Always Check Your References (Cheat Sheets to the Rescue)
Most of us have a cheat sheet [CS] here and there. In my jump bag there is a 3 ring binder with cheat sheets in plastic sheet protectors. In this, it got me thinking about cheat sheets again and there are a few things to share. First, we have wrote about them many times over the years (located with site:isc.sans.edu Cheat Sheets) [1] [2] [3] [4] [5]. There are also a series of cheat sheets all over the ‘intertubes’ [6] [7] [8] and lets not forget the great list of CS at Packet Life [9]. There are even GIT repositories of CS [10].
Note: From here On, I am talking about an Apple OS X only App. If someone wants to contribute something similar for Linux and Windows email me ( rporter at isc dot sans dot edu ) or twitter @packetalien and I will post an update.
One common thing that has been bothering me as of late is ‘search-ability’ and ease of getting to quick answers in a cheat sheet. Then I thought about possible solutions and wanted to share.
For other coding references there is Dash [11] which I use heavily and they have tons of cheat sheets [12]. While sitting in a SANS 572 Advanced Network Forensics, it hit me, write a Packet Forensics CS, to the Dash Docs Batman.
As it turns out, the format is easy to understand and based in Ruby [12] and there is a Ruby gem called Cheatset [13] that has great samples.
Here is a screenshot of what I’ve got so far, and this cheat sheet will be for packet "forensicators":
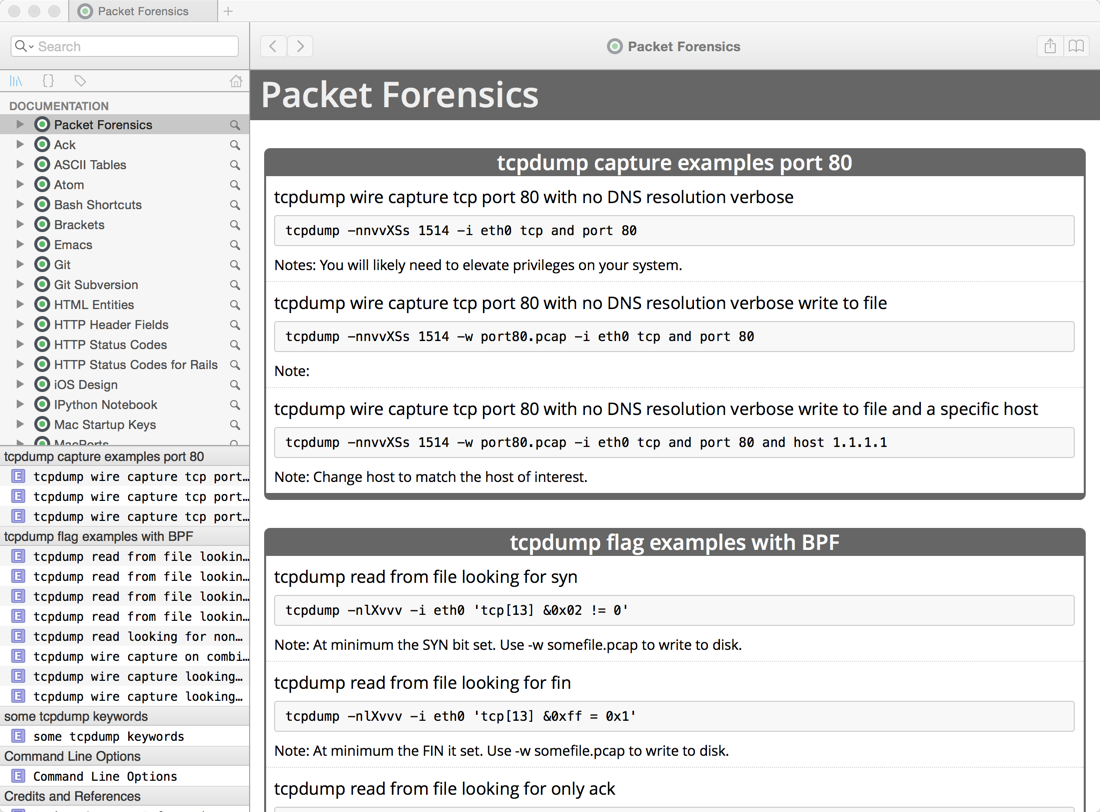
There will be more to come as time permits and if anyone is interested in the source or docset for this and or would like to contribute email me ( rporter at isc dot sans dot edu ) or twitter @packetalien.
A final note, when doing forensics on a case, it is always good to have references handy!
[1] https://isc.sans.edu/diary/2+Cheat+Sheets+for+Incident+Handling/5354
[2] https://isc.sans.edu/diary/Cheat+Sheet%3A+Analyzing+Malicious+Documents/7705
[3] https://isc.sans.edu/diary/New+and+updated+cheat+sheets/6958
[4] https://isc.sans.edu/diary/New+Incident+Response+Methodology+Cheat+Sheet/10828
[5] https://isc.sans.edu/diary/OWASP+Session+Management+%22Cheat+Sheet%22/11263
[6] https://isc.sans.edu/presentations/
[7] https://www.owasp.org/index.php/Session_Management_Cheat_Sheet
[8] https://cert.societegenerale.com/en/publications.html
[9] http://packetlife.net/library/cheat-sheets/
[10] https://github.com/detailyang/cheat-sheets
[12] https://github.com/Kapeli/cheatsheets
[13] https://github.com/Kapeli/cheatset
Richard Porter
@packetalien, packetalien.com, rporter at isc dot sans dot edu
--- ISC Handler on Duty


Comments