YARA: XOR Strings
I did not notice this in August when YARA 3.8.0 was released, but a new string search feature was introduced: XOR searching.
Here is an example:
rule xor_test {
strings:
$a = "http://isc.sans.edu" xor
condition:
$a
}
By using string keyword "xor" with a string, the YARA engine will search for all byte sequences that match any 1-byte key XOR-encoded versions of this string (except for "key" 0x00).
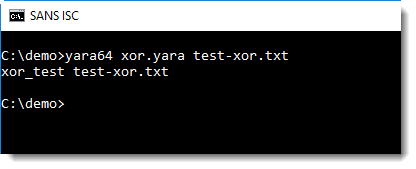
In this example, file test-xor.txt contains a URL encoded with XOR key 0x41 (A).
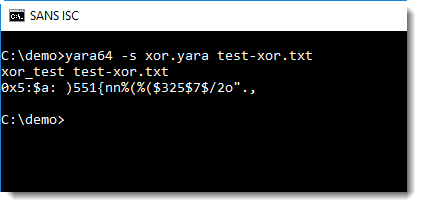
With option -s, the encoded string is displayed:
String modifier "xor" can be used together with string modifiers "ascii", "wide" and "nocase".
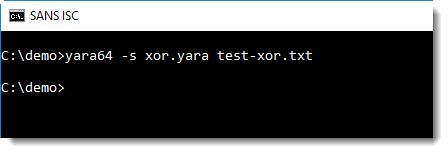
It can not be used with regular expressions, although no error or warning is displayed:
rule xor_test_re {
strings:
$a = /http:\/\/[a-z]+\.com/ xor
condition:
$a
}
It does work if the regular expression is literal:
rule xor_test_re {
strings:
$a = /http:\/\/didierstevens\.com/ xor
condition:
$a
}
But I don't see the use case for this.
Didier Stevens
Senior handler
Microsoft MVP
blog.DidierStevens.com DidierStevensLabs.com


Comments