Guidance to Protect DNS Against Hijacking & Scanning for Version.BIND Still a Thing
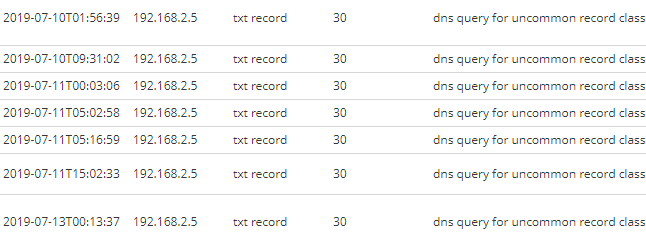
This type of scanning looking for vulnerable BIND server is nothing new and has been ongoing for pretty much the past 20 years. Checking what might be exploitable, the last BIND advisory was released less than a month ago [1] and is remotely exploitable. This is an example of observable BIND Version scanning that could seen in DNS logs.
Coming back to DNS, yesterday the UK National Cyber Security Centre (NCSC) released an alert to provide guidance against "DNS hijacking and mitigation advice"[3] because of a continued ongoing large-scale campaign to hijack DNS servers. The original alert published in January 2019 is available here which highlighted that DNS A (Address) and NS (Name Server) records where the main target for hijacking.
If you have DNS servers within your environment, have a look at the document provided by NCSC available here.
[1] https://kb.isc.org/docs/cve-2019-6471
[2] https://kb.isc.org/docs/cve-2019-6469
[3] https://www.ncsc.gov.uk/news/ongoing-dns-hijacking-and-mitigation-advice
[4] https://www.ncsc.gov.uk/news/alert-dns-hijacking-activity
[5] https://s3.eu-west-1.amazonaws.com/ncsc-content/files/Advisory-DNS-hijacking.pdf
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu



Comments