rockNSM as a Incident Response Package
Are you looking for a lightweight system to be part of your Incident Response kit? This is probably the package for you. It contains all the basic elements needed to capture data on the fly with Suricata, Bro, Logstash, Kibana, Elasticsearch and Kafka needed to conduct an investigation. Two options exist to get going to build your system, you can use the ISO built on CentOS 7.3 or built your own, and obviously I recommend using the ISO; make sure you check the hardware requirement before starting. "The system you run this on should have at least 2 network interfaces and more than 8GB of RAM, with an OS (RHEL or CentOS 7) already installed."[2] The current version is 2.0.5 and I recommend reading the release notes.
This kit can also be use in a small network (i.e. home is a perfect place for it) as a complete IDS package. The current version has a small issue, when installing via the ISO, make sure when you see an option to create an account that you create your own before continuing, otherwise you won't be able to login. After you complete the ISO installation, I recommend you run the following commands to complete the setup:
- sudo su -
- chown suricata:suricata /var/run/suricata
- /opt/rocknsm/rock/bin/generate_defaults.sh
- /opt/rocknsm/rock/bin/deploy_rock.sh
- rock_status (check if everything is working)
- rpm --import https://www.centos.org/keys/RPM-GPG-KEY-CentOS-7 (install PGP key)
- vi /etc/yum.repos.d/CentOS-Base.repo (gpgcheck and enable from 0 to 1)
- yum clean all && yum check-update
- yum update (Update all then reboot)
- yum install bind-utils (optional if you need nslookup or dig)
- http://IPADDRESS - to access Kibana (I recommand static address)
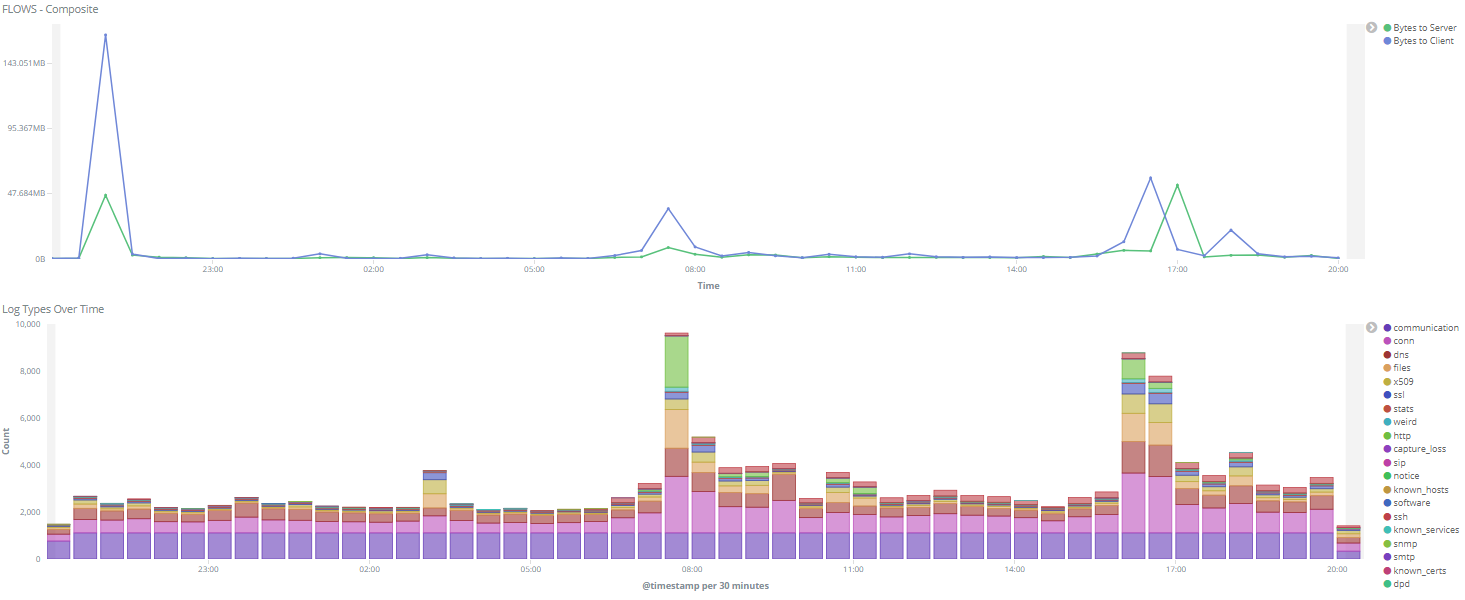
Check this page for additional information to troubleshoot the system. Overall easy to install (~20 minutes), easy to use and start traffic capture immediately. This is the output of the many Kibana dashboard displaying an overview over the past 24 hours of Bro capture.
[1] https://github.com/rocknsm/rock/releases/download/v2.0.5/rocknsm-2.0.5-1705.iso
[2] https://www.gitbook.com/book/rocknsm/rocknsm-guide/details
[3] https://github.com/rocknsm/rock/releases
-----------
Guy Bruneau IPSS Inc.
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments