How Victims Are Redirected to IT Support Scareware Sites
In the classic version of tech support scams, the fake technician initiated an unsolicited phone call to the victim. Now the awareness for this scheme has increased, scammers shifted tactics. Their latest approaches involve convincing the potential victim to be the one calling the impostor. I've seen this accomplished in two ways:
- Scammers use bots to respond to Twitter users who mention PC problems or malware. The bots search for the appropriate keyboards and send messages that include a phone number of a tech support firm. I described this approach when exploring how scammers prescreen potential victims.
- Scammers set up scareware websites that are designed to fool people into thinking their PC is infected, compelling visitors to call the fake tech support organization. Johannes Ullrich described a typo squatting variation of this technique in an earlier diary. Let’s take a look a domain redirection variation of this scam below.
In the following example, the victim visited a link that was once associated with a legitimate website: 25yearsofprogramming.com. The owner of the domain appears to have allowed its registration to expire in early 2014. At that point, the domain was transferred to Name Management Group, according to DomainTools Whois records. The record was assigned DNS servers under the domains cashparking.com, hastydns.com, dsredirection.com and eventually brainydns.com.
Name Management Group seems to own over 13,000 domains (according to DomainTools Whois records), including numerous domains that DomainTools classifies as malicious, such as 0357al.com, 18aol.com, 520host.com, 60dayworkout.us, 61kt.com, 7x24sex.net, 9tmedia.com, adobecrobat.info, adultfantasynetwork.com, allappsforpc.com, apkcracks.net, etc. (Don't visit these domains.)
Landing on the Fake Malware Warning Site
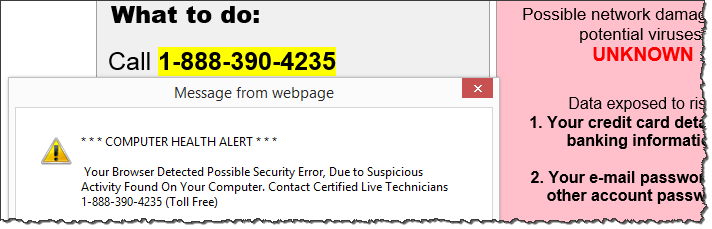
Visiting the once-legitimate URL a few days ago landed the victim on a scammy scareware page, designed to persuade the person to contact "Microsoft Certified Live Technicians" at the specified toll-free phone number. The site employed social engineering techniques employed by rogue antivirus tools. Such schemes present victims with fake virus warnings, designed to scare people into submission.
The site in our example also played an auditory message, exclaiming:
"This is a Windows system warning! This is a Windows system warning! If you are hearing this warning message, the security of your Windows system has been compromised. Your Windows computer and data might be at risk because of adwares, spywares and malicious pop-ups! Your bank details, credit card information, email accounts, Facebook account, private photos and other sensitive files may be compromised. Please call the number mentioned now to resolve this issue."
To see and hear what the victim experienced, play the video clip below or watch it on YouTube.
Here are the redirection steps that brought the victim to the scareware site mentioned above:
http ://25yearsofprogramming.com/blog/2010/20100315.htm -> https ://p2.dntrax.com/tr?id=f2d252736d65832f11811ad8cb43ceff00313e75.r -> http ://247tech.help/crt/us_seg0303/m1/us_windos_3806/index.html
You can see the source code to the final page on Pasebin, if you're interested. According to the code, it was mirrored from clients.worldnetconsultants.com/Lander3 using the free non-malicious tool HTTrack Website Copier on 08 Jan 2015. (More on this interesting tidbit in my diary
Who Develops Code for IT Support Scareware Websites?)
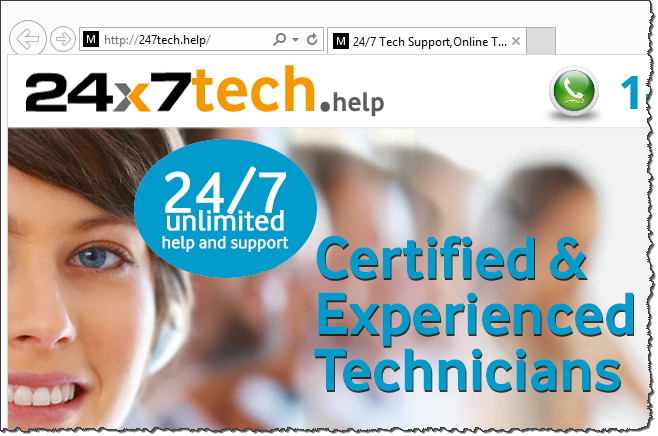
If you visited the top page of the 247tech.help website (don't go there), you would see a friendly, professional-looking page, gently inviting the visitor to "Call Now for Instant Support" by dialing 844-878-2550. Please don't call that number; however, if you'd like to hear a details account of what people experience when they do call, read my article Conversation With a Tech Support Scammer.
