Ukraine Themed Twitter Spam Pushing iOS Scareware
With the expansion of Russia's invasion of Ukraine in February, Ukraine has made heavy use of social media to demonstrate die ability of the Ukrainian armed forces to repulse the attack. Ukraine often shares video clips showing attacks against Russian troops from drones or action camera footage from the front lines. These videos have been widely distributed, and various social media channels have shared them to build an audience for themselves.
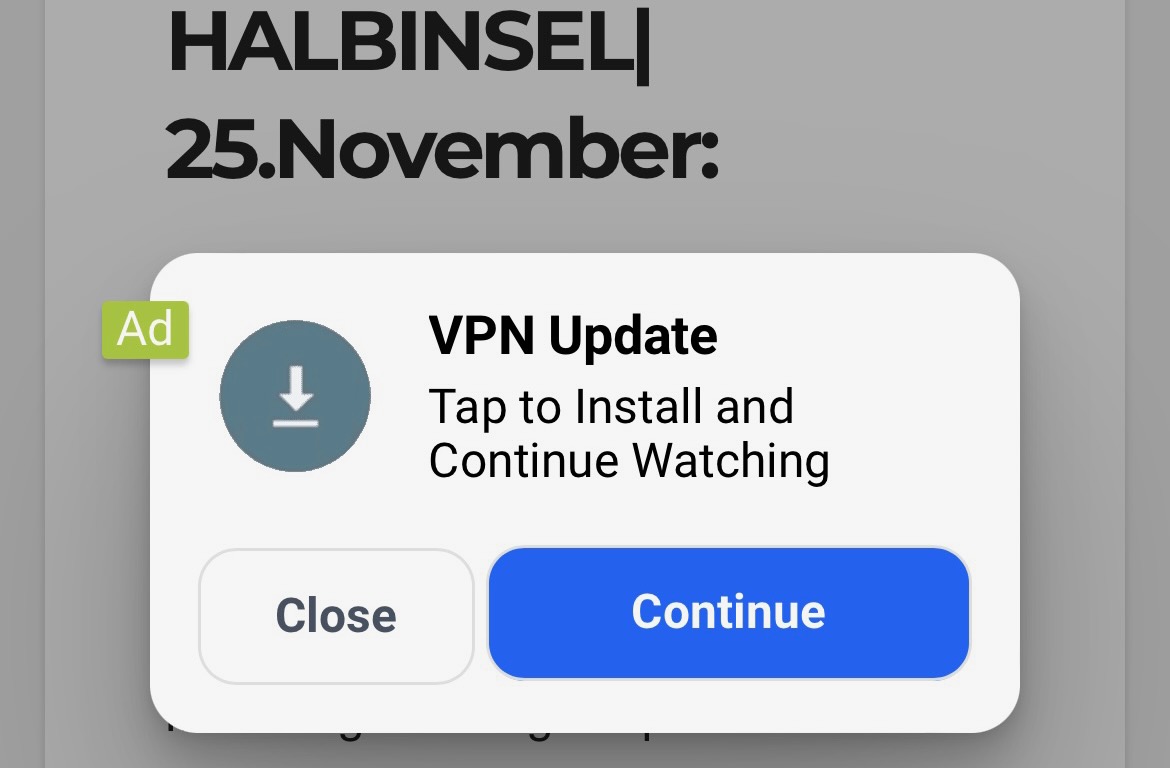
Of course, like any current significant event, these videos are also used to push more malicious content. Recently I have observed how on Twitter, many videos not hosted on the platform are attempting to push scareware/malware. The type of software being advertised with the videos depends on the device used to view the content. For example, the following tweet as seen from an iPhone:

The account "Sender (G)" was registered with Twitter about a year ago, so it isn't new, and it currently only has around 550 followers. But it is part of a more extensive set of accounts that may be under the control of one entity. All accounts use similar or identical messages and point to the same sites.
In this case, you are directed to "sender-g.com," and as an iOS user, you may see one of several VPN or anti-malware ads:
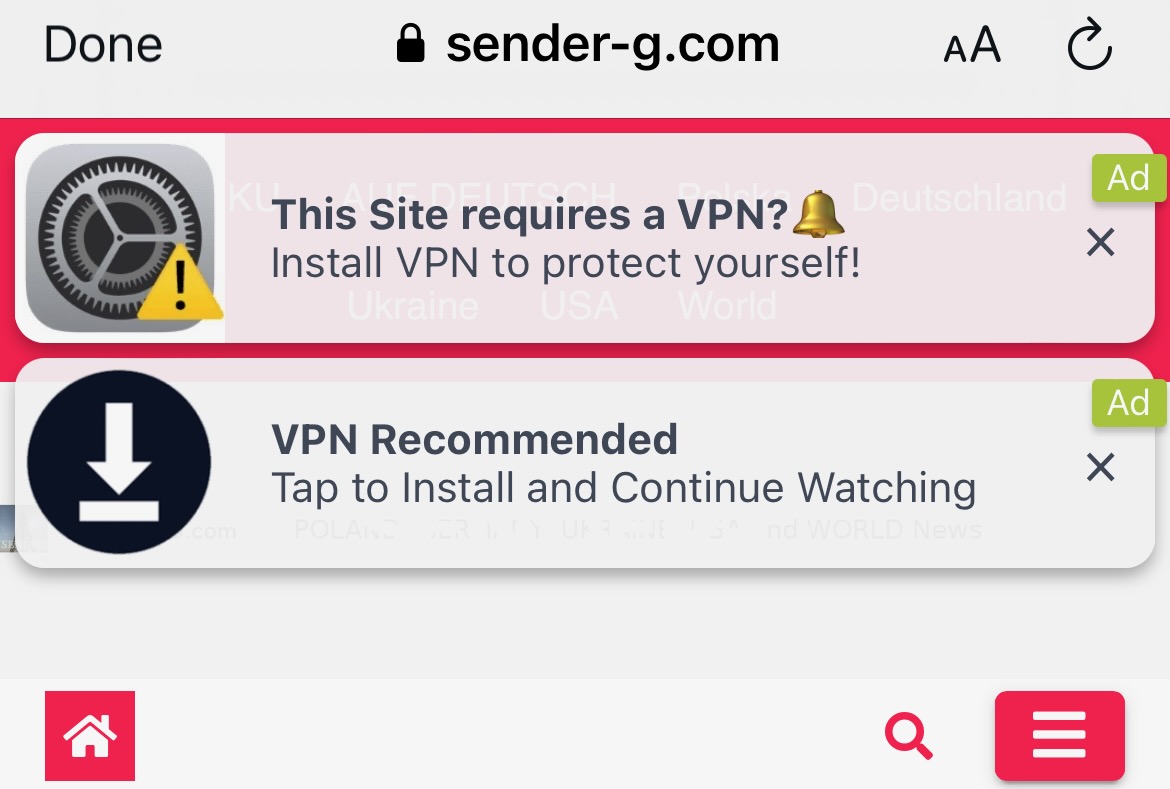
Once clicking on one of the popups, the user will be confronted with additional "scare" messages:

