Collecting Logs from Security Devices at Home
You have probably considered logging the data from your home security devices and often the most difficult question is, where do I start? I included a list of loggers that can be used to collect security data from home devices. One that I have always found interesting is the gateway ISP router because it collects various types of logs including firewall logs (i.e. iptables).
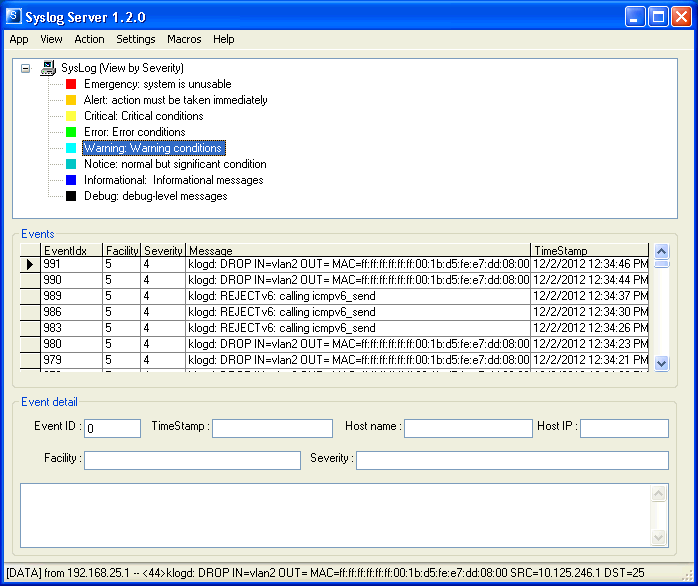
Some of these loggers require more work to setup (i.e. Linux rsyslog) while other are much simpler (i.e. Windows Syslog Server) and start collecting logs right away from your network. For example, the Syslog Server from Sourceforge is a free Windows syslog server that can setup in minutes and can easily collects the logs from a home based router. It has a few features where you can view the events by host, severity (as per picture) and facility and can send an email when a threshold value has been reached. Here is a screenshot of this software collecting Linksys router iptables logs.
If you are using a logger that works well for you and would like to share your experience with other, either add it as a comment or send your description of your favorite logger via our contact form and I will update the list later.
Freeware
Rsyslogd and MySql (Linux only)
http://www.rsyslog.com/doc/rsyslog_mysql.html
Syslog Server (Windows only)
http://sourceforge.net/projects/syslog-server/
Free download but require registration
ArcSight Logger (Log up to 750 MB per day and 10:1 compression. Linux only)
http://www.hpenterprisesecurity.com/products/hp-arcsight-security-intelligence/hp-arcsight-logger/
Splunk (Log up to 500 MB per day. Support multiple OS)
http://www.splunk.com/download
What's Up Gold Syslog Server Free Tool
http://community.whatsupgold.com/freetools/syslog
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu



Comments
http://code.google.com/p/enterprise-log-search-and-archive/
ELSA is included in the new Security Onion 12.04 Beta:
http://code.google.com/p/security-onion/wiki/Beta
Thanks,
Doug
Doug Burks
Dec 2nd 2012
1 decade ago
Paul
Dec 3rd 2012
1 decade ago
Although stunnel and friends may not be readily available for some such platforms, there is often a way to make it work.
I write a document detailing how to get all the parts working on a QNAP NAS device, here: http://stuffphilwrites.com/2012/09/qnap-nas-syslog-messages-ssl/
PhilHagen
Dec 3rd 2012
1 decade ago
Matt
Dec 3rd 2012
1 decade ago
Sadly my DSL router from Actiontec does not support syslog output, despite being Linux-based (BusyBox). Actiontec has stated they have no plans to add syslog.
Paul
Dec 3rd 2012
1 decade ago
AndrewB
Dec 3rd 2012
1 decade ago
Guy
Dec 3rd 2012
1 decade ago