Quickie: Bit Shifting With translate.py
As promised in diary entry "Corrupt BASE64 Strings: Detection and Decoding", I explain here how to shift bits with my translate.py tool:
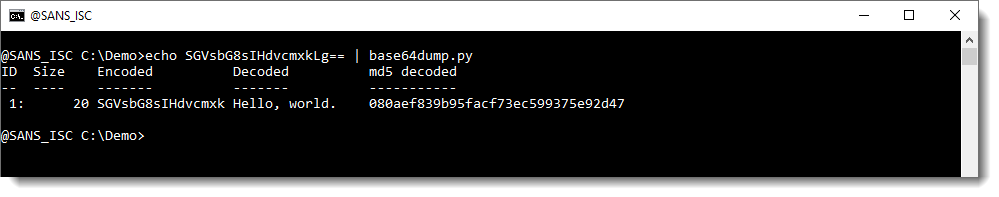
Here is a BASE64 string (SGVsbG8sIHdvcmxkLg==) that decodes to "Hello, world.":
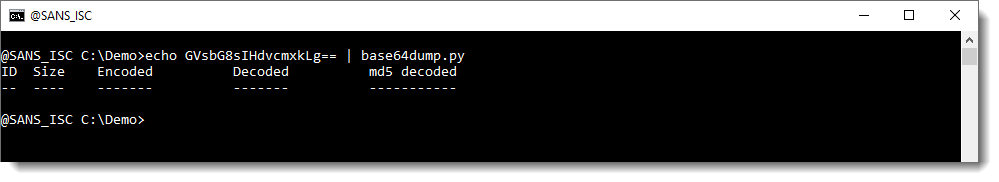
Corrupting this BASE64 string by removing the first character (S) means that it is no longer detected:
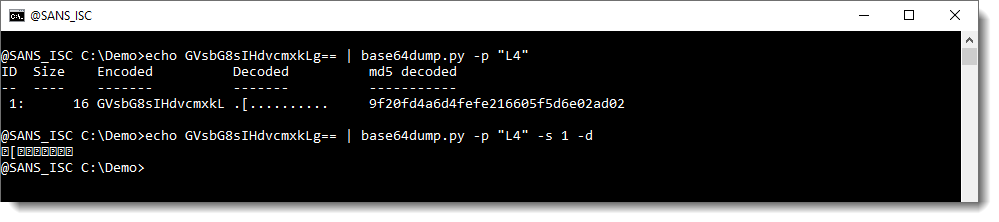
And truncating the length to a multiple of 4 (with Python function L4) makes that it gets detected, but not decoded properly:
We then proceeded in diary entry "Corrupt BASE64 Strings: Detection and Decoding" to manipulate the input BASE64 string so that we arrived at a decoded string we could recognize.
Here, in stead of manipulating the input BASE64 string, I'm manipulating the output by shifting bits.
Each character in a BASE64 string represents 6 bits. So I will bit shift the output with 2, 4 and 6 bits to the right using my translate.py tool like this (this command shifts the complete byte sequence, not individual bytes):
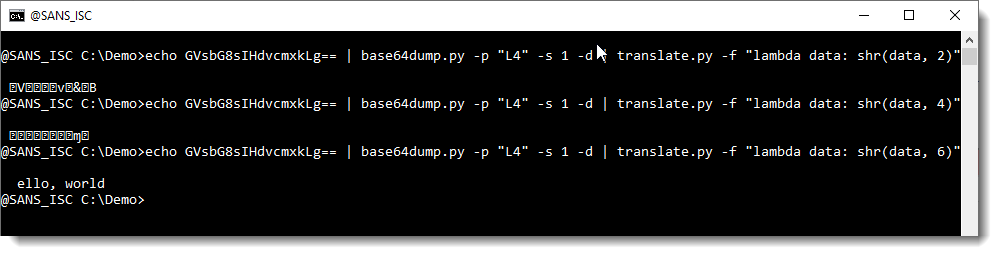
The result here is that a bit shift to the right of 6 bits results in a decoded BASE64 string that we can recognize.
With this we know that it is likely that we are missing one BASE64 character at the beginning, and thus we can try fixing it like explained in previous diary entry.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com



Comments