Sometimes it's a dud
A reader submitted a malicious RTF file, experiencing difficulty to find the malicious code.
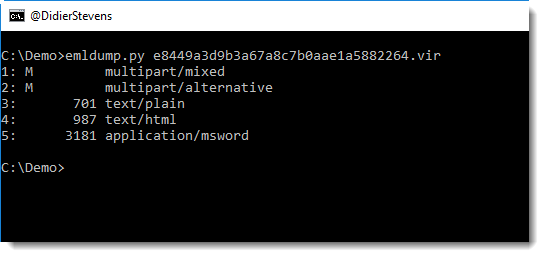
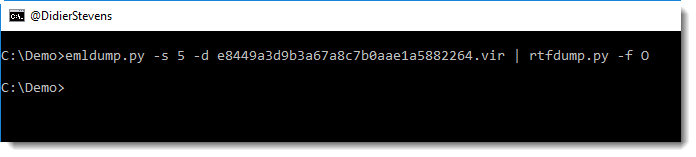
It was delivered via email, we analyze the file with emldump.py:
I've seen such emails before:
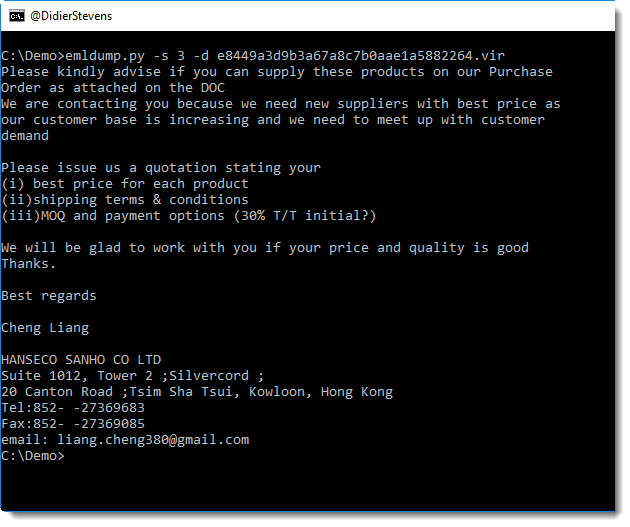
They typically have a malicious document as attachment.
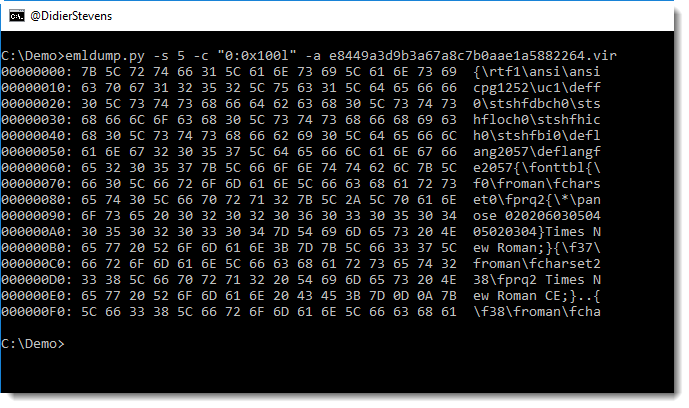
Here it's an RTF file:
We can analyze it with rtfdump.py:
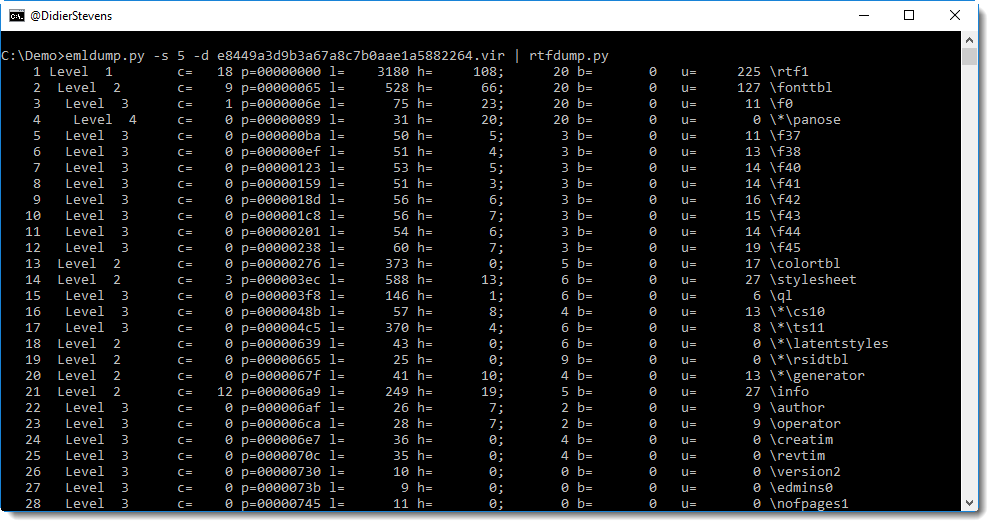
The RTF file has no objects:
It's always possible that objects are so obfuscated, that rtfdump.py is not able to identify them. So let's take a look at the amount of hexadecimal characters we can find in the RTF file:
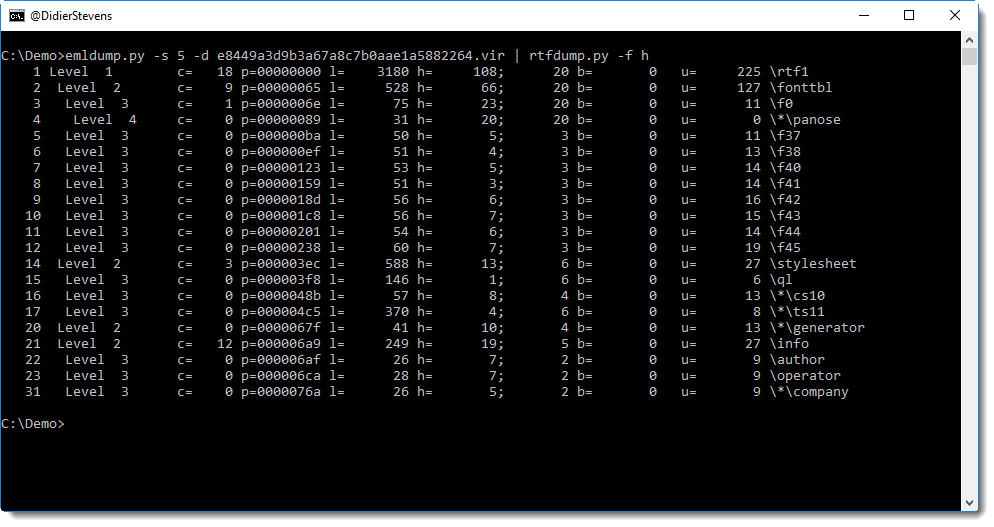
There's hardly any hexadecimal characters, the longest contiguous string of hexadecimal characters is just 20 characters long.
So this RTF file does not seem to contain malicious code. Looking at the file itself with a text editor, I came to the conclusion that it's just an empty RTF file (with metadata). With the metadata, I was able to find actual malicious RTF files produced by the same actor. So this must be a failed attempt at delivering malicious documents.
Didier Stevens
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com



Comments