Spear Phishing Handlers for Username/Password
Reviewing my ISC mail inbox, I noticed that I had been receiving multiple phishing email that were very similar. Putting my cursor over each embedded pictures, I noticed the domain involved was the same for all of them. I copied the URL and started checking around for known threat intel on ipfs[.]io against various sites and found on urlscan.io [1], there was over 10000+ samples listed.
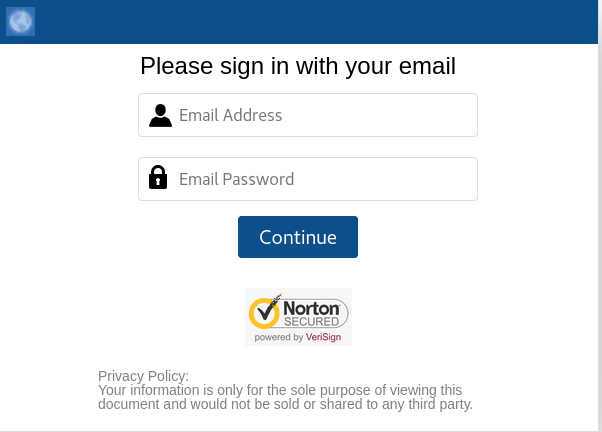
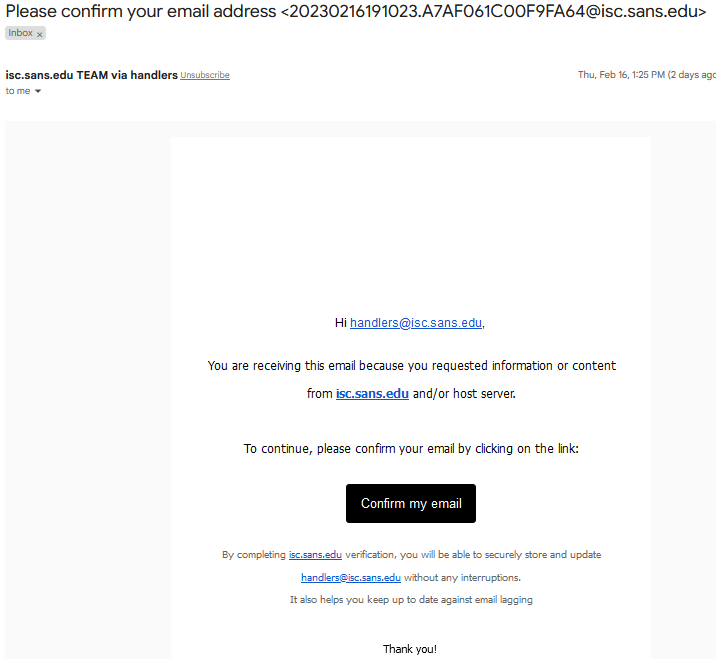
All these emails are asking the recipient to login to capture email address and password and the entries are Secured by Norton!
