Have You Ever Heard of the Fernet Encryption Algorithm?
In cryptography, there is a gold rule that states to not develop your own algorithm because... it will be probably weak and broken! They are strong algorithms (like AES) that do a great job so why reinvent the wheel? However, there are projects that try to develop new algorithms. One of them is Fernet[1], described like this:
Fernet guarantees that a message encrypted using it cannot be manipulated or read without the key. Fernet is an implementation of symmetric (also known as “secret key”) authenticated cryptography.
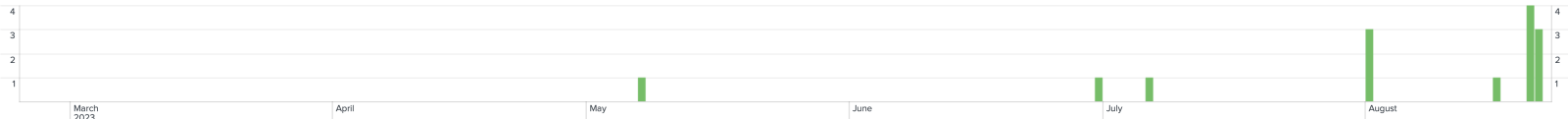
Fernet is available in many programming languages as a library/module/... one of them is, of course, Python[2]. The algorithm is not brand new and exists for years; the Python module has been last updated in 2016! I started to see some malicious scripts using Fernet to encrypt their payloads. I had a quick look at my hunting results and we can see a small trend starting across the last six months:
The usage of Fernet is pretty efficient. The last sample I detected has a VT score of 2/60! The script remains very simple:
import subprocess
creationflags = subprocess.CREATE_NEW_PROCESS_GROUP | subprocess.CREATE_NO_WINDOW
from fernet import Fernet
exec(Fernet(b'uSS2i-KrquUVErKGb1AFc7qQa695Aa_rae36i7Y9wUo=').decrypt(b'gAAAAABk26 ... oZUwkZW6TTIWcWnYoTExo=').decode('utf-8'))
But wait, Fenet is not installed by default in Windows Python environment. How to use it? Easy, just try to install it:
creationflags = subprocess.CREATE_NEW_PROCESS_GROUP | subprocess.CREATE_NO_WINDOW subprocess.Popen(['cmd.exe','/c','start','/b','pip', 'install', 'fernet'],creationflags=creationflags)
For the story, the decrypted and executed payload is an infostealer.
[1] https://github.com/fernet/spec
[2] https://pypi.org/project/fernet/
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key
| Reverse-Engineering Malware: Advanced Code Analysis | Online | Greenwich Mean Time | Oct 27th - Oct 31st 2025 |


Comments