The nature of this page is in stark contrast to the scareware warnings-filled trap shown above, which redirection victims encountered.
Other Redirection Possibilities
The website hosting 25yearsofprogramming.com at the time of this writing redirects visitors to various places, perhaps randomly, perhaps based on the person’s geography or browser details. I encountered two other redirection flows that led to scareware websites set up for IT support scams.
One redirection flow employed p2.dntrax.com, as the example above, but took the victim to alert.windows.com.computers-supports.com (don't go there):
http ://25yearsofprogramming.com/blog/2010/20100315.htm -> https://p2.dntrax.com/tr?id=f2d252736d65832f11811ad8cb43ceff00313e75.r -> http ://alert.windows.com.computers-supports.com/index-1.html?isp=Time%20Warner%20Cable&browser=Internet%20Explorer&browserversion=Internet%20Explorer%2011&ip= 108.61.226.4&os=Windows&osversion=Windows%208.1
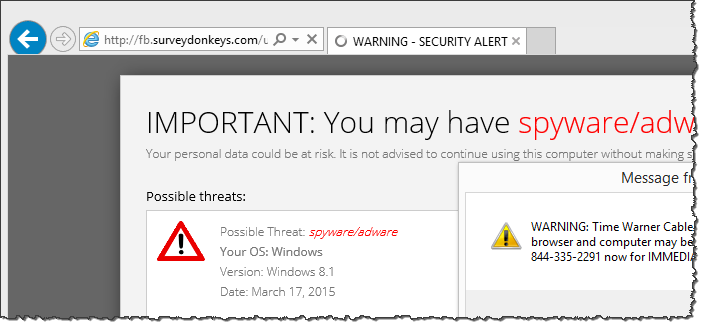
The resulting site is a bit more sophisticated than the one in the previous example, because it uses JavaScript to customize the web page to include the victim's ISP, browser name, IP address and Windows version. For instance:
document.write(getURLParameter('ip'))
You can see the source code of that page on Pastebin. Here's the screenshot of what the victim saw; in this example, the website didn't receive the victim's IP and other details and therefore didn't display this info:
Sometimes the victim was redirected using a longer trail to a different IT support scareware site (don't go there):
http ://25yearsofprogramming.com/blog/2010/20100315.htm -> http ://xml.revenuehits.com/click?i=cEuxzuX2fpc_0 -> http ://zh.zeroredirect1.com/zcvisitor/fddce3a1-ccbb-11e4-ab5a-0a92e2e12617 -> http ://claimyourfree.com/promo/base.php?c=734&key=0cdc58908ab3a694320034e391aa520a&target=oscar-vox-zKU0jhQu -> http ://fb.surveydonkeys.com/us/index.php?target=oscar-vox-zKU0jhQu -> http ://ajax.surveydonkeys.com/imp/g38a0n?data=eyJicm93c2VyX3R6X29mZnNldCI6LTI0MCwiY2IiOjEwNTExNSwibHBfcmVmIjoiIiwibHBfdXJsIjoiaHR0cDovL2ZiLnN1cnZleWRvbmtleXMuY29tL3VzL2luZGV4LnBocD90YXJnZXQ9b3NjYXItdm94LXpLVTBqaFF1In0= -> http ://securedgo.com/d3ed9240-61de-48c1-9a7b-b10dbafaa7d2 -> http ://fb.surveydonkeys.com/us/windowswarning.php?os=Windows&osversion=Windows%208.1&isp=Time%20Warner%20Cable&browser=Internet%20Explorer&voluumdata=vid..00000003-ee55-4287-8000-000000000000__vpid..48799800-ccb6-11e4-8c70-feaa7355a29a__caid..d3ed9240-61de-48c1-9a7b-b10dbafaa7d2__lid..5e47c857-460b-4d05-b92e-e24c030f0933__rt..R__oid1..b74614e1-7a0b-40bb-8bd5-66fbfc48a121
The redirection chain and the source code (you can see it on Pastebin) of the resulting site, as well as its look-and-feel were different from the examples above:
The design of this page matches closely the site Johannes Ullrich described in the typo squatting variation of this scenario on December 15. The latest page employed the sound file gp-msg.mp3 to scare visitors. VirusTotal has a record of this file, which was first uploaded to VirusTotal on December 11, 2014.
Who is Redirecting, Why and How?
We seem to be dealing with two different redirection engines and companies: p2.dntrax.com and xml.revenuehits.com after the initial 25yearsofprogramming.com redirect.
The domain dnstrax.com was registered by Team Internet AG, which is associated with over 44,000 domains, including several that DomainTools classifies as malicious: anonse24.de, natursteindichtstoff.de, seospecialists.de, etc. The domain revenuehits.com is registered to MYADWISE LTD, which is associated with about 50 domains.
The companies behind these servers, as well as the firm presently controlling 25yearsofprogramming.com are probably receiving referral fees for their roles in the redirection scheme.
