A Not So Well Done Phish (Why Attackers need to Implement IPv6 Now! ;-) )
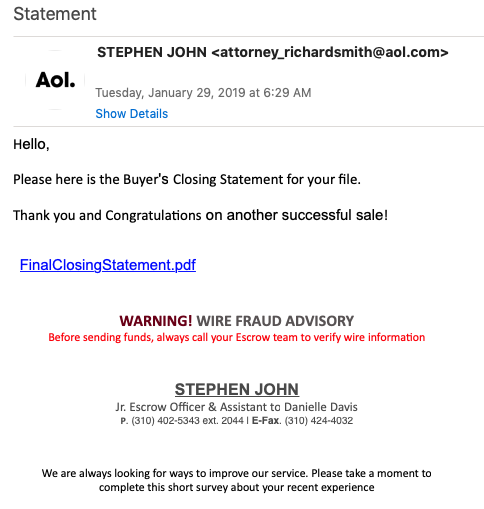
I got a little bit a better done Phish this morning:
Initially, I was interested in this because it looks like some of the other real estate related phishing/Business Email Compromise attacks I have seen in the past. The goal is to usually get a victims email credentials to later inject emails with fraudulent wire instructions. Many million dollars have been lost in these attacks in the past. I found it interesting that the attacker specifically requested to verify wire instructions via the phone.
So what do you do with a phishing email:
(1) Click on the link of course
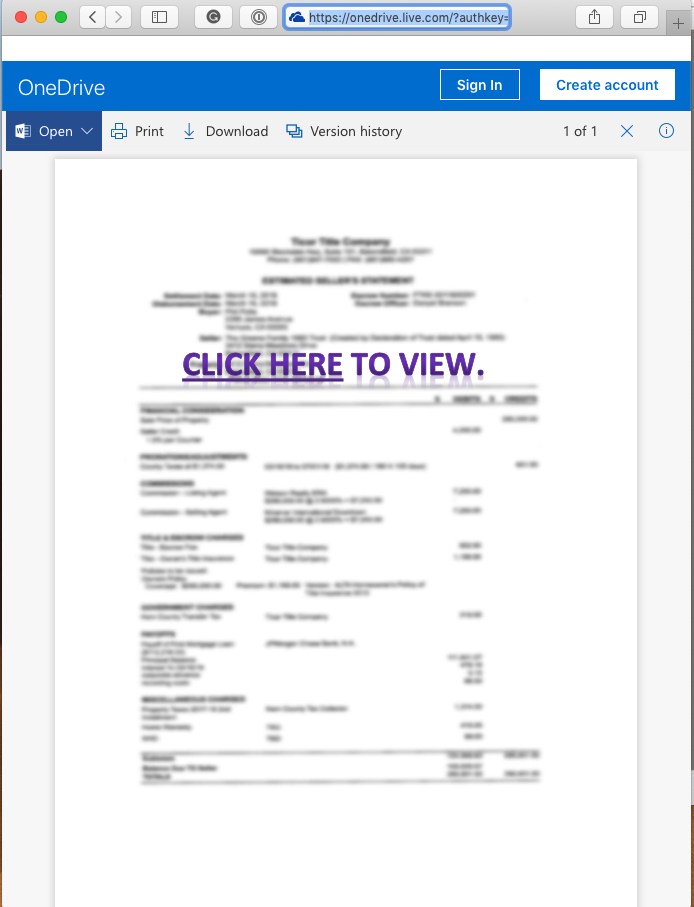
The link itself led to hxxps:// 1drv.ms /b/s!Ajbc-YlY0yFbdwRk1MlFeXtt4YU . "1drv.ms" is actually a legitimate Microsoft owned domain and used as a short link for OneDrive documents. Sure enough, I ended up at a legitimate OneDrive URL. But the document displayed asked me to click again:
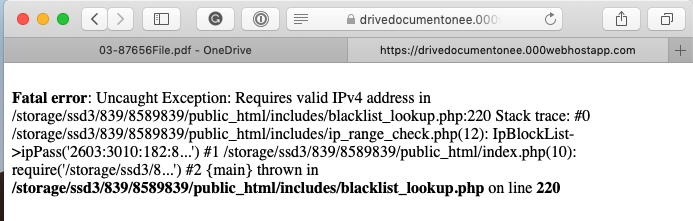
So the next step would be to give the attacker my "honey password". Sadly, I didn't get to this part because the attacker didn't anticipate victims using IPv6. The blocklist the attacker uses to exclude researchers is only considering IPv4, and errors out on IPv6.
This is actually a pretty major oversight. Considering that this attack probably targets home users and also would get good results from mobile users. According to Google [1], about 30 % of these requests will come via IPv6 for users in the US.
[1] https://www.google.com/intl/en/ipv6/statistics.html#tab=per-country-ipv6-adoption
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS Technology Institute
Twitter|
| Application Security: Securing Web Apps, APIs, and Microservices | Washington | Jul 14th - Jul 19th 2025 |



Comments