How Many SANs are Insane?
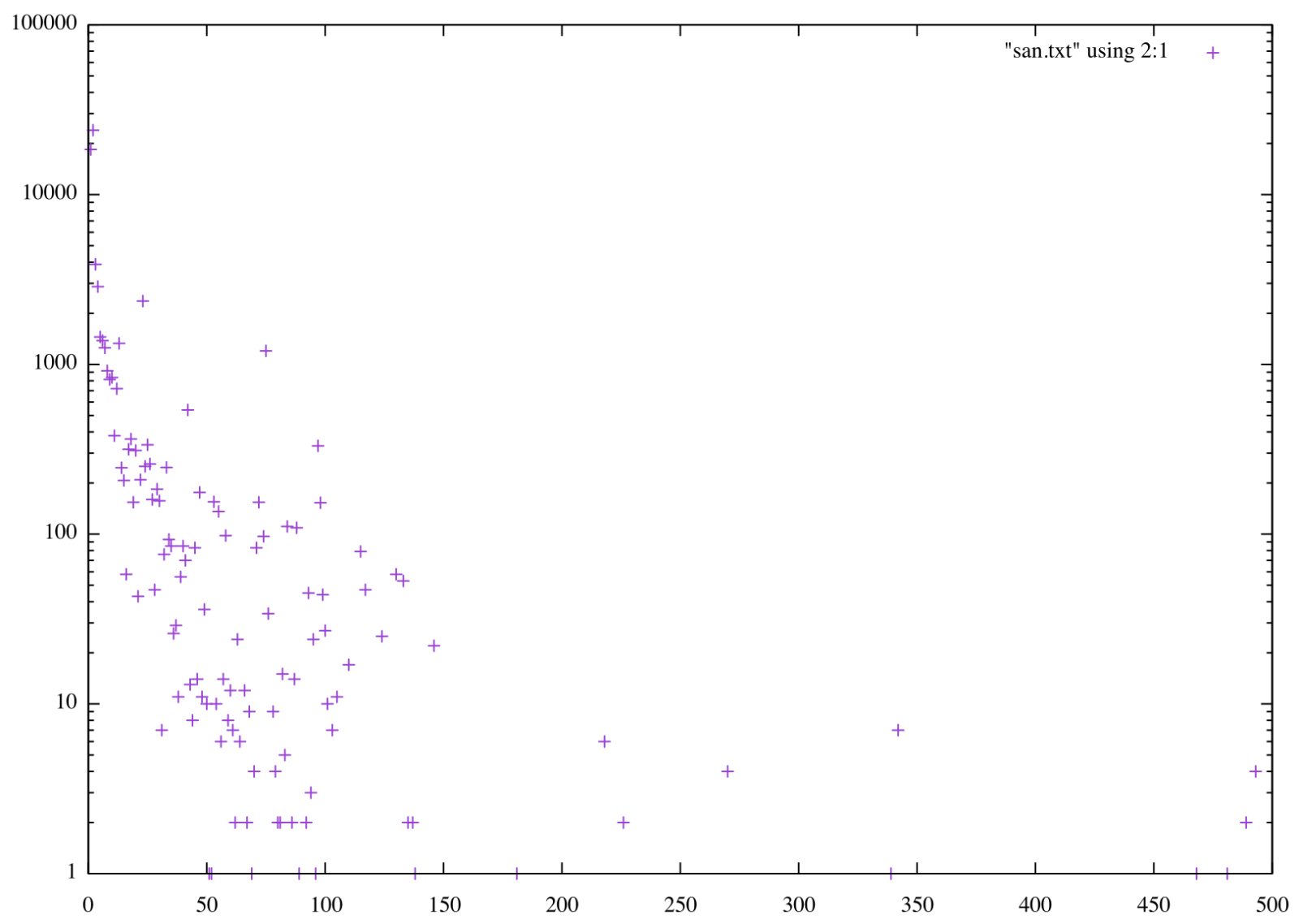
x509 certificates, as they are used for TLS, can include multiple "Subject Alternative Names" (SANs) to be used with various websites. Experimenting with numerous ways to detect TLS anomalies, I looked at my Zeek x509 logs to summarize how many names are present in certificates.
My Zeek logs are stored in JSON format to make it easier to send them to Elasticsearch. But I also prefer the jq over the zeek native tool zeek-cut (personal preference).
I used this command line to summarize the logs:
zcat x509.log | jq '."san.dns" | length' | sort | uniq -c | sort -n
Based on this methodology, the maximum number of SANs per certificate is close to 500, but most are using 100 hostnames or less.
But the real question: What is normal?
It turns out there is no real "hard" limit. The RFCs leave it up to the implementation to define how many SANs to allow [1]. Different certificate authorities implement different limits:
Let's Encrypt [2] , GoDaddy[3]: 100
Comodo[4]: 1,000 (some older references appear to state 2,000 are allowed)
So, in short: it appears that 100 is "safe." For larger numbers, you may run into implementation-specific issues.
]1] https://datatracker.ietf.org/doc/html/rfc5280#section-4.2.1.6
[2] https://letsencrypt.org/docs/rate-limits/
[3] https://www.godaddy.com/web-security/multi-domain-san-ssl-certificat
[4] https://comodosslstore.com/comodo-mdc-ssl.aspx
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|


Comments