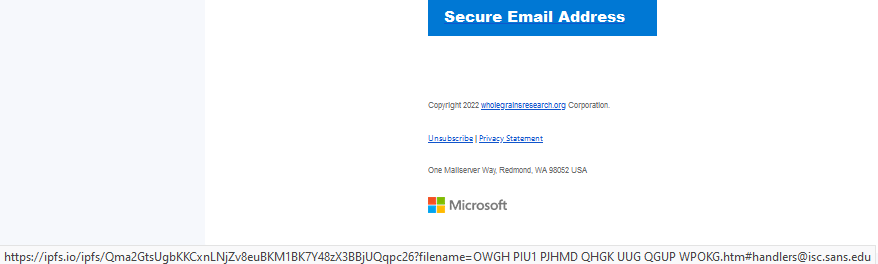
First Email (Received 2 copies with the same URL)
https://ipfs[.]io/ipfs/Qma2GtsUgbKKCxnLNjZv8euBKM1BK7Y48zX3BBjUQqpc26?filename=OWGH%20PIU1%20PJHMD%20QHGK%20UUG%20QGUP%20WPOKG.htm#handlers@isc.sans.edu
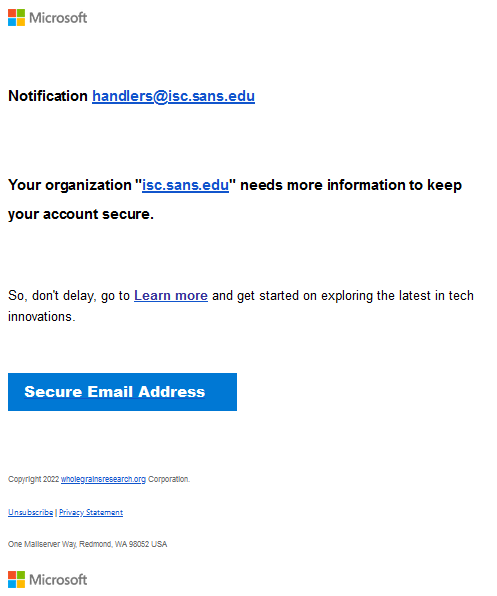
Second Email
https://ipfs[.]io/ipfs/QmaU5FjjeFiDzWs2s6gZ5SyPqL2wvQa2652LHPb3d1U3XC?filename=QUPG%20WGWG%20WDOUH%20UDGW%20URZ%20PKDB%20UKLM.htm#handlers@isc.sans.edu
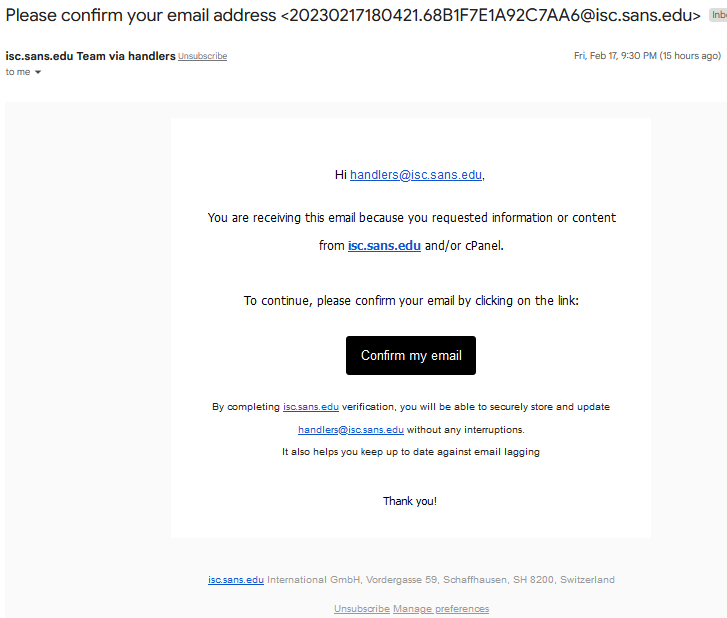
Third Email
https://ipfs[.]io/ipfs/Qma2GtsUgbKKCxnLNjZv8euBKM1BK7Y48zX3BBjUQqpc26?filename=OWGH%20PIU1%20PJHMD%20QHGK%20UUG%20QGUP%20WPOKG.htm#handlers@isc.sans.edu
Indicator
ipfs[.]io
Final Word
Last, a blog post by Lance Spitzner published on the 13 Feb 2023 about "Phishing - It's No Longer About Malware (or Even Email)" [5] highlight some of the changes on the phishing goals and some of the common indicators worth reading including two indicators are no longer recommended: misspellings and hovering of the link "except for highly technical audiences. One problem with this method is that you have to teach people how to decode a URL, which can be a confusing, time consuming, and technical skill."[5]
[1] https://urlscan.io/search/#page.domain%3Aipfs.io
[2] https://www.virustotal.com/gui/url/2c8a881b916d2396ff68ed18c41a6b8a13ba8e869de65d87a23b869a95fd0c63?nocache=1
[3] https://www.virustotal.com/gui/domain/ipfs.io/detection
[4] https://cybergordon.com/result.html?id=12ef23f1-a775-4619-81ec-c7aaaae7e4a4
[5] https://www.sans.org/blog/phishing-its-no-longer-about-malware-or-even-email/
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments