache Nifi is to prepare and import data into machine learning systems.
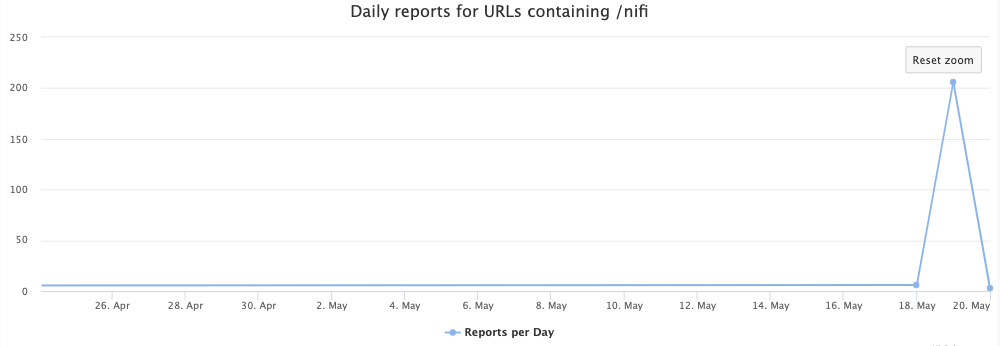
Today, I noticed a spike in requests for the URL "/nifi", the default URL used for the NiFi GUI.
Almost all the reports come from the same user-agent and IP address:
User-Agent: Go-http-client/1.1
Source IP: 109.207.200.43
The source IP, located in the Ukraine, has a history of scanning for various vulnerabilities, but nothing I would assign to a particular bot. Just "random" URLs like:
- /boaform/admin/formLogin
- blank.org:443
There are a couple other IPs and User-Agents used to scan for Nifi:
65.154.226.171 - Claiming to use headless chrome on Linux and Chrome on Windows. Reasonably recent versions so they may be real user agents.
205.169.39.250 - Claiming to use Chrome, but ancient versions so I assume these user agents are fake
Both of these IPs are part of Qwest/CenturyLink/Lumen. 65.154.226.171 at least used to be part of Paloalto.
But the real question: What are they looking for? Trying to steal data from badly secured NiFi installs? Poisoning ML data? cryptomining... ? There isn't a vulnerability that I would consider, other than bad configurations with no/weak/default passwords.
Let me know if you use NiFi, and if you have an idea what they may be looking for.
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|
| Application Security: Securing Web Apps, APIs, and Microservices | Las Vegas | Sep 22nd - Sep 27th 2025 |



Comments
WwrdPldn
May 23rd 2023
2 years ago
I also had the 109.207.200.43 show up on logs for blocked connection attempts to udp port 500, on my home network.
hope this helps,
- Nick
Nick
May 25th 2023
2 years ago
ProfADWLoyno
May 26th 2023
2 years ago