Hunting for PHPUnit Installed via Composer
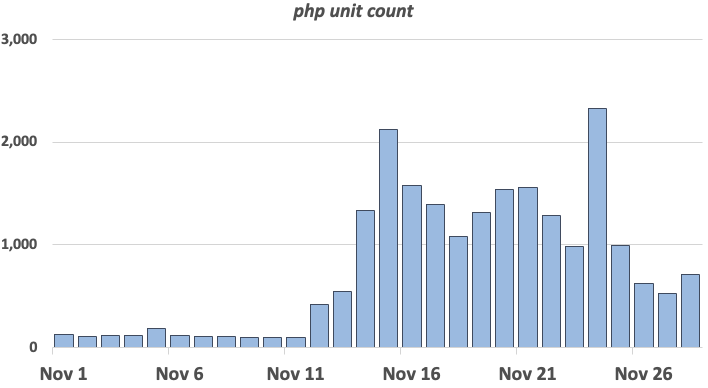
One rather persistent pattern in our honeypot logs is attacks against older PHPUnit flaws. These attacks appear to exploit CVE-2017-9841, a simple remote code execution vulnerability [1]. Back in 2019, Imperva called it "one of the most exploitable CVEs of 2019", and even now, attacks keep coming in [2]. After tuning one of our honeypots to be more sensitive to these attacks, we saw one to two thousand attacks against the honeypot a day (the honeypot covers multiple IP addresses).
So why is a four-year-old vulnerability still so popular? Looking at the exploited URLs, one pattern emerged is the inclusion of WordPress plugins and other addons that administrators may install via composer. The most common URLs are:
/sites/all/libraries/mailchimp/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
/laravel/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
/wp-content/plugins/dzs-videogallery/class_parts/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
/wp-content/plugins/jekyll-exporter/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
/wp-content/plugins/cloudflare/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
/wp-content/plugins/mm-plugin/inc/vendors/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
/modules/gamification/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
/modules/autoupgrade/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
/modules/ps_facetedsearch/vendor/phpunit/phpunit/src/Util/PHP/eval-stdin.php
...
One issue may be that administrators installing these plugins and extensions may not be aware that they will install and enable PHPUnit as they install the respective extension. A typical composer.json file used to install the extension will include an extension like
"require-dev": {
"phpunit/phpunit": "^6.2.2"
},
The example above includes version 6.2.2 or later of PHPUnit if the respective module is installed with the "dev" option (composer install --dev). Luckily, only PHPUnit before 5.6.3 or 4.8.27 is vulnerable. I took a quick look at the respective composer.json files, and none of the current files requires such an old version (if it is still available). But I guess, given the heavy scanning for this vulnerability, there may still be sufficient numbers of vulnerable systems around.
This is also more of a "composer" vs. a WordPress problem. While WordPress remains a favorite target of attackers due to its popularity, composer like many similar technologies (npm, pip...) obscures some of the dependencies installed automatically and makes inventorying dependencies more difficult. As a quick test, you could run this command:
find . -name 'composer.json' -exec egrep -H phpunit {} \;
to find all composer.json files that include a reference to PHPUnit
[1] https://nvd.nist.gov/vuln/detail/CVE-2017-9841
[2] https://www.imperva.com/blog/the-resurrection-of-phpunit-rce-vulnerability/
---
Johannes B. Ullrich, Ph.D. , Dean of Research, SANS.edu
Twitter|


Comments