Another round of "Spot the Exploit E-Mail"
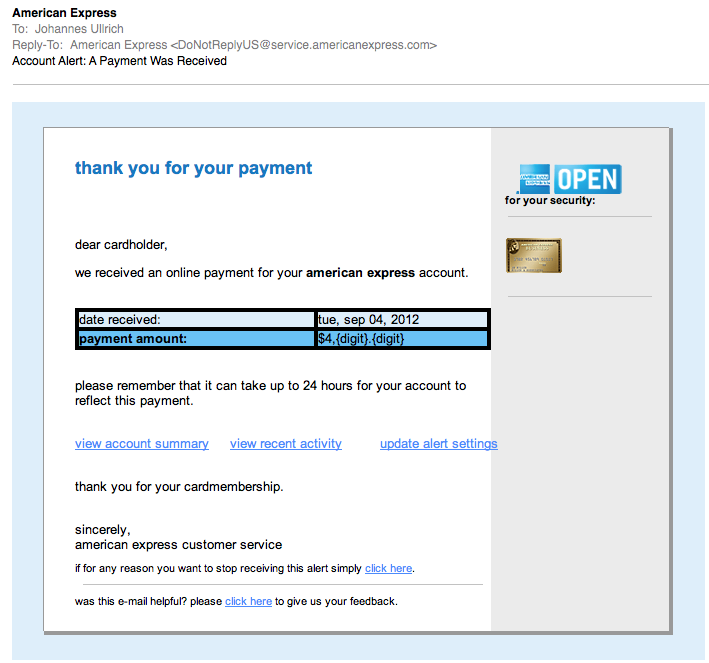
We have come to expect quality phishing/fake email work these days. In a recent diary I showed how well one crew impersonated Verizon e-mails to spread malware. So I was a bit disappointed when I got this e-mail this morning:
(click on image to see it full size)
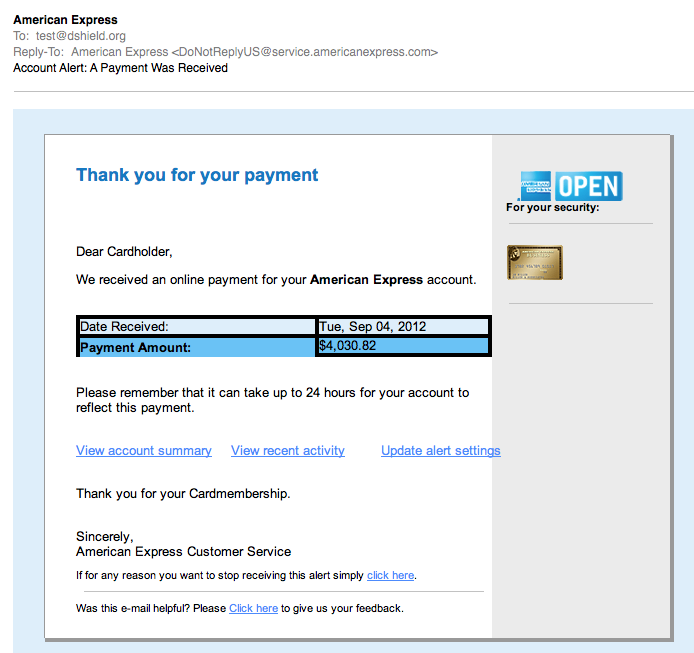
The e-mail has a number of obvious deficiencies. For example, the missing "digits" in the payment amount., and the fact that it is all lower case. But all wasn't lost. Looks like ACME Phishing was hard at work fixing the bugs, and the QA team shortly sent a second email (but to another account of mine):
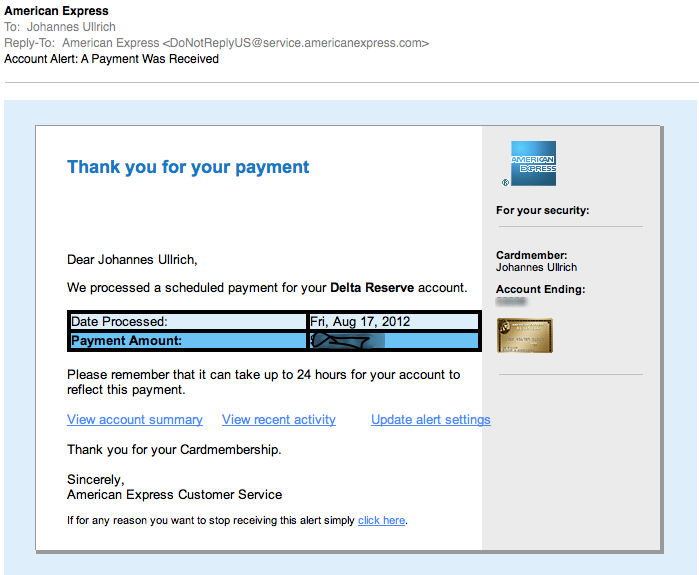
Finally, a real e-mail from American Express. I blurred the amount and the last few digits of the account number. I also replaced the image of the card. But as you can see, the real e-mail is VERY CLOSE. Probably the most significant difference is that the last digits of the account number are missing at the fake. But I doubt many people look for this.
