0.0.0.0 in Emotet Spambot Traffic
Introduction
Emotet often uses information from emails and address books stolen from infected Windows hosts. Malicious spam (malspam) from Emotet spoofs legitimate senders to trick potential victims into running malicious files.
Additionally, Emotet uses IP address 0.0.0.0 in spambot traffic, possibly attempting to hide the actual IP address of an Emotet-infected host.
This ISC diary reviews the spoofed 0.0.0.0 address used in a recent Emotet infection from Tuesday 2022-01-18.
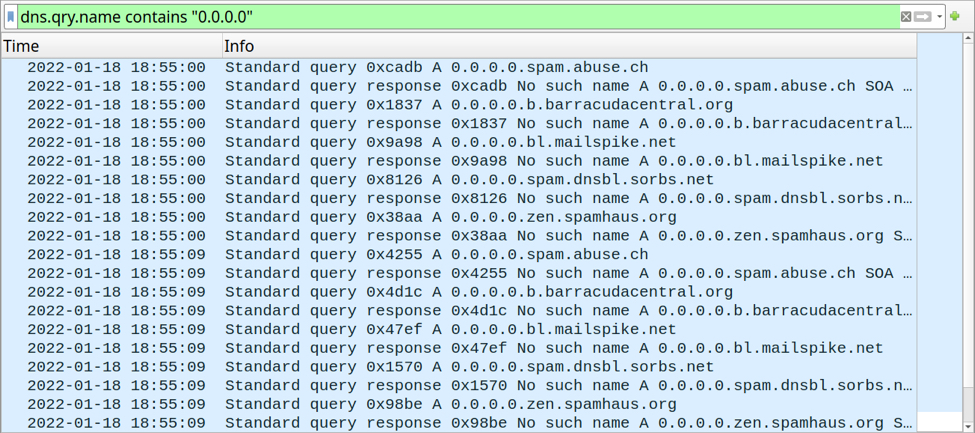
Shown above: 0.0.0.0 in DNS queries from an Emotet-infected host.
Scenes from an infection
Both Emotet botnets (dubbed by researchers as "epoch 4" and "epoch 5") resumed activity after the recent holiday season, and malicious spam started approximately one week ago on Tuesday 2022-01-11.
Most Windows hosts I've infected with Emotet in my lab will start spamming within an hour or less after the initial infection. Refer to the images below for activity from a recent Emotet infection on 2022-01-18.
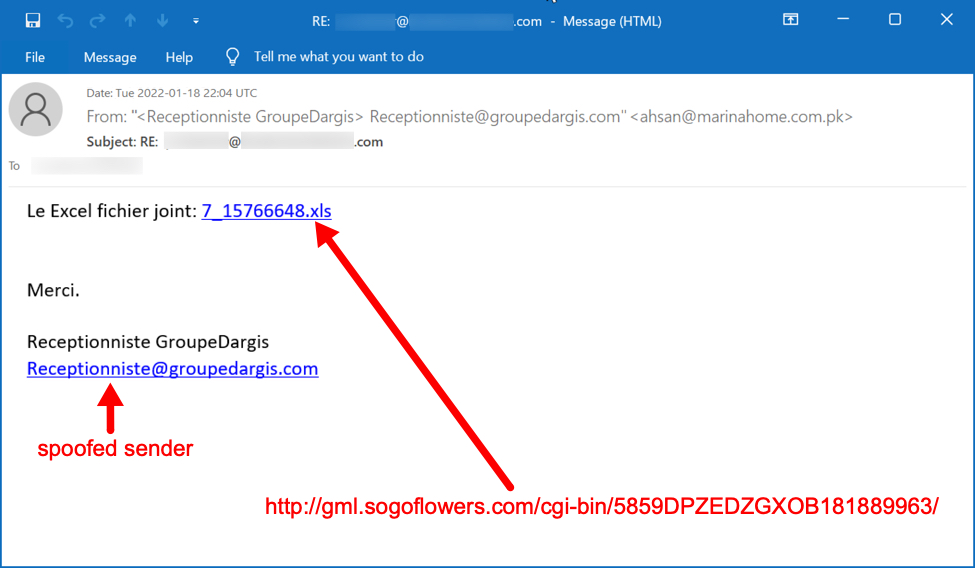
Shown above: Screenshot from malspam pushing Emotet on Tuesday 2022-01-18.
