Strange DNS Queries - Request for Packets
We have received a pcap sample of DNS queries that display a strange behavior. The queries are type ANY for domains ghmn.ru and fkfkfkfa.com. When doing a nslookup, both domains have 100 IPs listed under their domain names with each of them resolving exactly the same last octets (i.e. .1, .10, .100, etc). Queries with the same transaction ID are often repeated several times. The traffic samples we have received indicate the queries are sent by either a host or a server.
If anyone else is seeing queries for either of these domains or queries with a similar behavior and can share some pcap or logs, you can submit them via our contact page.
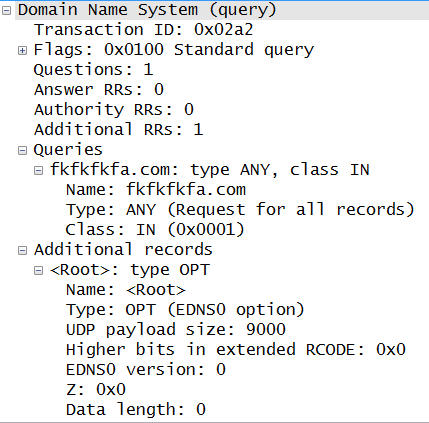
Wireshark example of a query:
Update 1:
Domain fkfkfkfa.com
We have received logs that indicate this behavior has been ongoing as early as 23 Sep 2013.
Domain ghmn.ru
We have received logs that indicate this behavior has been ongoing as early as 15 Dec 2013.
[1] https://www.robtex.com/dns/ghmn.ru.html#shared
[2] https://www.robtex.com/dns/fkfkfkfa.com.html#shared
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu
Adobe phishing underway
When thousands of access credentials and email addresses of Adobe customers were breached back in October, we expected that phishing attacks that make use of the stolen information would follow. Surprisingly, it seems to have taken the bad guys quite a while to kick off anything serious - the only mails we got so far on a compromised address that we converted into an Adobe phishing honeypot were the usual spam emails peddling the usual goods. But today, Adobe themselves issued a warning http://blogs.adobe.com/psirt/2013/12/20/alert-adobe-license-key-email-scam/ suggesting that something more nefarious must be going on. If you have a sample of this email, please share via our contact form.
Since the Adobe and now the Target breach both affected about 40 million people .. odds are that half a million or so might be on both lists. So if you are getting an email from "Target" on the email address that you used for Adobe, you might want to be extra careful, too ...



Comments