Upswing in port 23/TCP scanning
Reader Tom wrote in that he has noticed an upswing of scanning for port 23/TCP to a honeypot system. They are completing the 3 way handshake, then sending a FIN to shut it down. Dshield data confirms that others are seeing the same. 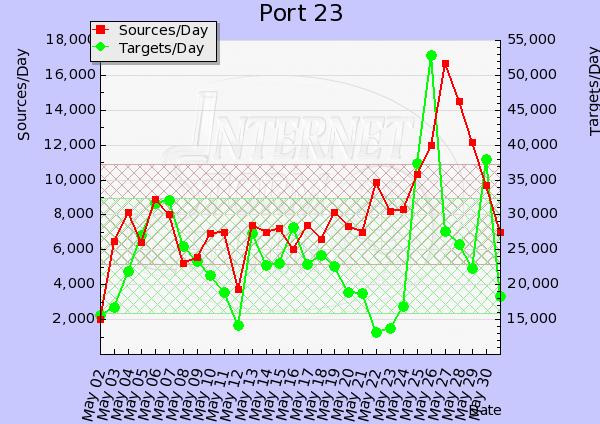 Let us know if you are seeing anything interesting at our contact us page.
Let us know if you are seeing anything interesting at our contact us page.
Cheers,
Adrien de Beaupré
Intru-shun.ca Inc.
SPF how useful is it?
Chris wrote in and mentioned a talk at Auscert which highlighted that (Sender Policy Framework) SPF would have helped in the instance of an intrusion and suggested a diary outlining some of the things that can and can't be achieved using SPF. I have my own experiences with SPF and the effectiveness, but I'd like to hear you experiences with SPF, good or bad. so I can write a more complete diary on the topic.
For those that are not familiar with SPF. The idea behind it is to create a DNS entry that specifies those machines in your network that are allowed to send email from your domain. The receiving mail server checks this record and if it does not match it will drop the message. There is a little bit more to it, but hat is the crux of it. So if you have had any experiences with SPF (good or bad) please let me know via the contact form or directly markh.isc at gmail.com.
Thanks Chris for the idea and thanks in advance for your contributions. I'm aiming to get a diary out on this later this month.
Cheers
Mark H


Comments