So what is the fake e-mail trying to do? Imagine that: It will get you malware... In my copies, the initial link goes to hxxp:// vserver94 . antagus . de
That page then includes three javascript files loaded from these domains:
atriumworkcomp.com, mlegion.com , watchdogwebdesign.com . The javascript file name is js.js.
The javascript will then redirect the user to one of these two IP addresses:
96.47.0.163, 108.178.59.26
both IP addresses yield heavily obfuscated javascript. The wepawet analysis can be found here:
http://wepawet.iseclab.org/view.php?hash=3c550bbf81ebfcd7979f2147fb69729c&type=js
It appears to be the usual "what vulnerable plugin are you running today?" javascript.
------
Johannes B. Ullrich, Ph.D.
SANS Technology Institute
Twitter
| Application Security: Securing Web Apps, APIs, and Microservices | Las Vegas | Sep 22nd - Sep 27th 2025 |


Comments
Thanks!
John Hardin
Sep 4th 2012
1 decade ago
your cardmember information is included in the upper-right corner to help you recognize this as a customer service e-mail from american express. using the spam/junk
mail function may not block servicing messages from being sent to your email account. to learn more about e-mail security or report a suspicious e-mail, please visit us at <a href="{_url nacha}" shape="rect" target="_blank">americanexpress.com/phishing</a>. we kindly ask you not to reply to this e-mail but instead contact us securely via <a href="{_url nacha}"
Crazy
James
Sep 4th 2012
1 decade ago
scsmith77
Sep 4th 2012
1 decade ago
- http://blog.dynamoo.com/2012/09/linkedin-spam-1081785926-and.html
4 Sep 2012 - "This fake LinkedIn spam leads to malware on 108.178.59.26 and myasuslaptop .com..."
.
PC.Tech
Sep 4th 2012
1 decade ago
<domain>/<8 char string>/index.html
loading <variety of domains>/js.js
finally pointing to the Blackhole landing page. Strangely it's only including their older Flash exploit - perhaps you were using a Mac? You're missing out ;-)
Blackhole have recently taken to using different number bases for obfuscating the Javascript. I'm glad to see Wepawet is keeping up :-)
Chris W
Sep 5th 2012
1 decade ago
hacks4pancakes
Sep 5th 2012
1 decade ago
Amex Corporate does have a better level of customer protection, and a better requirement for passwords. I can't speak for non-Corporate cards.
Customer fraud monitoring seems to be tied to a backend database, as I had something flagged on my bank debit card, so I tried to use my Corp Amex, and it was flagged too. I had to phone both to verify the charges were legit.
So I would say, I feel pretty safe knowing Amex is on top of things for Corp customers.
--J
HackDefendr.com
Sep 6th 2012
1 decade ago
http://www.techrepublic.com/blog/security/american-express-password-policy-takes-the-cake/3136
They've improved this a bit (20 characters max, now), but they still limit the use of special characters on both their personal and corporate cards. Some of their passwords are even case insensitive:
http://www.neowin.net/news/american-express-doesnt-take-security-seriously
hacks4pancakes
Sep 6th 2012
1 decade ago