An Alternative to Shodan, Censys with User-Agent CensysInspect/1.1
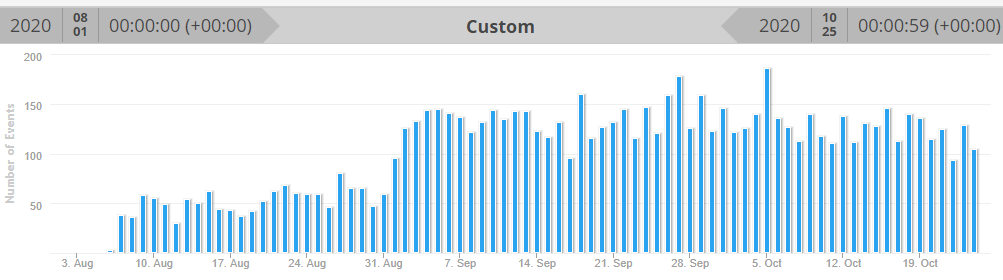
I have well over 2 years of honeypot logs and only started seeing CensysInspect user-agent in my logs about 2 months ago. Most of us are familiar with Shodan and often use it to find what is or was exposed to the Internet. This is an alternative site to search the same data with 3 available search options, by IPv4, websites and certificates.
This is an example of what can be seen in webserver logs:
20201024-071114: 192.168.25.9:80-167.248.133.52:54072 data 'GET / HTTP/1.1\r\nHost: 70.50.xx.xx\r\nUser-Agent: Mozilla/5.0 (compatible; CensysInspect/1.1; +https://about.censys.io/)\r\nAccept: */*\r\nAccept-Encoding: gzip\r\n\r\n'
Planning to do more than 10 queries per day, you need to register, it is free and check this page that show examples on how to to query de data.
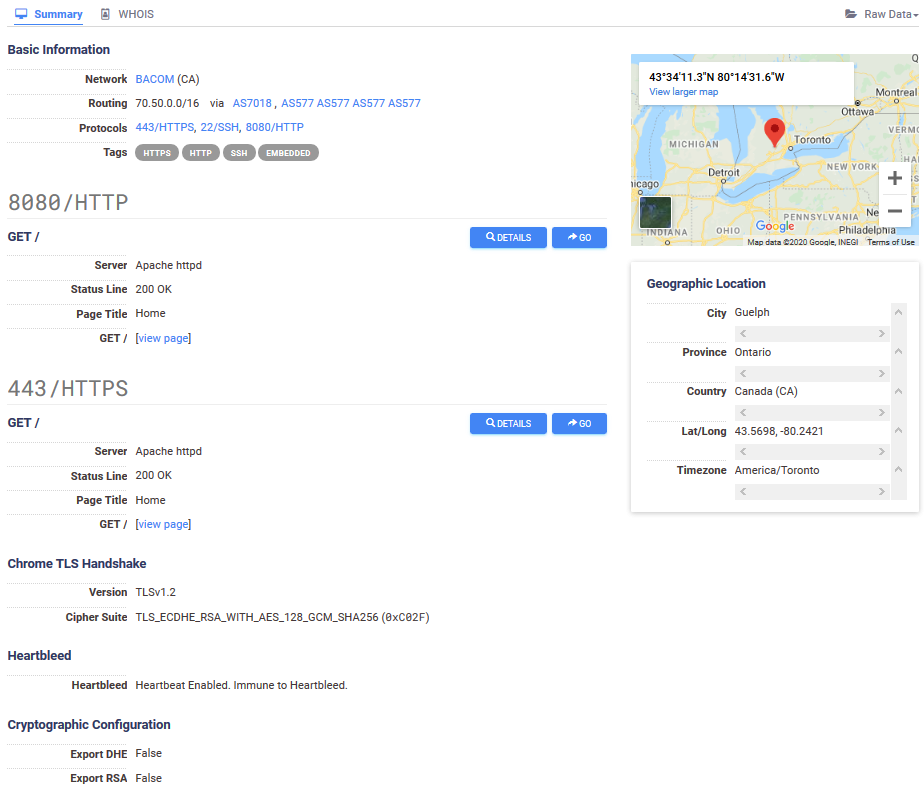
This scanner works by grabbing banner and collecting all information being leaked by insecure devices which get categorized and stored for "research" purposes. According to their FAQ, it uses Zmap which "[...] can scan the entire public IPv4 address space in under 45 minutes." and uses "ZGrab can perform a TLS connection and collect the root HTTP page of all hosts ZMap finds on TCP/443." The information captured is like what Shodan provides:
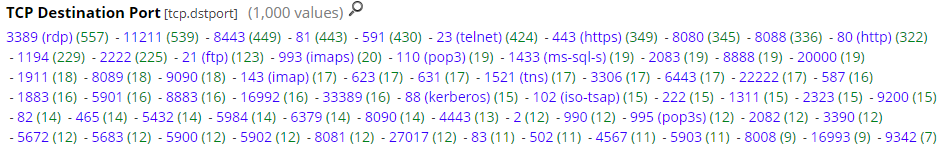
This is an alternative to find Internet-facing systems, finding open ports and services that listen on a port. Censys probes for more than just the standard known ports. This is some of the ports starting with the top (total in 2 months > 1000 ports).
IP Ranges included in the probes:
74.120.14.33-74.120.14.52
162.142.125.23-162.142.125.57
167.248.133.33-167.248.133.52
192.35.168.193-192.35.168.251
[1] https://censys.io
[2] https://www.shodan.io
[3] https://censys.io/ipv4/help
[4] https://support.censys.io/hc/en-us/articles/360038378552-Frequently-Asked-Questions-FAQ
[5] https://zmap.io
[6] https://isc.sans.edu/ipinfo.html?ip=167.248.133.52
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu



Comments