Windows Malware with VHD Extension
Windows 10 supports various virtual drives natively and can recognize and use ISO, VHD and VHDX files. The file included as an attachment with this email, when extracted appears in the email as a PDF but is is in fact a VHD file.
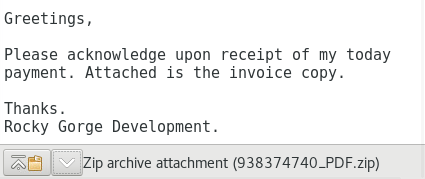
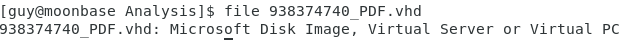
This email received this week with a zip file attachment, after extraction, contained a file with a VHD extension. Using Linux file command, identified the file as a Microsoft Disk Image.
Windows 10 File Browser Listing
File was submitted to Virustotal [1] for analysis with very little detection and was identified as a Trojan by two scan engines. Sandbox analysis also indicated it may try to detect the virtual machine to hinder analysis, analysis by sandbox was minimal. Sandbox indicated the original filename was 7zS.sfx.exe0 vs 938374740_pdf.vhd
Attempt to copy the file to Windows 10 Sandbox [2] crashed the system. A second attempt to copy the file resulted with the same outcome.
Indicators
filename: 938374740_pdf.vhd, 7zS.sfx.exe0
SHA256: ea9aca145f23464a7739c7b3b6a8f8c7ce65bdd6f868e0a87a65a9a1291ee960
[1] https://www.virustotal.com/gui/file/ea9aca145f23464a7739c7b3b6a8f8c7ce65bdd6f868e0a87a65a9a1291ee960
[2] https://isc.sans.edu/diary/Malware+Analysis+with+elasticagent+and+Microsoft+Sandbox/27248
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu




Comments