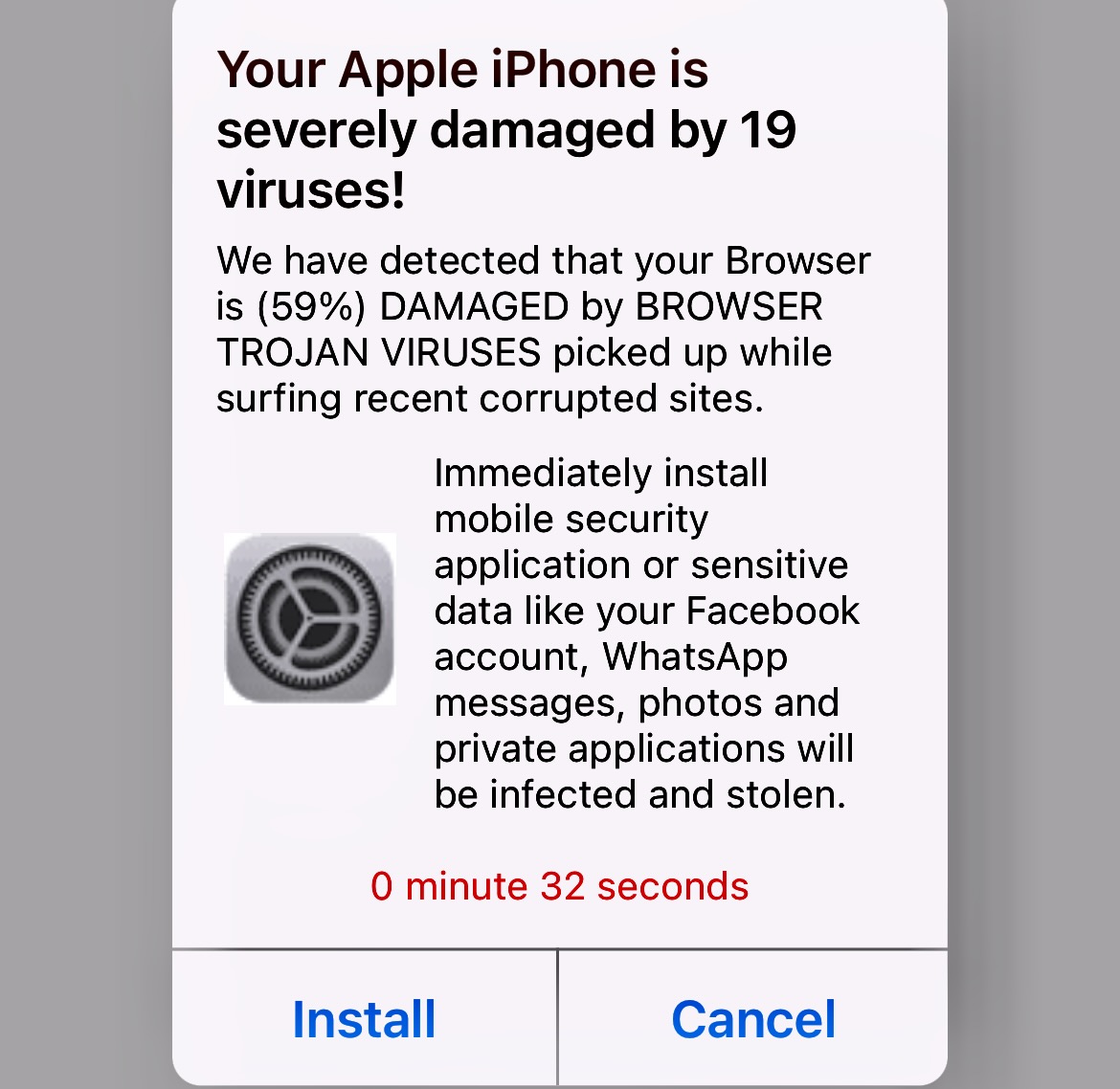
In the end, the victim will be redirected to the "Free" VPN application in Apple's iOS Appstore. The application appears to be more or less benign, and I didn't test the quality of the VPN yet, but it also probably doesn't do much for the user but agressively push in-App purchases to subscribe to premium services.
If you visit sender-g.com with a desktop browser, you may see similar ads for software like McAfee antivirus or Mackeeper, a MacOS cleanup utility. Interestingly, the website itself does not show any visible ads but only popups.
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|


Comments