There's much to explore regarding the domain names, systems and companies involved in the schemes outlined above. If you have additional information about these entities, or would like to contribute towards this analysis, please leave a comment. If you decide to explore any of these systems, do so from an isolated laboratory environment.
Also, if you encounter a tech support scam, please register it with our database of such incidents.
-- Lenny Zeltser
Lenny Zeltser focuses on safeguarding customers' IT operations at NCR Corp. He also teaches how to analyze malware at SANS Institute. Lenny is active on Twitter and Google+. He also writes a security blog.

Comments
I know, some will say "How dare you" and "web ads fund content" etc. Well, tough. I've caught more than one banner-ad service serving up malicious flash/java/javascript before or redirecting to an exploit kit landing page. And I've gotten to where I don't care if it was an accident or not or if the original banner ad they agreed to serve was benign or not. If I catch 'em sending my users to hostile content or even related to (or monetising) sites hosting hostile content, I'll drop 'em in my DNS filters and be done with them.
It's caused no complaints so far and seems to help at least a little...
Anonymous
Mar 20th 2015
9 years ago
Dear Cardmembership,
An attempt was made to login to your Account.
This attempt was blocked and for your protection we have disabled your account.
Please click the link below to activate your account:
Activate Your Account ==> 14.161.37.134/bbl.html (DO NOT USE ADDRESS!!!!!)
This is an automated message.Please do not reply to this email.
Thank you for your continued Card Membership.
Sincerely,
The American Express Customer Service Team
The headers.
Return-Path: <AmericanExpress@info.com>
Received: from xxxxxx-pub-iedge-vip.xxxxxx.rr.com
by XXXXXXX1.email.rr.com
(InterMail vM.8.04.01.13 201-2343-100-167-20131028) with ESMTP
id <>
for <>; Thu, 19 Mar 2015 23:11:44 +0000
Return-Path: <AmericanExpress@info.com>
Received: from [212.226.139.13] ([212.226.139.13:59831] helo=mail.registration.fi)
by cdptpa-iedge03 (envelope-from <AmericanExpress@info.com>)
(ecelerity 3.5.0.35861 r(Momo-dev:tip)) with ESMTP
id 26/8A-22105-0B75B055; Thu, 19 Mar 2015 23:11:44 +0000
Received: from localhost (localhost [127.0.0.1])
by mail.registration.fi (Postfix) with ESMTP id 7567942BB15E;
Fri, 20 Mar 2015 01:11:43 +0200 (EET)
X-Quarantine-ID: <g-sbUzdpmD-B>
Received: from mail.registration.fi ([127.0.0.1])
by localhost (mail.registration.fi [127.0.0.1]) (amavisd-new, port 10024)
with ESMTP id g-sbUzdpmD-B; Fri, 20 Mar 2015 01:11:43 +0200 (EET)
Received: from riikka (unknown [187.86.129.162])
by mail.registration.fi (Postfix) with ESMTP id 5B47C42BB156;
Fri, 20 Mar 2015 01:11:28 +0200 (EET)
Reply-To: <AmericanExpress@info.com>
From: "American.Express"<AmericanExpress@info.com>
Subject: Irregular Activity Detected XCYOXQUCXE
Date: Thu, 19 Mar 2015 20:11:34 -0300
MIME-Version: 1.0
Content-Type: text/html;
charset="Windows-1251"
Content-Transfer-Encoding: 7bit
X-Priority: 3
X-MSMail-Priority: Normal
X-Mailer: Microsoft Outlook Express 6.00.2800.1081
X-MimeOLE: Produced By Microsoft MimeOLE V6.00.2800.1081
Message-Id: <20150319231128.5B47C42BB156@mail.registration.fi>
To: undisclosed-recipients:;
X-RR-Connecting-IP:
X-Authority-Analysis: v=2.0 cv=WuCpwKjv c=1 sm=1 p=EeyebiKKAAAA:8 p=zwoigDAHFAr3muzOUH8A:9 p=Yfy1aCoo2AoA:10 p=tTD7qjiiRVwA:10 p=5BcD0ymsIHkA:10 a=61Z4K+ibLiJT6jLwhNwwdA==:17 a=Dyoqhi_TatcA:10 a=wPDyFdB5xvgA:10 a=rxA76bY6IJkA:10 a=Cfj4BQAnxiAA:10 a=v-Xpks9oaqIA:10 a=BqjLhEBqAAAA:8 a=emO1SXQWCLwA:10 a=SSmOFEACAAAA:8 a=Ft8UYL4EG9YA:10 a=_W_S_7VecoQA:10 a=C4PSEst5Od8A:10 a=1TM7i2lP1nUA:10 a=qiWi7Edwir4A:10 a=NWVoK91CQyQA:10 a=61Z4K+ibLiJT6jLwhNwwdA==:117
X-Cloudmark-Score: 100
X-EsetId:
Anonymous
Mar 20th 2015
9 years ago