Downloader Disguised as Excel Add-In (XLL)
At the Internet Storm Center, we like to show how exotic extensions can be used to make victims feel confident to open malicious files. There is an interesting webpage that maintains a list of dangerous extensions used by attackers: filesec.io[1]. The list is regularly updated and here is an example of malicious file that is currently not listed: "XLL". It's not a typo, it's not a "DLL" but close to!
An "XLL" file is a Microsoft Excel add-in that is indeed a DLL but when launched, it will be loaded into Excel and executed. The default icon makes it looks like non suspicious:
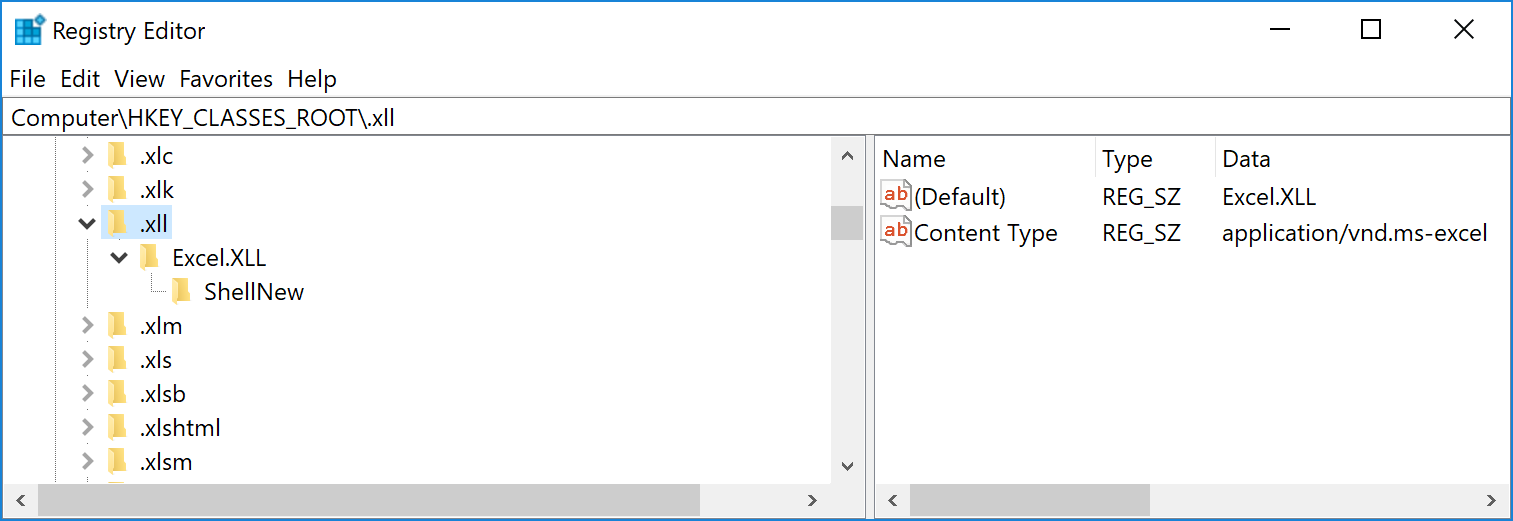
When you've Microsoft office installed, the file extension is linked to Excel, a double-click on it will spawn it:
Like VBA macros, Microsoft implemented[2] this for legit reasons:
"The primary reason for writing Microsoft Excel XLLs and using the C API is to create high-performance worksheet functions. The applications of high-performance functions—and, starting in Excel 2007, the ability to write multithreaded interfaces to powerful server resources—make it a very important part of Excel extensibility. The performance of XLLs was further enhanced in Excel 2007 by the addition of new data types and, most important, support for multithreading."
But, when a feature is available, attackers will try to abuse of it. Because it's a DLL, it has an exports table: xlAutoOpen(). It's the exported function that will be called by Excel once the DLL loaded. We have now all the components required to execute malicious code:
- A "non-suspicious" file
- Linked to a trusted app
- Automatic load and jump to executable code
Note: Like VBA macros, Excel will ask you the authorization to load the add-in.
The sample that I found was 64-bits code and I had only a 32-bits version of Excel in my malware analysis lab (note to self: install the 64-bits version of Microsoft Office), impossible to perform live analysis. One of my prefered tool to quickly extract encoded strings from a PE file is floss. No need to go deeper, it successfully decoded all we need to understand the behaviour of the DLL:
LoadLibraryW kernel32 etProcAddress ExpandEnvironment tringsW URLDownloadToFileW GetStartupInfoW CreateProcessAsUserW T$PH T$HH %APPDATA%\msoffice.exe UrlMon hxxp://3[.]126[.]250[.]38/FH/CAT/DHL2020386.exe T$tH ExitProcess t=f; u$E+J
The second stage payload (DHL2020386.exe) is a Formbook trojan[3]. If you are interested into the XLL file, I uploaded it on Malware Bazaar[4].
[1] https://filesec.io
[2] https://docs.microsoft.com/en-us/office/client-developer/excel/developing-excel-xlls
[3] https://www.virustotal.com/gui/file/5aad7a3f3d55c4741d8a79b59e0e9f922d375adab9f998ababc03a88a2feb27c
[4] https://bazaar.abuse.ch/sample/f00154ced8148e4866340673268f47b9b41b53925410e6e45ba75140652dfcaf/
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
| Reverse-Engineering Malware: Advanced Code Analysis | Online | British Summer Time | Jul 28th - Aug 1st 2025 |



Comments