Ongoing NTP Amplification Attacks
Brett, who alerted us earlier this month regarding the mass exploit against Linksys devices has surfaced a current issue he's facing with ongoing NTP amplification attacks. A good US-CERT summary of the attack is here: https://www.us-cert.gov/ncas/alerts/TA14-013A. Brett indicates that:
"We are seeing massive attacks on our NTP servers, attempting to exploit the traffic amplification vulnerability reported last month. Our IPs are being probed by an address in the Netherlands, and a couple of them -- at which unpatched servers were discovered -- are being hit with about 3 million spoofed packets per hour. (We've since patched and firewalled the vulnerable servers, but the packets keep coming.) The spoofed packets are crafted so that they appear to be originating mostly from port 53 and 80, but occasionally have other port numbers such as 3074 (XBox) and 6667 (IRC). This is a very serious attack for us, and I'd appreciate some help in alerting folks to it."
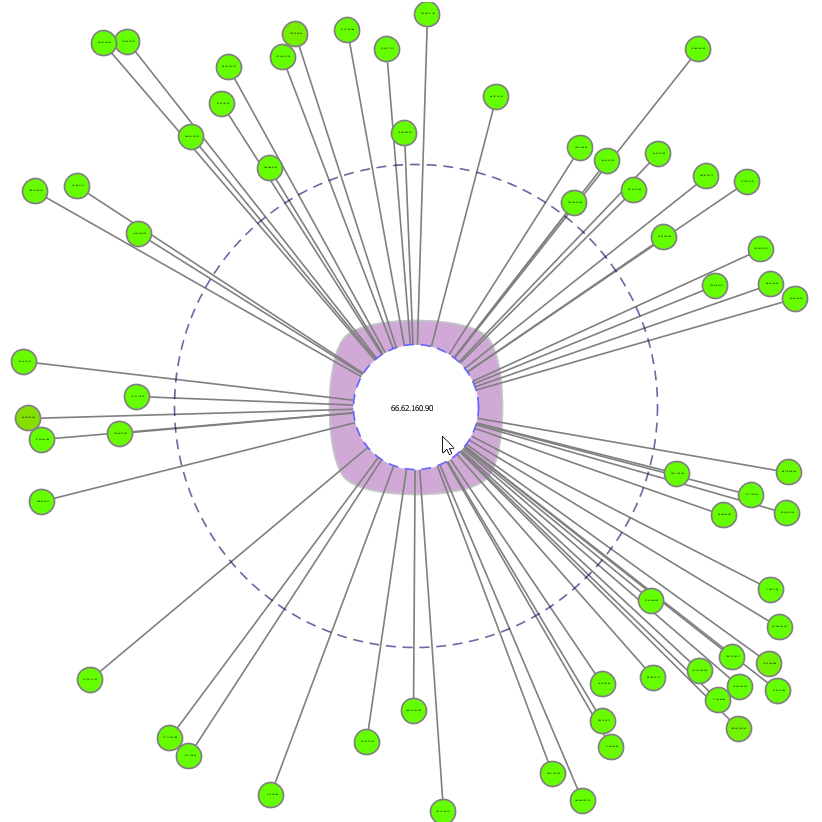
He also sent along a 8 second packet capture that I've visualized as seen below.
According to Brett, folks receiving similar traffic will see numerous "monitor" queries from spoofed source addresses and ports. His ISP is receiving roughly 3 million of these packets every hour, aimed at 3 IP addresses that belonged to FreeBSD servers that were vulnerable in their default configurations, servers that have now been patched and firewalled. He reminds us that even when The FreeBSD Project's patch has been applied, a vulnerable server will continue to respond to the queries with an equal number of rejection packets. While the patch eliminates the traffic amplification, the traffic is still echoed and its origin is further obscured.
Brett's ISP is are also seeing probes of their IPs looking for additional vulnerable servers originating from IP address 93.174.95.119 (NL), "which may be a server controlled by the person(s) behind the attack. The probes stand out because they are reported by tcpdump as being NTPv2, while most of the other traffic is NTPv3 or NTPv4. Level3 was apparently having congestion problems yesterday and today, and this may be why."
If readers are seeing similar traffic, please provide details in comments here.


Comments