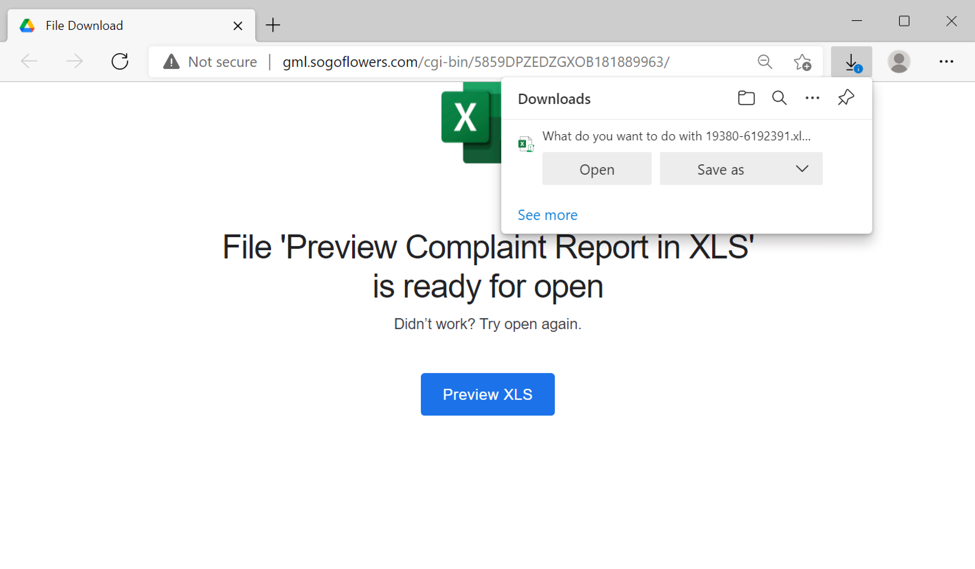
Shown above: Web page from link in the malspam.
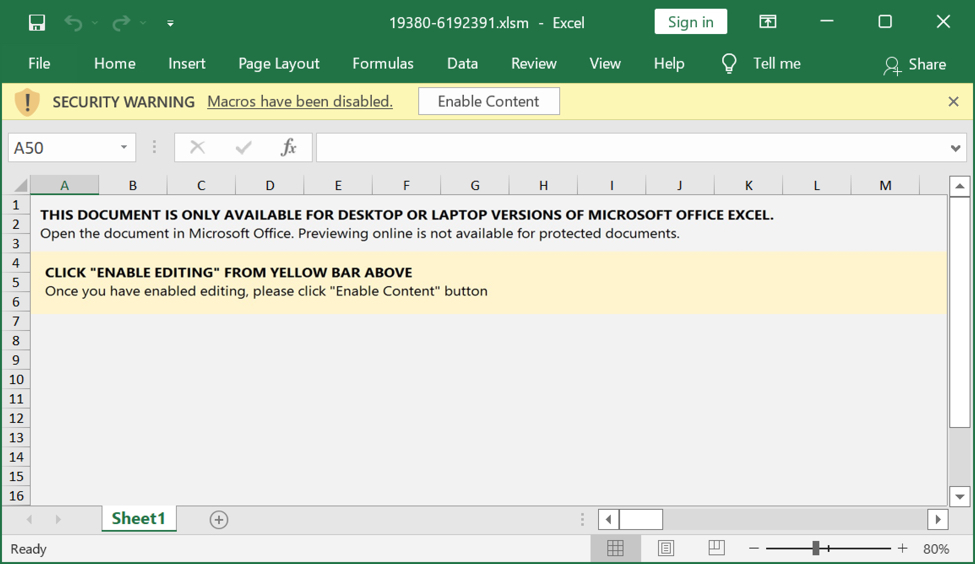
Shown above: Example of downloaded Excel spreadsheet for Emotet.
Enable macros in a downloaded spreadsheet, and they will infect a vulnerable Windows host. This is standard operating procedure for Emotet.

Shown above: Traffic from an infection filtered in Wireshark.
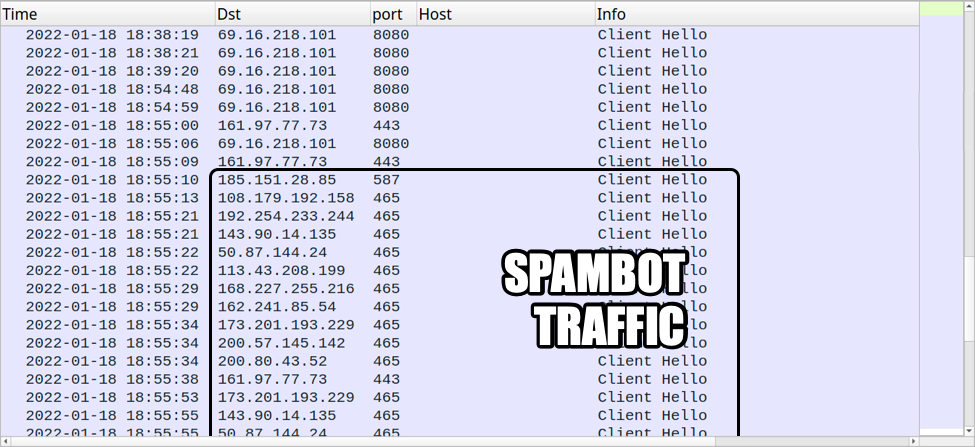
Shown above: Spambot activity started approximately 27 minutes after the initial infection.
