XPS Attachment Used for Phishing
While Phishing is never a good thing, it is interesting to see something different than your normal phishing attempt. We received an email today from Earl Ruberts about an email their IT department received from a purchasing department of another company with which they have no relationship. The email contained an attachment that had a .xps extension. They conducted scans of the attachment that came back clean and the email did not appear to be spoofed. They contacted the company to ask them if they sent it and found out they were actively cleaning up an account compromise. Since the email and attachment was suspicious, Earl asked us to take a look. Here is the body of the email:
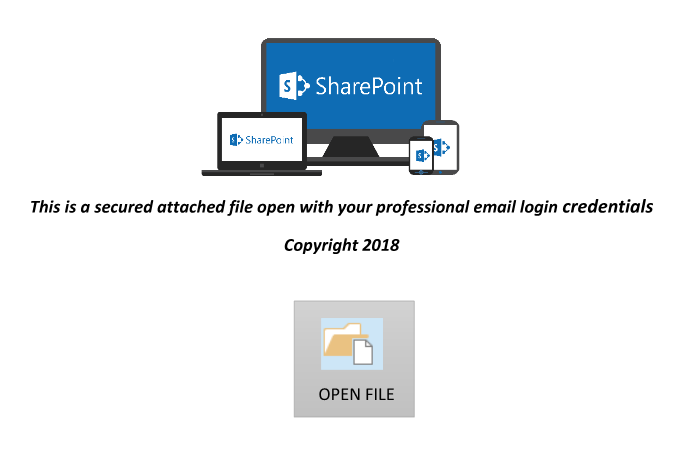
Using a VM, I took a quick look at the attachment in notepad and it showed a structure that looked like an XPS file. An XPS extension stands for "XML Paper Specification" and if like Microsoft's version of a PDF using XML. So, I used Microsoft's built-in XPS viewer to open the file. This was where the phishing came into play. Here is what you see when you render the file:
The phishing folks use the ploy of a "Secure attached file" in the XPS file since this is supposed to be a copy of a check and "Payment Advice" in order to convince the victim they are being careful with their check. Also, the SharePoint references would be convincing to people if asking them to retrieve files, since many businesses use SharePoint internally for this purpose. The average user would probably click on this. The "OPEN FILE" portion contains is a hyperlink to hxxps://areticaempresarial[.]com[.]br/microsoftsharepoint/share.php
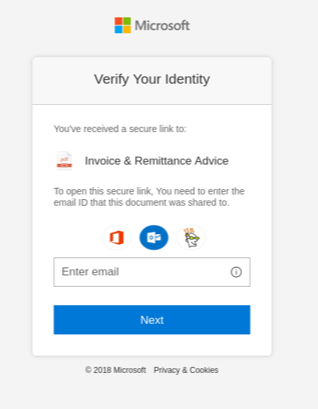
This again is continuing the ploy with use of "microsoftsharepoint" in the URLto help lure the victim into clicking. The URL is visible when you hover over it. If the user clicks the link, they are presented with the following screen:
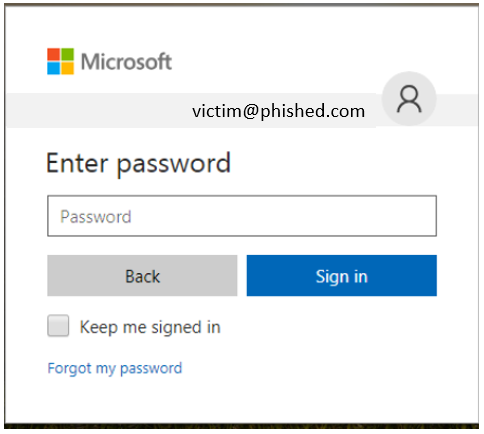
The user would then be asked for their password from a site with a nice Microsoft logo (It is SharePoint, right?) and if they followed the directions in the attachment, they would provide their "professional" email and password credentials.
It seems that we have a compromised account being used to send phishing emails in order to phish more account credentials from other victims. This could really reek havoc on partners of a company with a compromised account(s). I would venture to guess that is not all that the accounts are being used for or will be used for in the future. Also, an XPS isn't a file type that you see often today and probably isn't on the prohibited file extension list of most email gateways. It's a file extension that if you aren't actively using it internally and you don't expect to get that type of file in from external, I'd recommend blocking it on your email gateway. This is also a great example of how important it is to train your employees to be suspicious of unexpected emails and to not just click on everything!
Lorna Hutcheson
ISC Handler

.PNG)


Comments
Anonymous
Jun 22nd 2018
7 years ago