iPhone worm in the wild
Couple of days ago there were a lot of discussions about an attack on iPhone users in the Netherlands where the attacker installed a backdoor that asked the iPhone owner to pay 5 EUR to get rid of the Trojan.
The attack was aimed exclusively against jailbroken (hacked) iPhones – these phones allow the user to run unofficial code and bypass Apple's official App Store. In other words – it allows users to run (often) pirated programs.
One of the problems with most jailbroken iPhones is that they run various services, including SSH among the others. The installation of SSH service is terribly insecure and, besides allowing remote root login, also leaves a default password on most jailbroken iPhones. This "vulnerability" was used by the hacked in the Netherlands and the same thing is exploited by the worm named iKee that was published today.
The worm is written in C and contains a lot of comments – one can see that the author was not the most experienced C coder but nevertheless he managed to get the worm to work.
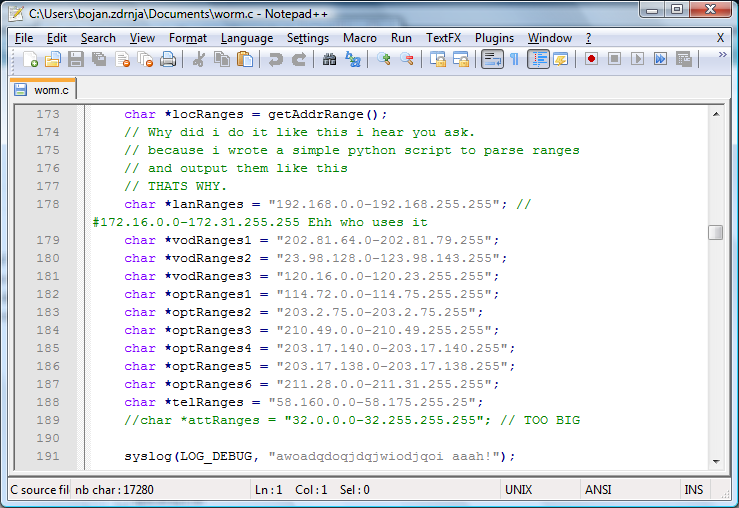
The worm is actually very, very simple. After execution it will scan certain IP addresses (you can see the list on the screenshot above). All IP addresses belong to 3G customers in Australia and are hardcoded in the worm. If an IP address is reachable, the worm uses a Cydia application to try to login to the IP address as root – it presumes that it is an iPhone since only 3G networks are scanned.
If the login was successful, the worm will copy several files (including itself) to the vulnerable iPhone, will kill SSH (so the phone can't be infected again or by a different attacker) and will change the background as well.
While this is maybe the first iPhone worm that was actually detected in the wild, and while it is very simple, it definitely highlights the risks of running unauthenticated code, something that a lot of people using hacked/jailbroken iPhones are not aware of. Similarly as not running a pirated version of an operating system on your machine, one should not try to evade security mechanisms implemented in phones, especially since they can contain a lot of sensitive personal information.
--
Bojan
INFIGO IS
| Web App Penetration Testing and Ethical Hacking | London | Mar 2nd - Mar 7th 2026 |


Comments
Ricardo F. Teixeira
Nov 8th 2009
1 decade ago
More info, and links to his MySpace/Twitter pages, here:
http://www.sophos.com/blogs/gc/g/2009/11/08/iphone-worm-discovered-wallpaper-rick-astley-photo/
Graham Cluley, Sophos
Nov 8th 2009
1 decade ago
rrittenhouse
Nov 10th 2009
1 decade ago
Mark
Nov 13th 2009
1 decade ago