Phishing Word Documents with Suspicious URL
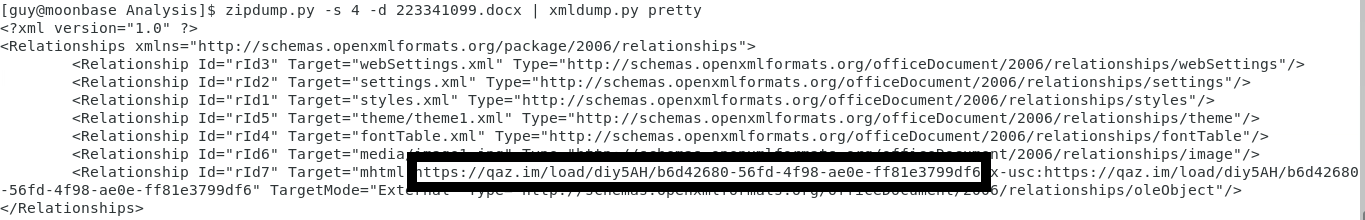
Got this word document this week that was quarantined as phishing by Defender (223341099.docx) with the Subject: Urgent Payment Issue. Using Didier malware analysis tools, I ran through the following checks to see what could be embedded in it that is likely suspicious. I first checked the file using oledump.py to see if there were any OLE files in this document.
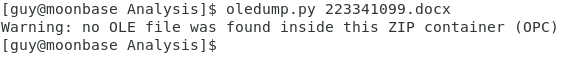
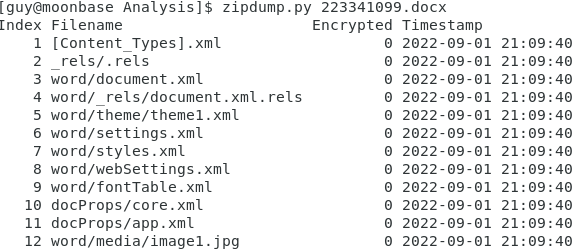
Next step was to check what is inside this OPC file using zipdump.py.
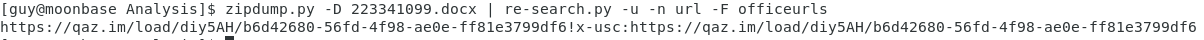
There is one jpeg file in there and the remainder are all XML all dated September 1, 2022. Since everything appear to be a word/document.xml, lets look for URL that might be hidden in this word document by digging inside with zipdump.py using the following options described by Didier here:
One interesting URL has been located in the document. The option re-earch searches inside the text with -e which extracted the string. My last step is to dump content of item #4 to see all the other URLs including the one previous identified:
Indicator
qaz[.]im
https://qaz[.]im/load/diy5AH/b6d42680-56fd-4f98-ae0e-ff81e3799df6
[1] https://github.com/DidierStevens/DidierStevensSuite
[2] https://isc.sans.edu/diary/Analyzing+a+Phishing+Word+Document/28562
[3] https://www.virustotal.com/gui/url/bdebda9813ab5d38ec1e2b691aa40e2886f3c38e726780560b59af6007906ad6?nocache=1
-----------
Guy Bruneau IPSS Inc.
My Handler Page
Twitter: GuyBruneau
gbruneau at isc dot sans dot edu


Comments