CSAM - Why am I seeing DNS Requests to IANA.ORG in my Firewall Logs?
As part of Cyber-Security Awareness month, one of our readers sent us an extract from their firewall logs. The events of interest where a regular pattern of internal hosts making DNS requests to a few hosts at iana.org.
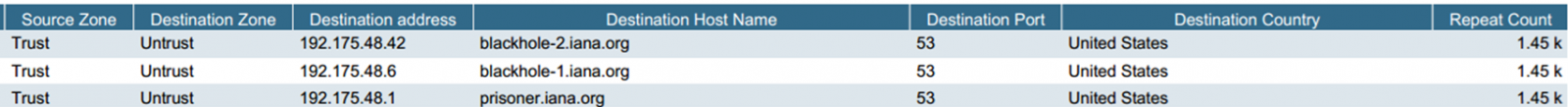
So in other words, thousands of outbound DNS Requests to internet hosts that aren't in any DNS or DHCP configuration inside the organization. What gives?
After a bit of searching, we found our answer in RFC6304 and RFC6305, also http://support.microsoft.com/kb/259922. I especially like RFC6305's title - "I'm Being Attacked by PRISONER.IANA.ORG!"
In plain english, when you don't have reverse DNS zones set up for your internal subnets, each individual workstation will attempt to register their reverse entry with these hosts at iana. It's just part of how DNS is architected, it's not specific to any one operating system vendor (so it's not "a windows thing").
The solution? Configure reverse DNS zones for each zone inside your organization.
While reverse DNS zones have great applications for penetration testers, they are also *very* desirable for a lot of "legit" reasons:
- It helps you identify hostnames from ip addresses that might show up in your firewall and other logs (this is a big one)
- It helps in defining Active Directory "Sites", which will in turn allow you to optimize Domain Controller type queries. For instance, creating sites for each remote office location in an organization will allow workstations to authenticate to domain controllers in their local office, rather than chewing up WAN bandwidth to authenticate against Domain Controllers at head office.
What other "sysadmin" uses do you routinely use reverse DNS for? Please let us know using our comment form.
===============
Rob VandenBrink
Metafore
VMware Release Multiple Security Updates
VMware released the following security updates. The first one is VMSA-2013-0012 which address multiple vulnerabilities in vCenter Server, vSphere Update Manager, ESXi and ESX. [1]
The second is VMSA-2013-0006.1 which address multiple vulnerabilities in vCenter Server Appliances and vCenter Server running on Windows. [2]
The last is VMSA-2013-0009.1 which address multiple vulnerabilities in vCenter Server, ESX and ESXi that updates third party libraries. [3]
[1] http://www.vmware.com/security/advisories/VMSA-2013-0012.html
[2] http://www.vmware.com/security/advisories/VMSA-2013-0006.html
[3] http://www.vmware.com/security/advisories/VMSA-2013-0009.html
-----------
Guy Bruneau IPSS Inc. gbruneau at isc dot sans dot edu


Comments