Emotet spambot traffic using 0.0.0.0
Right as the spambot activity starts, the following DNS queries are made using domains related to spam filtering:
- 0.0.0.0.spam.abuse.ch
- 0.0.0.0.b.barracudacentral.org
- 0.0.0.0.bl.mailspike.net
- 0.0.0.0.spam.dnsbl.sorbs.net
- 0.0.0.0.zen.spamhaus.org
Similar DNS queries, but without the 0.0.0.0, are generated during Trickbot infections. However, Trickbot uses the infected host's public IP address data in the DNS query. Here is an example from analysis of a Trickbot sample (scroll down to the "Domains" list).
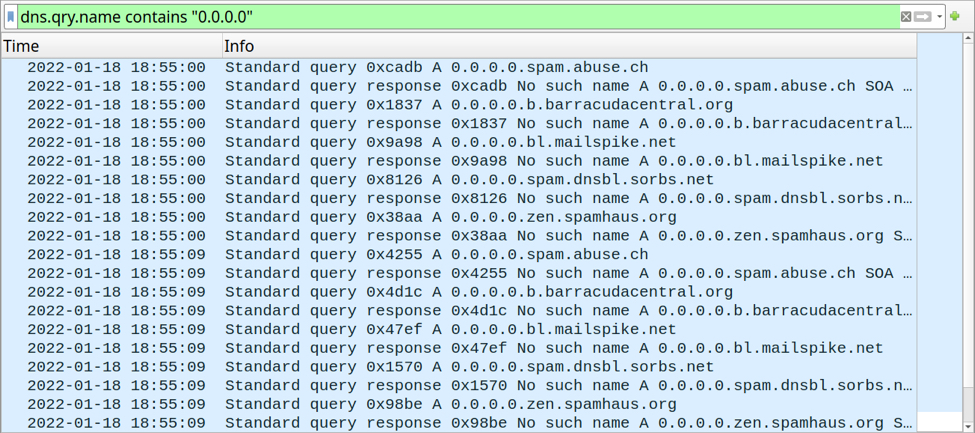
Shown above: 0.0.0.0-related DNS queries from an Emotet-infected host.
In addition to DNS queries, Emotet uses 0.0.0.0 during SMTP communications. This happens whenever an Emotet-infected host tries sending malspam to a targeted mailserver. The SMTP command is EHLO [0.0.0.0].

Shown above: SMTP traffic using EHLO [0.0.0.0].
This attempt does not hide the actual IP address of an Emotet-infected host, because it still appears elsewhere in the SMTP traffic (blurred in the above image, for example). But 0.0.0.0 can be an indicator of emails pushing Emotet or other malware.
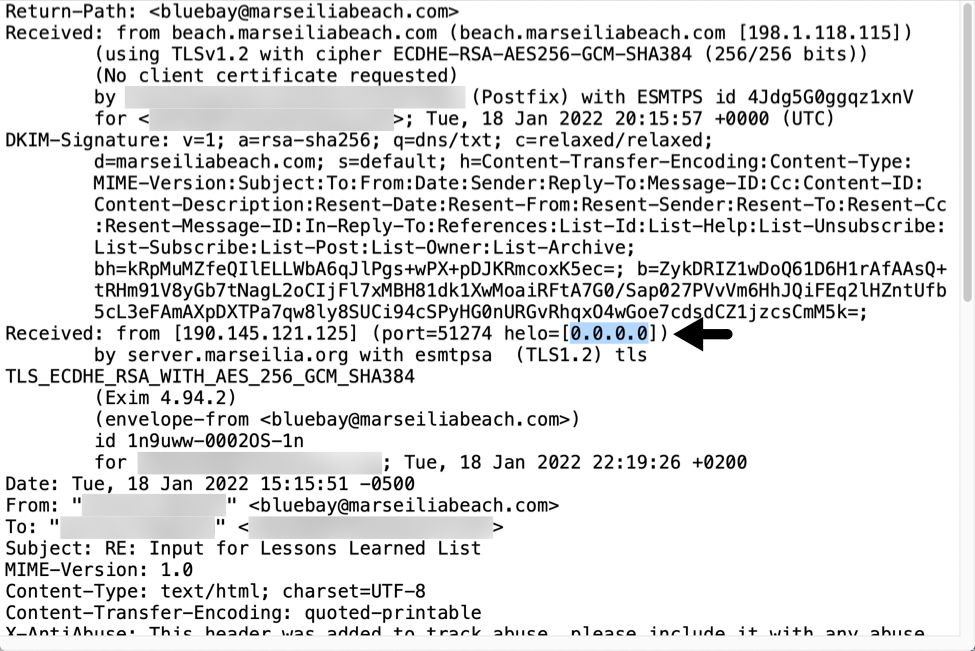
Shown above: Example of Emotet malspam with 0.0.0.0 in the email headers.
Final words
While 0.0.0.0 is an indicator for Emotet or other malware, you can find up-to-date indicators for Emotet malware samples, URLs, and C2 IP addresses at:
- https://urlhaus.abuse.ch/browse/tag/emotet/
- https://feodotracker.abuse.ch/browse/emotet/
- https://bazaar.abuse.ch/browse/tag/Emotet/
- https://threatfox.abuse.ch/browse/malware/win.emotet/
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments