DNS-based DDoS
ISC reader Zach reports that his company currently sees about 4Gbps of DNS requests beyond what is "normal", and all seem to originate from 91.216.194.0/24. Yup, someone on that IP range in Poland is likely having a "slow network day".
To make it less likely that your DNS servers unwittingly participate in a denial of service attack against someone else, consider using rate-limiting. If you are not running a massively popular eCommerce site, odds are your bandwidth and the load limit of your DNS server are way way beyond what you actually need.
The easiest way to rate-limit (if you use Linux) is to put an iptables rule on port 53 that controls how many packets per source IP address will be accepted per minute. BIND, one of the most popular DNS servers, introduced a response rate-limiting option in version 9.10 that allows to define how many responses per second the server will provide before it punts. Both are good ideas if you run an authoritative DNS server that has way more bandwidth and muscle than your actual usage requires.
Macros? Really?!
Yes indeed! While the past 15 years or so were mostly devoid of any significant macro viruses, macro-based malware is now making a "successful" comeback. Last week, we saw a significant Dridex malware run that was using macros in Excel files (.XLSM), and earlier this week, the crooks behind the banking spyware "Vawtraq" started to spam the usual "Fedex Package" and "Tax Refund" emails, but unlike in other malspam runs, the attachment was no longer a ZIP with an EXE or SCR inside, but rather a file in Microsoft Office .DOC format. File extension based blocking on the email gateway is not going to save your bacon on this one!
For Vawtraq, if the recipient opens the DOC, the content looks garbled, and the only readable portion is in (apparently) user-convincing red font, asking the recipient to enable macros. You can guess what happens next if the user falls for it...: A VBS and Powershell file get extracted from the DOC, and then download and run the Vawtraq malware executable. The whole mess has very low detection in anti-virus, yesterday's Vawtraq started with zero hits on VirusTotal, and even today, one day later, it hasn't made it past 7/52 anti-virus engines detecting the threat yet. Thus, odds are you will need to revert to manual analysis to determine if a suspicious Office document is indeed malicious, and to extract any indicators from it that can help to discover users on your network who have been "had".
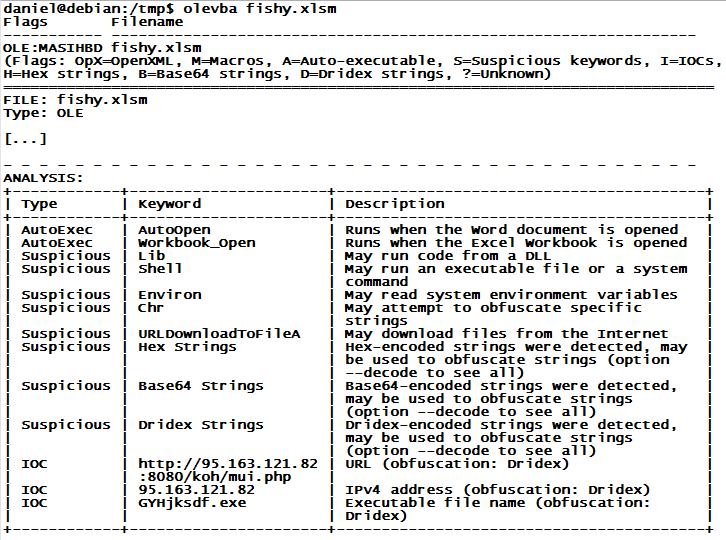
Besides Didier Stevens' "oledump" that we covered last month, my favorite toolkit for this analysis is the python-oletools package by Philippe Lagadec. "olevba" in particular does a great job at parsing out all the obfuscated code, and is often even able to extract actionable indicators of compromise (IOC), like URLs and IP addresses. The example below is an abbreviated "olevba" analysis of a recent Dridex run, and it nicely shows how the next stage URL and EXE name are pulled out in one quick swoop. Give it a try!


Comments